Cyberattackers are actively exploiting regarded security vulnerabilities in greatly deployed, mission-critical SAP applications, permitting for entire takeover and the skill to infest an corporation even further.
Lively cyberattacks on recognized vulnerabilities in SAP programs could guide to whole handle of unsecured SAP programs, scientists are warning.
Adversaries are carrying out a assortment of attacks, according to an notify from SAP and security company Onapsis issued Tuesday – such as theft of sensitive data, economical fraud, disruption of mission-critical organization procedures and other operational disruptions, and delivery of ransomware and other malware.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
SAP apps help companies take care of critical company processes – which includes enterprise source planning (ERP), product lifecycle management, purchaser romantic relationship management (CRM) and offer-chain management.
From mid-2020 until finally these days, Onapsis scientists have recorded additional than 300 prosperous exploit attempts on unprotected SAP cases.
Who’s at Risk?
Sad to say, the ongoing attacks could have significantly-achieving consequences, as SAP mentioned in the warning:
“These are the applications that 92 percent of the Forbes World 2000 have standardized on SAP to electricity their operations and fuel the worldwide economic climate,” the warn famous. “With far more than 400,000 organizations working with SAP, 77 % of the world’s transactional earnings touches an SAP technique. These businesses incorporate the wide the vast majority of pharmaceutical, critical infrastructure and utility providers, food items distributors, defense and quite a few much more.”
Authorities organizations must consider individual see of the spate of attacks, researchers said.
“SAP programs are a well known attack vector for bad actors,” Kevin Dunne, president at Pathlock, informed Threatpost. “Most federal businesses are operating on SAP, as it has grow to be the field standard for government entities. On the other hand, these SAP implementations are usually on-premise, and managed by the govt entities them selves thanks to security worries. These techniques then turn out to be progressively vulnerable when updates and patches are not applied in a well timed trend, leaving them large open for fascinated hackers.”
The technology sector is a different hot goal for attacks, according to Setu Kulkarni, vice president of technique at WhiteHat Security.
“Our reporting has found that impartial software package suppliers (ISVs) and technology businesses have and inordinately high window of exposure,” he instructed Threatpost. “We are looking at that ISVs and technology organizations are missing in their security rigor as they in the long run may perhaps move on the security duties to the businesses that use the ISV to develop solutions for their clients.”
Active Exploitation
The attacks are brute-forcing large-privilege SAP person accounts, as perfectly as exploiting a raft of regarded bugs: CVE-2020-6287, CVE-2020-6207, CVE-2018-2380, CVE-2016-9563, CVE-2016-3976 and CVE-2010-5326, in accordance to the warning.
The adversaries are “advanced risk actors,” according to Onapsis, as evidenced by how immediately they’ve been able to create exploits, among other issues.
There is “conclusive proof that cyberattackers are actively focusing on and exploiting unsecured SAP purposes, through a various set of methods, resources and treatments and obvious indications of advanced expertise of mission-critical apps,” the warn reads. “The window for defenders is substantially smaller than beforehand believed, with illustrations of SAP vulnerabilities currently being weaponized in significantly less than 72 hrs given that the launch of patches, and new unprotected SAP applications provisioned in cloud (IaaS) environments being identified and compromised in significantly less than three several hours.”
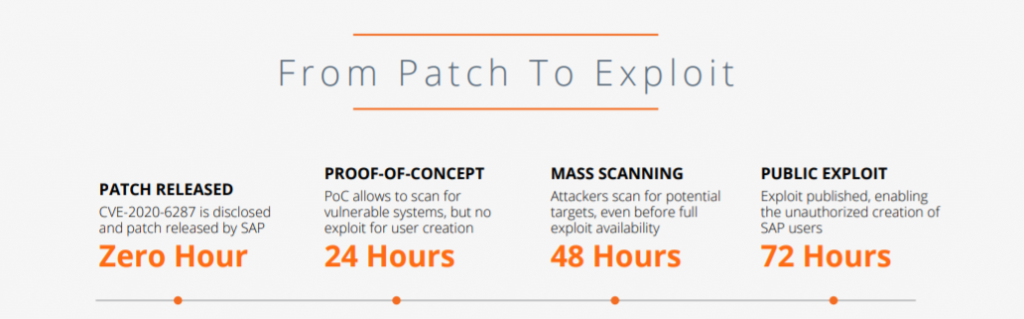
Resource: Onapsis.
The issues are as follows:
- CVE-2020-6287 is a critical authentication bypass issue in SAP NetWeaver Software Server Java allowing comprehensive account takeover
- CVE-2020-6207 is one more critical authentication bypass bug, in SAP Remedy Manager
- CVE-2018-2380 is a medium-severity flaw in SAP CRM, which enables an attacker to exploit inadequate validation of path information offered by end users
- CVE-2016-9563 is also a medium-severity bug, this time in SAP NetWeaver AS Java. Remote authenticated users can exploit it to carry out XML External Entity (XXE) attacks, which let them to interfere with XML processing
- CVE-2016-3976 is a substantial-severity directory traversal vulnerability in SAP NetWeaver AS Java that enables distant attackers to go through arbitrary data files
- And CVE-2010-5326 is an 11-yr-previous critical issue in the Invoker Servlet on SAP NetWeaver AS Java. It does not have to have authentication, which makes it possible for distant attackers to execute arbitrary code by using an HTTP or HTTPS ask for.

Exploit works by using – simply click to enlarge. Supply: Onapsis.
Following initial entry, Onapsis observed threat actors making use of the vulnerabilities to build persistence, for privilege escalation, evasion and, eventually, total regulate of SAP techniques, like financial, human money management and provide-chain apps.
“Additionally, makes an attempt at chaining vulnerabilities to reach privilege escalation for OS-level entry ended up observed, expanding possible influence further than SAP devices and programs,” according to the analysis.
As an example, Onapsis mentioned that a single actor was capable to scan and generate an admin person making use of an exploit utility for CVE-2020-6287. Upon productively producing the profile and logging in, more exploits had been executed from CVE-2018-2380 for shell upload, as the attackers tried using to entry the working process layer. Pursuing that, exploits for CVE-2016-3976 had been executed, targeting the down load of a “credential retail outlet,” which offers accessibility to logins for large-privileged accounts and the main database. Worryingly, this all occurred in 90 minutes, in accordance to Onapsis.

Exploit chaining. Supply: Onapsis.
Interestingly, the cyberattackers in some scenarios are patching the exploited vulnerabilities immediately after they’ve gained access to a victim’s setting, Onapsis stated.
“This motion illustrates the threat actors’ sophisticated area knowledge of SAP apps, entry to the manufacturer’s patches and their capacity to reconfigure these devices,” according to the agency. “This system is normally utilized by menace actors to deploy backdoors on seemingly patched techniques to keep persistence or to evade detection.”
Who’s Behind the SAP Attacks?
The activity is getting mounted by a number of groups, who appear to be engaged in coordinated action across huge swathes of infrastructure, according to the warn.
“Attackers [are] triggering exploitation from distinctive supply techniques from the kinds utilised to conduct subsequent handbook logins were being detected, indicating the likelihood of coordinated groups and/or actors leveraging huge-distribute attack infrastructure,” it reads. “While this actions is frequent when examining working procedure and network-centered attacks, this knowledge provides evidence that the same strategy is also made use of when targeting mission-critical programs, as these actors use TOR nodes and dispersed VPS infrastructures to launch the attacks and escalate privileges.”
The activity is originating from all over the environment, such as Hong Kong, India, Japan, the Netherlands, Singapore, South Korea, Sweden, Taiwan, United States, Vietnam and Yemen.
How Can I Avert an Attack?
The principal way to thwart these kinds of attacks is to patch the vulnerabilities. Also, any web-experiencing accounts must have exceptional passwords to disallow automated brute-force attempts to split in and any devices that do not want to encounter the general public web should really be taken offline.
“All noticed exploited critical weaknesses have been instantly patched by SAP, and have been out there to consumers for months and many years in some circumstances,” the alert noted. “Unfortunately, both equally SAP and Onapsis keep on to notice lots of organizations that have even now not applied the proper mitigations…allowing unprotected SAP methods to continue on to operate and, in quite a few conditions, continue being seen to attackers by using the internet.”
Also, when applying security patches in a timely style is critical to closing down the risk from main, known SAP vulnerabilities. However, Pathlock’s Dunne pointed out that patching can only treatment issues that are in the rear-check out. With cyberattackers patching the bugs powering them, there also wants to be a way to detect malicious action.
“For a detailed, ahead searching method to SAP security, corporations will need to implement a thorough alternative to check person activities within just the procedure, such as interactions with sensitive info,” he advised Threatpost. “This way, even attackers that are capable to breach SAP methods by identified or unidentified vulnerabilities can nevertheless be determined and their destruction can be mitigated in genuine-time.”
Check out out our free upcoming reside webinar events – exceptional, dynamic discussions with cybersecurity professionals and the Threatpost group:
- April 21: Underground Marketplaces: A Tour of the Dark Economic system (Find out a lot more and sign-up!)
Some sections of this write-up are sourced from:
threatpost.com

 Parrot Launches Bug Bounty Program
Parrot Launches Bug Bounty Program