The out-of-bounds read vulnerability enables an attacker to escape a Squirrel VM in games with thousands and thousands of month-to-month players – this kind of as Counter-Strike: World Offensive and Portal 2 – and in cloud providers such as Twilio Electric powered Imp.
An out-of-bounds examine vulnerability in the Squirrel programming language allows attackers crack out of sandbox constraints and execute arbitrary code within a Squirrel virtual machine (VM), hence offering a destructive actor entire access to the underlying equipment.
Presented the place Squirrel lives – in online games and embedded in the internet of issues (IoT) – the bug probably endangers the hundreds of thousands of monthly players who perform movie game titles these types of as Counter-Strike: International Offensive and Portal 2, as perfectly as cloud services these as the Twilio Electrical Imp IoT platform, with its ready-to-use open-resource code library.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Squirrel is an open-source, object-oriented programming language used by video online games and cloud expert services for customization and plugin advancement. It is a light-weight scripting language that satisfies the dimension, memory bandwidth and serious-time demands of programs like video online games and embedded programs.

Both of those of the online games stated above use the Squirrel Engine recreation library to enable everyone to produce customized match modes and maps.
Tracked as CVE-2021-41556, the Squirrel out-of-bounds read through vulnerability can be exploited when a Squirrel Motor is utilized to execute untrusted code, as it is with Twilio Electrical Imp or specific online video game titles.
The vulnerability was learned by SonarSource and in depth in a submit published on Tuesday. In that writeup, vulnerability scientists Simon Scannell and Niklas Breitfeld instructed a serious-globe state of affairs in which an attacker could embed a malicious Squirrel script into a local community map and distribute it through the trusted Steam Workshop: a mod repository for Steam Games that lets creators upload their mods for a large constructed-in viewers when furnishing regular players with an straightforward way to receive mods.
“When a server proprietor downloads and installs this malicious map onto his server, the Squirrel script is executed, escapes its VM, and can take command of the server machine,” the researchers discussed.
The security flaw problems an “out-of-bounds obtain through index confusion” when defining Squirrel classes. “The truth that bitflags are set within just indexes is problematic as it is fully doable for an attacker to produce a course definition with 0x02000000 techniques,” the researchers spelled out. They produced the adhering to, “very simple” proof of strategy (PoC): just a nibble’s well worth of code that could be exploited to hijack a method and grant an attacker full manage of the Squirrel VM.

Proof of principle. Source: SonarSource.
“The rawset and rawget functions allow for us to handily accessibility customers of a supplied course,” in accordance to the examination. “In this PoC, the squirrel interpreter will dereference a null pointer and segfault because the _defaultvalues array has not been allocated nonetheless.”
An attacker could bring about the vulnerability by:
The vulnerability is dangerous mainly because a malicious actor could established up a fake array that could examine and publish values. By performing so themselves, the scientists identified they could “hijack the control movement of the application and acquire comprehensive manage of the Squirrel VM,” which they did by overwriting function tips.
SonarSource delivered the next chart, which shows the chain of attacker-controlled pointer that enabled reading and composing to the full address room:
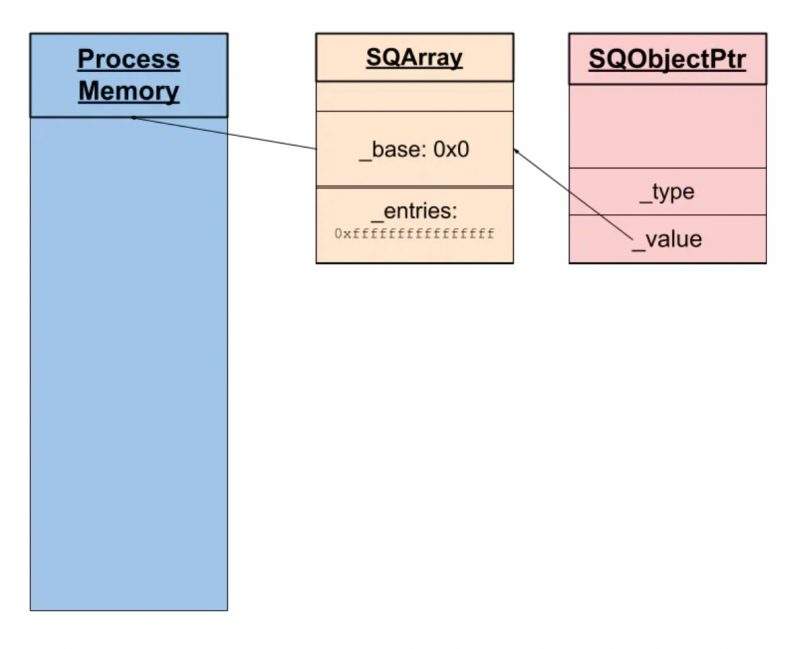
Chain of attacker-managed pointer that enabled reading through and producing to the complete tackle house. Resource: SonarSource.
Squirrel GitHub Repository Patched
The maintainer of the Squirrel GitHub repository acknowledged the vulnerability in August. A patch was pushed out as section of a code dedicate on Sept. 16.
But as mentioned by The Hacker Information, the alterations haven’t been provided in a new steady release, with the last official edition (v3.1) unveiled on March 27, 2016.
Hence, the scientists who learned the vulnerability are “highly” recommending that maintainers who use Squirrel in their jobs utilize the available deal with dedicate in order to secure in opposition to attacks.
Test out our totally free forthcoming stay and on-desire on the net city halls – exclusive, dynamic discussions with cybersecurity gurus and the Threatpost neighborhood.
Some sections of this report are sourced from:
threatpost.com


 Apple iCloud Hacker Steals Nudes
Apple iCloud Hacker Steals Nudes