Some security researchers say it is really Cobalt Strike and not a SmokeLoader variant, but BioBright states in-depth screening shows it is for true a frightening morphic malware that changes its parts and recompiles alone.
An APT has attacked two independent vaccine brands this 12 months employing a shape-shifting malware that seems at initial to be a ransomware attack but afterwards reveals to be far far more innovative, researchers have observed.
Dubbed Tardigrade by the Bioeconomy Information Sharing and Examination Centre (BIO-ISAC), the attacks employed malware that can adapt to its setting, conceal itself, and even run autonomously when minimize off from its command-and-control server (C2), in accordance to a new advisory unveiled by BIO-ISAC.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The first attack was detected at a “large biomanufacturing facility” in April, with investigators identifying a malware loader “that demonstrated a higher degree of autonomy as perfectly as metamorphic abilities,” according to the advisory. In Oct 2021, the malware was detected at a second facility as effectively.
“Due to the advanced traits and ongoing unfold of this lively menace, BIO-ISAC created the conclusion to expedite this danger advisory in the public fascination,” the center mentioned in its advisory. Investigators go on to review the attacks and will release additional data when it’s accessible, the heart explained.
Having said that, for now, “biomanufacturing web pages and their partners are inspired to assume that they are targets and choose vital steps to evaluate their cybersecurity and response postures,” the centre warned.
Without a doubt, there have already been a amount of attacks targeting the COVID-19 vaccine initiatives since the pandemic started, and they are likely to proceed, security researchers warned.
In October 2020, Dr. Reddy’s, the contractor for Russia’s “Sputinik V” COVID-19 vaccine and a important generics producer, had to near crops and isolate its facts facilities after a cyberattack. Two months later on, in December, threat actors broke into the European Medications Agency (EMA) server and accessed documentation about the vaccine applicant from Pfizer and BioNTech.
Malware Behavior
According to BioBright, a biomedical and cybersecurity organization and BIO-ISAC member, researchers established that the malware made use of in the Tardigrade attacks is a variant of the SmokeLoader loved ones with metamorphic capabilities. SmokeLoader is a generic backdoor with capabilities that vary based on which modules are included.
The variant would seem specifically clever in that it can modify its properties relying on its ecosystem, investigators noticed. Even though former SmokeLoader versions scientists have found have been externally directed by C2 infrastructure, the variant utilized in the Tardigrade attacks “is much additional autonomous” and can direct its own lateral motion, according to BIO-ISAC.
The malware also can elevate its privilege to the greatest level promptly by impersonating a customer system, according to the advisory.
Researchers also noticed SmokeLoader sending encrypted visitors to a C2 IP tackle in the attacks, suggesting information exfiltration, they mentioned.
Is It Seriously a New Malware, or Cobalt Strike?
Some security researchers questioned BIO-ISAC’s report and its technical details. Precisely, they doubted BioBright researchers’ identification of an intserrs644.dll file submitted to VirusTotal as remaining the new Tardigrade malware/SmokeLoader variant. They told BleepingComputer that the DLL file was, relatively, a Cobalt Strike beacon and that it has no relation to SmokeLoader.
On Monday, BioBright CEO Charles Fracchia advised Threatpost that the assertions are incorrect: “We now have next- and 3rd-party confirmation that we are correct,” he said in an job interview, explaining that the disagreement over the malware’s identification boils down to the disparate confidence degrees of automatic resources. “I’m a tiny astonished that people would hurry to the conclusion [that the malware is Cobalt Strike] with a 50 per cent self confidence level [from VirusTotal, et al.].”
(As of Monday, BioBright was even now coordinating disclosure of the cyber incident reaction groups that confirmed its results but said that one particular is a “well-known cyber incident response crew.”)
BioBright’s “in-depth testing” has demonstrated that the malware isn’t Cobalt Strike, he claimed. “This is no run-of-the-mill ransomware. It’s a additional sophisticated version that could have arisen from SmokeLoader [we assess with] probably a 65 percent assurance amount.”
Any individual beloved this malware, Fracchia claimed: They “spent a whole lot of time, income and hard work to make this sophisticated” code, he advised, pointing to the metamorphic excellent as the “really frightening bit.”
The variation amongst metamorphic and polymorphic is in the compiled artifact, he discussed. Most anti-virus operates off signatures to determine malware these as Cobalt Strike. To evade that identification, malware engineers do a person of two issues: They either use polymorphism, scrambles the code bundle with encryption in a semi-random way, working with various keys for encryption so that the bundle seems different and evades anti-virus detection or they use the extremely unique procedure of metamorphism, which changes constituent pieces of the malware and recompiles by itself.
“That’s substantially much more bleeding edge,” he claimed. “That’s from the top rated shelf of equipment.”
BioBright researchers are nonetheless hoping to unravel how it does that, Fracchia reported, but it’s obvious that Tardigrade has some really state-of-the-art morphic habits. “We caught a very sophisticated device, so – ya,” he reported.
Warning to Companies
The attacks are a warning to vaccine manufacturers that risk actors are turning into much more targeted on their efforts to cripple critical enterprise sectors, which biomanufacturing has in truth come to be through the COVID-19 pandemic, security pros stated.
The race to establish and certify vaccines has eclipsed the risk of cyber-attacks on the services included, but it is imperative that they don’t let their guard down, noticed Saryu Nayyar, CEO of security business Gurucul.
“The reduction of vaccine production functionality could be regarded a weapon, hurting our capability to battle COVID-19,” she reported in an e-mail to Threatpost. “These manufacturers have to be capable to detect malware these as Tardigrade and remediate just before it does considerable harm.”
Nevertheless there isn’t immediate proof to verify that the Tardigrade attacks ended up especially specific from the vaccine effort and hard work, their complexity and sophistication displays that hyper-vigilance versus any form of attack is required in the sector, mentioned an additional security professional.
“The authentic position is all of our sources are currently being scanned for vulnerabilities and malware is making an attempt to be inserted anywhere an opening offers alone to the attackers,” said Garret Grajek, CEO of security agency YouAttest.
Supplemental reporting by Lisa Vaas.
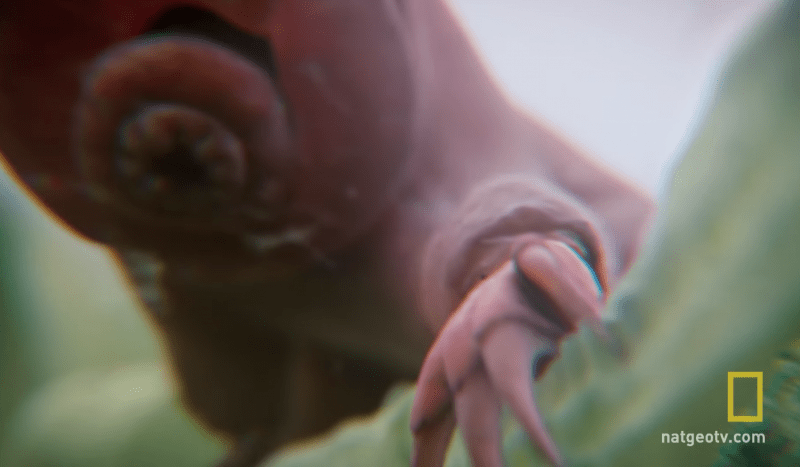
Illustration courtesy of nationalgeotv.com online video.
There is a sea of unstructured details on the internet relating to the most current security threats. Sign-up Now to find out important concepts of all-natural language processing (NLP) and how to use it to navigate the data ocean and add context to cybersecurity threats (with no remaining an professional!). This Stay, interactive Threatpost City Hall, sponsored by Immediate 7, will attribute security scientists Erick Galinkin of Immediate7 and Izzy Lazerson of IntSights (a Speedy7 business), additionally Threatpost journalist and webinar host, Becky Bracken.
Some components of this post are sourced from:
threatpost.com

 Sabbath hackers are targeting US schools and hospitals
Sabbath hackers are targeting US schools and hospitals