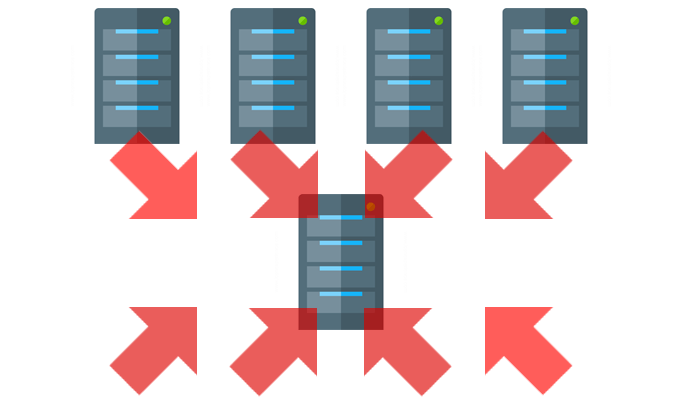
Systems are ripe for abuse by attackers who can abuse programs to launch DDoS attacks.
Scientists are warning internet censorship programs are ripe for abuse by a new variety of dispersed denial of support (DDoS) attack. The likely for abuse is regarding, scientists say, because attacks would consider advantage of a variety of reflection and amplification, which would be “extremely detrimental to any network” if carried out.
Netscout, which detailed the attack vector, dubbed the kind of DDoS attack a Middlebox HTTP Reflection/Amplification (MBHTTP) misconfiguration vulnerability. They say attacks can make DDoS volumes as superior as a 700,000 to 1 amplification factor.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The style of attack is a HTTP Reflection/Amplification, indicating an attacker can each magnify the total of destructive website traffic they produce when obscuring the resources of the attack visitors. An HTTP-based mostly DDoS attack sends junk HTTP requests to a target’s server tying up sources and locking out end users from using a particular internet site or provider.

Together with the risk of programs leveraged in large DDoS attacks the censorship techniques themselves would also be crippled, with visitors evaluation instruments knocked offline and permitted visitors blocked, according to researchers.
Tens of Millions of Gadgets Uncovered
Netscout credits a joint workforce of scientists from the College of Maryland and the University of Colorado Boulder for identifying the prevalent configuration vulnerability. Netscout estimates that 200 million IP addresses can perhaps be abused to launch attacks of this kind.
“Tens of thousands and thousands of these products are exposed and susceptible to abuse from adversaries and roughly 18 million of these offer at least a 2:1 amplification factor, resulting in one particular of the most prolific sorts of reflectors/amplifiers readily available to adversaries,” wrote Roland Dobbins and Steinthor Bjarnason in a technological examination posted Friday.
Why Censorship Devices?
Afflicted censorship systems, scientists uncovered, are specifically susceptible to these variety attacks simply because of three elements create scientists:
- A want on the element of the designers of such methods to scale their effectiveness and functionality in asymmetrical-routing scenarios by unwisely foregoing the need for a whole TCP handshake prior to responding to requests for a URI on the censorship systems’ deny-lists.
- The configuration and deployment of abusable techniques these types of that they will intercept and respond to inbound spoofed, crafted attack initiator packets on their northbound interfaces, instead than intercepting and processing outbound site visitors only on their southbound interfaces.
- The siting of some abusable devices inside of the ambit of routing loops, therefore converting them into what are correctly infinite repeating reflectors/amplifiers.
Netscout states a lot of censorship systems are “suboptimal” in design and “implementation choices make it possible for spoofed requests for denied FQDNs and/or URIs to be synthesized by attackers in significantly the same way as other perfectly-acknowledged reflection/amplification DDoS vectors.” This, they say outcomes in amplified HTTP responses staying directed to the meant targets of the attack.
Techniques Open to Attack For the reason that of Misconfiguration
At the heart of the vulnerability is a popular misconfiguration of censorship techniques that responds to HTML block notification pages from Uniform Resource Identifiers (URI) in a specific way.
“[A] absence of enforcement pertaining to TCP a few-way handshakes, make sure that attackers can spoof the IP addresses of their targets, deciding upon each the resource and destination ports of their alternative, in order to launch higher-pps/-bps HTTP reflection/amplification attacks,” scientists wrote.
Attackers can easily cloak attacks as properly.
“Skilled attackers are most likely to decide on source and location ports intended to permit the amplified attack site visitors to conform to widespread network entry regulate guidelines, so masquerading the attack targeted visitors so that at 1st glance, it appears to be authentic in the context of focused apps, companies, and infrastructure,” wrote Dobbins and Bjarnason.
Mitigation Risk: The Suggestions
Netscout suggests that network operators identify abuse-in a position censorship units and get rid of them.
“The security scientists who found this attack methodology have published a bespoke fork of the ZMap scanning software program, together with an accompanying module, which can be applied to establish abusable units,” scientists wrote.
“Nationwide internet censorship threatens totally free and open obtain to communication and information and facts for millions of people dwelling inside of censoring regimes… We present that this poses an even greater danger to the internet than beforehand comprehended,” wrote scientists from the University of Maryland and the University of Colorado Boulder.
Some areas of this short article are sourced from:
threatpost.com

 Former New York Observer Editor Re-charged Over Cyber-stalking
Former New York Observer Editor Re-charged Over Cyber-stalking