The optional function was launched no cost to consumers in a technical preview this week, adding a new layer of security to services, which has been plagued by privacy considerations.
Good doorbell maker Ring is providing cybersecurity critics considerably less to gripe about with the introduction of close-to-stop encryption to quite a few of its styles. Ring merchandise, which have been a juggernaut results with consumers, have confronted a litany of harsh criticism from cybersecurity professionals for what they say is a absence of interest to primary electronic security.
Soon after a a great deal predicted reaction to critics, Ring this week rolled out end-to-conclusion encryption for a lot of of its property security digicam products. Close-to-close encryption, in accordance to Ring, can be included to considerably less than 50 % of its in-use products and solutions. More mature design sensible-doorbell solutions, these types of as its very first and next-technology video doorbells, simply cannot be upgraded with the extra security.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The go was predicted, but initiated afterwards than planned.
Complex particulars by the Amazon-owned business Ring ended up manufactured readily available on Wednesday (PDF) as component of a complex preview of the new security actions. Ring’s stop-to-close encryption plans was initial introduced in September and originally slated to be launched by the close of 2020.
The feature—which will be optional and totally free for customers—will permit only the machine approved and enrolled with the related Ring account to acknowledge and obtain the live Ring online video stream. If 3rd functions want to watch a recording or stream on yet another product, they will require obtain to an encryption vital saved on the mobile machine approved to perspective the stream.
It is unclear how legislation enforcements’ obtain to Ring doorbell feeds might be impacted – if at all.
Clamoring Critics
The corporation has faced many years of criticism for flaws in the process that opened online video and details gathered by the method to be stolen by threat actors. Continue to other critics blasted Ring for what they explained were the company’s possess dodgy details-assortment techniques.
Final year, Amazon patched a vulnerability in the Ring smart doorbell that could have allowed attackers to accessibility the owner’s Wi-Fi network credentials and possibly reconfigure the product to launch an attack on the household network.
A couple of times afterwards, five U.S. Senators demanded in a letter to Amazon CEO Jeff Bezos that Amazon disclose how it is securing Ring household-security machine footage–and who is authorized to entry that footage.
Final Oct, Ring elevated privacy hackles yet again when it unveiled the new Generally Residence Cam, a intelligent household security digicam drone that flies all-around homes having security footage of men and women within their possess residences. Due to Amazon’s presently questionable knowledge-collection practices, privacy advocates apprehensive that the footage could fall into the mistaken hands.
Front Door Mitigations
On Wednesday, Ring outlined how it would specifically deal with these worries. It mentioned Ring will add an excess layer of security and privacy in addition to Ring’s current encryption, which by default encrypts video clips when they are uploaded to the cloud and stored on Ring’s servers, the business claimed.
“With Conclusion-to-Close Encryption, shopper movies are further secured with an further lock, which can only be unlocked by a critical that is stored on the customer’s enrolled cell product, made so that only the purchaser can decrypt and check out recordings on their enrolled unit,” according to a Ring weblog write-up about the rollout.
Ring claimed the support offers end users “control and added selections for encrypting and decrypting their films and is designed so that no unauthorized 3rd party can accessibility person online video material,” in accordance to a whitepaper Ring posted on the net about the company.
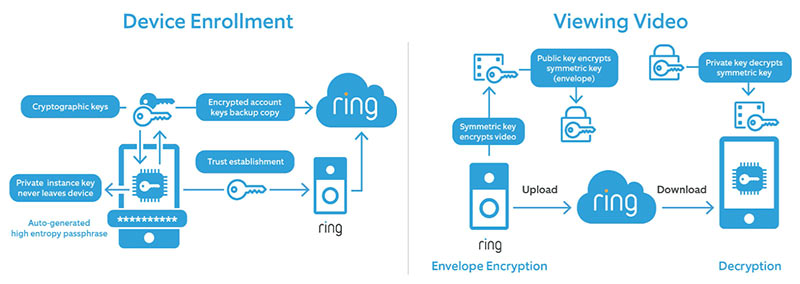
Ring Diagram of Stop-to-Conclusion Encryption Overview
Films encrypted when the feature is turned off will however be encrypted if the consumer decides to disable end-to-stop encryption, in accordance to the whitepaper, which also supplies stage-by-step recommendations about how the attribute works as nicely as distinct aspects about what kind of encryption the organization is utilizing.
Conclusion-to-conclusion encryption surely adds a layer of privacy that many prospects and privacy advocates have prolonged needed from Ring, which given that its inception has consistently pushed the boundaries of how substantially privacy individuals are ready to give up for house security security.
Subsequent Zoom’s Guide
The go to include conclusion-to-end encryption to Ring is comparable to a person that online videoconferencing assistance Zoom took previous calendar year to encrypt video streams amid privacy considerations and various security breaches of the service, these kinds of as Zoom bombing and zero-working day vulnerabilities, amongst other folks. Zoom, nonetheless, created the function out there to only paid people of the service.
When Ring’s new aspect has privacy and security advantages, it also will disrupt some current functions of the provider, this sort of as accessing Ring video by Alexa, and Echo Display or Fire Tv set product, or sharing with other cameras.
The encryption also may perhaps throw a wrench in controversial plans to use Ring’s Neighbors app to share information footage from Ring products with legislation enforcement, this sort of as what is happening in a method currently being examined by police in Mississippi in which they can livestream online video from Ring cameras put in at personal residences and businesses. When launched, the system sounded an alarm bell with privacy advocates like the Digital Frontier Foundation, which termed the launch of the method its “worst fears” staying “confirmed.”
Nevertheless, as the characteristic is optional and Ring consumers can choose to share encryption keys with 3rd functions, it will continue to be possible to each stream video to other equipment and share video streams with regulation enforcement if the operator of the machine so chooses.
Offer-Chain Security: A 10-Level Audit Webinar: Is your company’s software source-chain ready for an attack? On Wed., Jan. 20 at 2p.m. ET, begin identifying weaknesses in your source-chain with actionable guidance from authorities – portion of a constrained-engagement and Reside Threatpost webinar. CISOs, AppDev and SysAdmin are invited to question a panel of A-list cybersecurity gurus how they can prevent becoming caught uncovered in a article-SolarWinds-hack globe. Attendance is restricted: Sign up Now and reserve a location for this unique Threatpost Offer-Chain Security webinar – Jan. 20, 2 p.m. ET.
Some areas of this posting are sourced from:
threatpost.com


 Ring Rolls-Out End-to-End Encryption to Bolster Privacy
Ring Rolls-Out End-to-End Encryption to Bolster Privacy