U.S. businesses have to carry out vulnerability-disclosure procedures by March 2021, according to a new CISA mandate.
The U.S. government’s cybersecurity agency is now demanding federal organizations to put into action vulnerability-disclosure guidelines (VDPs), which would give moral hackers very clear recommendations for submitting bugs found in government systems, by next March.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Presently, most federal agencies deficiency a formal mechanism to get facts from white-hat hackers about prospective security vulnerabilities on their techniques. The new directive by the Cybersecurity and Infrastructure Security Company (CISA) aims to change this by demanding businesses to publish insurance policies with specific descriptions of which techniques are in scope, the styles of screening that are allowed and how moral hackers can post vulnerability studies. A directive is a compulsory course for federal, executive department, departments and companies.
“When companies combine vulnerability reporting into their current cybersecurity risk administration actions, they can weigh and deal with a broader array of issues,” according to the CISA directive, unveiled Wednesday. “This can help safeguard the information the general public has entrusted to the govt and offers federal cybersecurity groups extra info to secure their businesses. Also, making certain dependable guidelines throughout the govt department presents all those who report vulnerabilities equivalent protection and a much more uniform practical experience.”

The policies would include all internet-available units or expert services in government companies – like systems that have been not deliberately manufactured internet-obtainable, in accordance to CISA.
The directive mandates that organizations carry out VDPs with obvious wording all over which devices are in-scope, as properly as assurances all-around excellent-faith security research. VDPs should also plainly identify the mechanism by way of which researchers can report flaws to agencies, and present “timely” feedback on vulnerabilities described.
And, “to streamline conversation and collaboration, Federal agencies shall guarantee vulnerability reviews are available to method house owners in 48 hours of submission, and shall establish a channel for procedure owners to communicate with vulnerability reporters, as proper,” in accordance to a memorandum sent to heads of government departments and organizations.
Now we issued a directive that calls for federal civilian organizations in the executive department to publish a #vulnerability disclosure coverage. This will assure people know how to report a dilemma if they discover a single. Understand far more: https://t.co/5RsjPvyCOO. #InfoSec (1/3) pic.twitter.com/tPXXShmfRD
— Cybersecurity and Infrastructure Security Agency (@CISAgov) September 2, 2020
The directive first debuted in December 2019 as a draft open to public remark. Bryan Ware, assistant director of CISA, said that the company acquired much more than 200 suggestions from much more than 40 security scientists, academics, federal companies, technology firms, civil society and users of Congress.
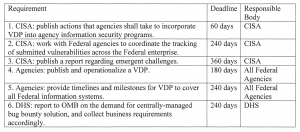 As future methods, in 60 days CISA will publish further advice concerning implementation, which will break down steps that organizations need to choose to include VDP into their details-security applications in an productive, standardized, liable and personalized way. And, within 180 days all businesses need to publish and operationalize their VDP.
As future methods, in 60 days CISA will publish further advice concerning implementation, which will break down steps that organizations need to choose to include VDP into their details-security applications in an productive, standardized, liable and personalized way. And, within 180 days all businesses need to publish and operationalize their VDP.
Ultimately, in 240 times organizations need to report “milestones for VDP to address all federal details systems” and CISA need to begin coordinating strategies to keep track of reported bugs.
As section of the directive, CISA will give a vulnerability-disclosure system company following spring. “We anticipate this will ease functions at companies, diminish their reporting stress beneath this directive, and boost discoverability for vulnerability reporters,” according to CISA.
On Wed Sept. 16 @ 2 PM ET: Learn the strategies to running a profitable Bug Bounty Method. Register today for this FREE Threatpost webinar “Five Essentials for Managing a Thriving Bug Bounty Program“. Hear from top Bug Bounty Software experts how to juggle general public compared to non-public programs and how to navigate the difficult terrain of controlling Bug Hunters, disclosure policies and budgets. Join us Wednesday Sept. 16, 2-3 PM ET for this LIVE webinar.


 Triple-Danger Cryptocurrency RAT Mines, Steals and Harvests
Triple-Danger Cryptocurrency RAT Mines, Steals and Harvests