With several in the public sphere warning about a opportunity compromise of the integrity of the Presidential Election, security researchers as an alternative flag on line methods and affect campaigns as the largest trouble areas.
With the 2020 U.S. Presidential Election coming up in just two months and transform, cybersecurity considerations have occur to the fore for normal citizens and politicians alike. That said, the probability of election results being impacted by an attack is fairly slender, in accordance to security scientists. In its place, there is a myriad of other at-risk election infrastructure that absolutely everyone need to be having to pay interest to.
When it comes to election security, problems about the integrity of voting machines normally pop to intellect, and the predicted growth of mail-in voting due to COVID-19 has also sparked worries. Past direct hacking initiatives, these kinds of as the attack on the Democratic National Committee in 2016, have remaining many nervous that this time about, the true election effects could be compromised in some way.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The worry that anyone could modify or delete election results specifically is a little bit of a tempest in a teapot, in accordance to researchers.
“Most voting machines in use nowadays, from the effectively-known market leaders, are ‘reasonably’ safe from cyberattacks because of to the actuality that the terminals are typically air-gapped from any related network in the course of the person voting system,” Invoice Rials, associate director and professor of apply of the Tulane University School of Professional Advancement Information and facts Technology Method, advised Threatpost. “Any vote forged is normally saved regionally and not transferred around a network right until after the polls shut and the tabulation takes place. From a cybersecurity perspective, the most important risk to elections is all the ancillary aspects associated with the election method.”
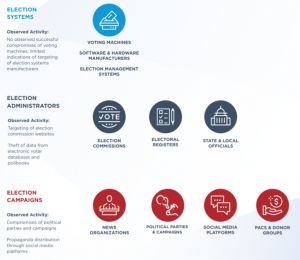
All those ancillary elements involve the availability of condition and neighborhood voter registration internet sites and other assist infrastructure, safeguarding campaigns’ delicate info and thwarting nation-state-backed impact strategies.
“We observed with the U.S. presidential cycle in 2016 that there were some makes an attempt to most likely gain some accessibility into election voting techniques them selves and ballot programs, but the most significant impression we observed was the targeting of campaigns, the targeting of candidates, and not just specially of the parties but also ancillary groups encompassing these candidates and events,” stated Ron Bushar, SVP and CTO, Govt Methods Consulting at Mandiant, talking at the current FireEye Virtual Summit. “Those hacking endeavours, in particular if they are timed effectively, can definitely have devastating effects on the perception of a voting technique by the folks taking part in that election.”
Voting systems by themselves ordinarily have double- or triple-redundancy when it will come to the election returns.

Credit score: Black Hat United states of america
“Many states mandate that paper ballots have to be taken care of, and you have usually two or three different copies of the digital success bodily stored in just the programs,” Bushar said. “And then of course, you have the digital copies that are that are despatched out. And in every single instance, the certification of these votes has to be finished by way of a manual procedure, even soon after first results are in. So from our standpoint, whilst individuals obviously are the most significant methods in the voting ecosystem, and they are unquestionably targeted, it is incredibly, extremely hard to affect the end result of an election by hacking the final results.”
In the meantime, current stats from the Black Hat United states of america 2020 Attendee Survey exhibit that 85 p.c of respondents imagine that cyber-menace actors will have at least some effects on the U.S. elections in 2020. And disturbingly, just about one particular 3rd of respondents believe that the effect will be critical, and that the effects of the 2020 election will always be in question as a final result.
Focusing on Election Sources
A single of the weak hyperlinks to be concerned about is the availability of the on the web means that enable citizens to sign-up to vote, discover polling locations or discover far more about candidates, according to new data — as very well as the IT systems utilised by state and community workplaces. Problems in this arena can be a lot more impactful than it would appear to be on the floor, especially when it comes to securing the voter rolls to prevent tampering and voter suppression.
“Due to the distribute of COVID-19, we are looking at a variety of election environments change on-line, to different levels, with political get-togethers conducting virtual fundraisers, campaigns relocating city halls to on the net platforms and election officials applying on the internet varieties to aid voting by mail,” explained Jocelyn Woolbright, a researcher with Cloudflare, who additional that cybercriminals are more and more concentrating on these methods.

Credit rating: Cloudflare
From April to June, Cloudflare saw a development of raising DDoS attacks in opposition to political strategies, with double the amount assaults observed in its telemetry in comparison to the initial a few months of 2020. Over-all, political campaigns have been dealing with an typical of 4,949 cyber-threats for each day, while much larger campaigns are viewing a lot of more than that, in accordance to the examination. This is problematic provided that strategies now depend on on the internet platforms like videoconferencing, on the net fundraising and social media to arrive at voters.
“When searching at the ecosystem of election security, political strategies can be smooth targets for cyberattacks due to the lack of ability to dedicate assets to advanced cybersecurity protections,” Woolbright explained. “Campaigns are typically brief-expression, income strapped functions that do not have an IT personnel or spending budget necessary to market lengthy-time period security tactics.”
For condition and community governments, constituents are accessing on the web information about voting processes and polling stations in significantly larger sized quantities of late – Cloudflare reported that it has observed boosts in website traffic ranging from two to 3 times the typical volume of requests considering the fact that April. So potentially it is no coincidence that the company found that governing administration election-similar websites are going through a lot more tries to exploit security vulnerabilities, with 122,475 these types of threats coming in per working day (like an average of 199 SQL injection attempts per working day bent on harvesting information and facts from web site guests).
“We believe there are a vast range of things for visitors spikes like, but not restricted to, states increasing vote-by-mail initiatives and voter registration deadlines thanks to unexpected emergency orders by 53 states and territories all over the United States,” Woolbright mentioned.
Mandiant’s Bushar included that cyberattackers have also been focusing on the IT infrastructure made use of by commissions and the boards of election, and the organization laptop or computer methods, email and other again-office environment equipment which is utilized both of those at the condition and the county/neighborhood degrees for the administration of elections. A person primary problem on this front is securing the availability and integrity of the voter registration databases on election day.
Tulane’s Rials famous that these voter registration databases are ordinarily stored and managed by county clerks and election commissioners.
“These databases are prone to cyberthreats, just like any other databases,” he famous. “Unfortunately, a lot of regional governments are nevertheless having difficulties to increase their cyber-defense abilities and are uncomplicated targets. Cybercriminals wishing to disrupt the election procedure are probable focusing on these voter-registration databases months and even years major up to election day. Incorrect or modified voter data could have an effect on the election procedure. Community governments who are liable for the cyber-security of these databases must be functioning now to strengthen the cybersecurity posture affiliated with the voter databases.”
In phrases of best procedures for thwarting these forms of assaults, there are foundational attempts for what an corporation can do, starting with creating a created information-security software and incident-response plan, in accordance to Ben Woolsey, manager at Mandiant.
Credit score: FireEye
“Not only need to they have a systematic technique to how to deal with an incident, but how to exclusively tackle unique incidents based on intelligence about what threats are out there,” he famous, for the duration of the FireEye Virtual Summit. “Then, have you practiced that? Schooling as an training is exceptionally critical.”
Corporations should also consider periodic wellness checks top up to the up to the day of the election, with improved hunting and checking efforts kicking in two months out, he mentioned.
“Not just hunting for easy signatures and hash values but looking for evidence of the practices, methods and treatments (TTPs) applied by country-condition adversaries and other important teams,” Woolsey claimed.
And eventually, on the day of the election, corporations need to have a war space, irrespective of whether virtual or on-premise, populated with a designated executive in charge, malware analysts and incident-response professionals — in scenario attackers attempt to mount a DDoS or ransomware attack on campaigns or election infrastructure — or worse.
“The dream of the war area is to have just one of the most boring times of your lifestyle,” Woolsey said. “You appear in early in the morning, you sit there, nothing at all transpires. And then the war place gets stood down after the after the vote is counted. That is the great War Place situation.”
Companies may possibly get outside assist way too: Christopher Krebs, director of the Cybersecurity Infrastructure and Security Agency (CISA), explained at Facts Security Media Group’s Cybersecurity Digital Summit this 7 days that the Feds will offer regional and condition federal government election officials complex aid, training and cyber-hygiene physical exercises required to assure a far more protected election in November. Also, the U.S. governing administration is featuring a reward of up to $10 million for any person providing facts that could direct to tracking down opportunity cybercriminals aiming to meddle in the November contest.
Country-State Actors and Social Affect
Point out-sponsored cyberattackers go on to be a bugbear for election security. But although direct hacking exercise remains a issue, nation-state meddling is far more likely to consider the sort of spreading divisiveness and disinformation — largely by means of online social-media bots and troll farms.
“In the midterm elections, the only matter we noticed was disinformation and social-media manipulation there was pretty little targeting of other elements, and there was no big hacking and leaking of candidates or campaigns or parties,” Bushar claimed, introducing that these types of exercise has been small in 2020 as very well. “But as to what is likely to transpire this this go all-around, it is tough to say.”

Credit: Black Hat United states
In the Black Hat attendee study, far more than 70 percent explained affect campaigns will have the greatest influence on the elections. As keynote speaker Renée DiResta, exploration supervisor at the Stanford Internet Observatory, detailed at the present, the anatomy of these assaults has develop into relatively normal. There is first the generation of 1000’s of phony-personae accounts. Then there is the development of material, which is seeded to social platforms. Following, doubtful news web sites deliver plausible — but bogus — articles or blog posts that amplify a main message. If successful, the viral mother nature of the “news” piques the curiosity of mass-media information web sites. They acquire the bait and report on the viral “news” as simple fact.
“It gets truly tough to attempt to discern among respectable speech, political speech and what becomes phony information or amplification of faux information,” Bushar stated. “Espionage and traditional data theft is definitely also a play here, specially on the candidates and the events. Which is either for purposes of comprehension how to mount a social-media disinformation campaign, or to get parts of respectable details that were being stolen, incorporate that with other pretend news or untrue data, and produce a strong narrative that can genuinely obtain traction – that is challenging to counter.”
When it will come to the adversaries concerned, about 69 % of Black Hat study respondents explained they count on disinformation initiatives to emanate mainly from Russia.
“One of Russia’s vital goals is to additional deepen divides in the populace, irrespective of whether that is with Brexit in the British isles or with gun command or Black Lives Matter in the U.S.,” claimed Duncan Hodges, senior lecturer in Cyberspace Operations at the U.K.’s Cranfield University, by using email. “For them, it is minimal work, so any obtain is valuable and can help weaken the West, E.U. and NATO, this not only structurally gains Russia but is significant for the domestic populace at residence in Russia.”
Russia isn’t by yourself in mounting influence strategies, on the other hand: China, Iran and other individuals have also set sizeable means into this sort of efforts.
“Beyond the Russia menace, which has been rather properly-documented, there are numerous illustrations of Chinese cyberespionage [in service to influence campaigns],” Bushar stated. “Iran has a fewer direct target on individual election campaigns, but they’re really, extremely energetic in the bogus persona disinformation, and are specifically really energetic on platforms such as Fb. They develop hundreds or 1000’s of bogus accounts and really amplify news stories that are definitely pro-Iranian. We haven’t witnessed them focusing on any distinct elections units or election infrastructure still.”

Credit rating: Black Hat
Many moments, these influence strategies are extremely focused. For instance, scientists at GroupSense not long ago discovered evidence that international actors are planning to target Indigenous Us residents for the 2020 election.
“They’re currently setting up troll accounts on Fb, Twitter and Instagram, and building a base of followers to prepare for long run disinformation campaigns,” Kurtis Minder, CEO of GroupSense, claimed by using email. “Some of the states with the premier Native American populations are also battleground states: Arizona, Michigan, North Carolina, Florida, Texas and Wisconsin. And, as we saw in Michigan, the place the vote differential was 11,000 in 2016, it doesn’t get substantially to suggestion a near election (there are 50,000 Indigenous Americans in Michigan, by the way).”
Social-media giants have labored to minimize the means of country-condition actors to user their platforms for these campaigns: Twitter in June in actuality took down three different country-sponsored influence functions, attributed to the People’s Republic of China (PRC), Russia and Turkey. Collectively the functions consisted of 32,242 bogus or bot accounts producing the information and many amplifier accounts that retweeted it. Nevertheless, much more wants to be completed.
“We have to coordinate on the identification of pretend accounts,” Mandiant’s Bushar claimed. “False personas, false information stories, there has to be a partnership of government intelligence-sharing with critical infrastructure vendors and state and local governments to make guaranteed they have all the visibility they can maybe get to protect in opposition to these threats.”
It is the age of distant operating, and firms are facing new and even bigger cyber-challenges – whether it’s collaboration platforms in the crosshairs, evolving insider threats or issues with locking down a a great deal broader footprint. Obtain out how to tackle these new cybersecurity realities with our complimentary Threatpost E book, 2020 in Security: 4 Stories from the New Menace Landscape, introduced in conjunction with Forcepoint. We redefine “secure” in a operate-from-home planet and supply compelling authentic-world finest procedures. Click here to obtain our E-book now.


 Eight Million Freepik People Go through Facts Compromise
Eight Million Freepik People Go through Facts Compromise