Scientists say that the marketing campaign sidesteps finish person detection and security answers.
Spammers have commenced utilizing a challenging URL obfuscation approach that sidesteps detection – and finally infects victims with the LokiBot trojan.
The tactic was uncovered in the latest spear-phishing e-mails with PowerPoint attachments, which contain a malicious macro. When the PowerPoint file is opened, the document makes an attempt to entry a URL by using a Windows binary (mshta.exe), and this leads to many malware remaining set up on to the system.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
This method is not unconventional for macro downloaders. On the other hand, since the domains related with the marketing campaign are now regarded to host destructive data files and knowledge, the attackers employed a exceptional semantic attack on the campaign’s URLs to trick the email receiver and avoid remaining flagged by email and AV scanners. A semantic URL attack is when a consumer manually adjusts the parameters of its request by preserving the URL’s syntax – but altering its semantic that means. More on that, underneath.
“We located it exciting that the attackers were being using URIs in this way, which in essence is an attack on the user’s preconceived idea of what a URI must glance like,” claimed scientists with Trustwave in a Thursday report. “It may well also defeat security remedies, which may possibly be expecting URIs in a certain structure.”
The malicious email that was observed by researchers is titled: “URGENT: Request FOR Offer (University of Auckland)” and the connected PowerPoint is titled “Request For Offer you.” The College of Auckland is a community investigate college in Auckland, New Zealand. Threatpost has attained out to Trustwave for even more details on the targeting and entice of this attack.
Obfuscation Tactic
It’s critical to distinguish in between a URL compared to URI listed here. A URI is an identifier of a specific resource, such as a page, reserve or a document. A URL, meanwhile, is the most widespread style of URI that also tells users how to obtain it (such as HTTPs or FTP).
A URI is made up of a scheme, host and route. The plan identifies the protocol to be utilised to entry the useful resource on the internet, although the host identifies the host that holds the source, and the path identifies the certain useful resource in the host that the web shopper wishes to access.

The spear phishing email lure. Credit: Trustwave
The spammers powering this attack have horned in on a person ingredient of the URI scheme called an Authority ingredient, which retains an optional person-details section. If the “userinfo” subcomponent is current, it is preceded by two slashes and adopted by an “@” character. An case in point of this Authority framework is as follows: authority = [userinfo@]host[:port].
Because “userinfo” is not generally utilized, it is in some cases ignored by servers, scientists claimed. In this precise campaign, attackers took benefit of this fact, utilizing what scientists named a “dummy” userinfo in order to cover their legitimate intent.
The end end result is that at facial area price, stop people who simply click on the link might feel they are becoming led to one particular area, but the URL is actually for a further.
In this unique campaign, the URL applied (j[.]mp/kassaasdskdd) in fact utilizes a URL shortening support presented by Little bit.ly and sales opportunities to Pastebin, which is a website that lets consumers to share plain textual content by way of public posts referred to as “pastes.” Each the use of URL shortening expert services and Pastebin are typically leveraged by cybercriminals so to avoid staying characterized as a small URL and to evade detection signatures, the attackers repeatedly use a randomized, brief string (“%909123id”) in the userinfo portion of their URL (see image beneath).
Mainly because userinfo is not required to obtain entry to any methods, the userinfo information will be disregarded when the URL is accessed – which means that at facial area benefit, it is unclear that the URL is shortened, and will redirect the people to Pastebin despite security gates.
“The negative men are trying to make the domains unnoticeable nonetheless nevertheless conforming with the generic URI syntax,” said scientists.
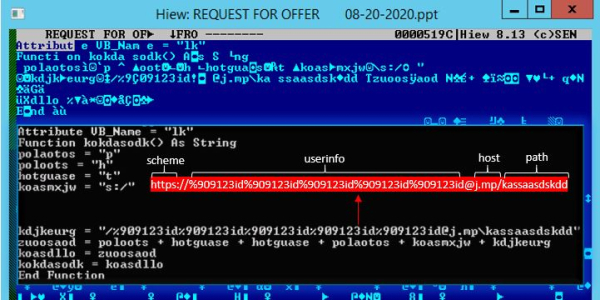
The PowerPoint attachment and its macro code in which the first destructive URL is formulated. Credit history: Trustwave
Researchers conducted a deeper evaluation of 4 URLs linked in the campaign. The to start with URL, accessed by the PowerPoint attachment, redirects to an obfuscated VBScript hosted on Pastebin. A second URL consists of VBScript, which is a dropper that writes a PowerShell downloader into the registry and sets up persistence, claimed researchers. This PowerShell then downloads and procedures the raw knowledge on two a lot more Pastebin URLs, and then executes the output binaries, they claimed.
The information at the third URL meanwhile contains an obfuscated PowerShell code, which then executes two DotNet compiled Dynamic Backlink Libraries (DLLs). These DLLs bypass the Windows Anti-Malware Scan Interface (AMSI) on the equipment, which is an interface typical allowing user apps and solutions to integrate with any anti-malware product or service on a device.
They then load a DLL injector into the memory. Finally, the very last URL includes an obfuscated malware LokiBot sample, which is injected into a legit system (notedpad.exe) by the aforementioned DLL injector.
LokiBot Malware
LokiBot is a prolific trojan that’s notorious for being very simple and successful with its capabilities to covertly steal info from compromised endpoints. It is at this time becoming dispersed in many forms that can hitch a ride inside other file formats—as is the scenario in the latest campaign. Different versions of LokiBot also in the previous had been offered on underground markets for as little as $300.
The new tactic will come just a week right after The U.S. Cybersecurity and Infrastructure Security Company (CISA) warned that LokiBot is observing a surge throughout the enterprise landscape. The uptick started in July, according to the company, and exercise has remained “persistent” ever considering the fact that.
“LokiBot has stolen credentials from multiple purposes and facts resources, which include Windows functioning technique credentials, email customers, File Transfer Protocol and Protected File Transfer Protocol clientele,” according to the warn, issued Tuesday. “LokiBot has [also] shown the capability to steal qualifications from…Safari and Chromium and Mozilla Firefox-primarily based web browsers.”
On Oct 14 at 2 PM ET get the most up-to-date facts on the growing threats to retail e-commerce security and how to stop them. Register today for this Cost-free Threatpost webinar, “Retail Security: Magecart and the Increase of e-Commerce Threats.” Magecart and other menace actors are riding the soaring wave of on-line retail usage and racking up significant numbers of client victims. Obtain out how internet websites can keep away from starting to be the upcoming compromise as we go into the holiday getaway year. Sign up for us Wednesday, Oct. 14, 2-3 PM ET for this LIVE webinar.
Some parts of this article is sourced from:
threatpost.com


 Technical and Cost Concerns of Passwordless Authentication Bother Security Leaders
Technical and Cost Concerns of Passwordless Authentication Bother Security Leaders