A preferred iOS computer software improvement package (SDK) utilised by above 1,200 apps—with a complete of extra than a billion mobile users—is said to have malicious code with the aim of perpetrating cellular advert-click fraud and capturing sensitive info.
According to a report released by cybersecurity firm Snyk, Mintegral — a cellular programmatic advertising system owned by Chinese cell ad tech enterprise Mobvista — incorporates an SDK part that enables it to collect URLs, unit identifiers, IP Tackle, operating program variation, and other user sensitive knowledge from compromised apps to a remote logging server.
The destructive iOS SDK has been named “SourMint” by Snyk researchers.
“The destructive code can spy on person exercise by logging URL-dependent requests built as a result of the application,” Snyk’s Alyssa Miller explained in a Monday examination. “This activity is logged to a 3rd-occasion server and could probably include individually identifiable data (PII) and other sensitive data.”
“Also, the SDK fraudulently reviews consumer clicks on advertisements, stealing possible income from competing advert networks and, in some cases, the developer/publisher of the software,” Miller added.
Whilst the names of the compromised apps using the SDK have not been disclosed, the code was uncovered in the iOS version of the Mintegral SDK (6.3.5.), with the 1st version of the malicious SDK courting back to July 17, 2019 (5.5.1). The Android edition of the SDK, however, isn’t going to show up to be affected.
Hijack Person Advert Clicks
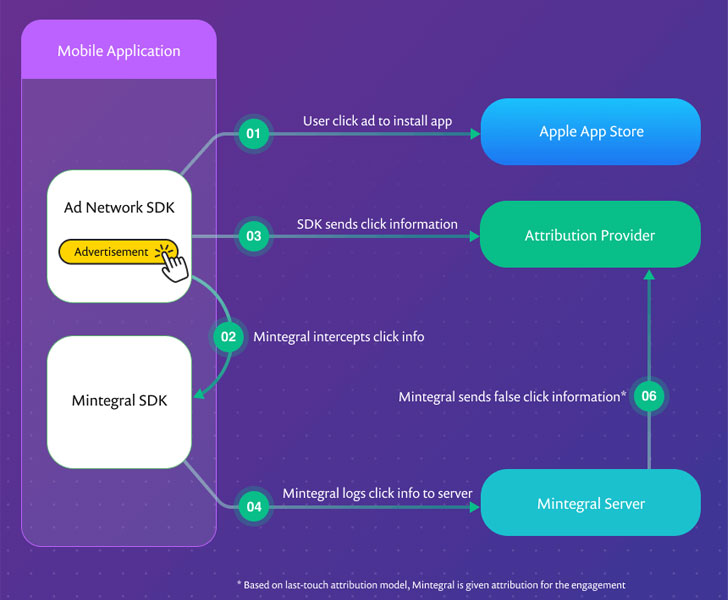
Stating that the SDK includes numerous anti-debug safety intending to conceal the real behavior of the software, Snyk uncovered evidence that Mintegral SDK not only intercepts all the ad clicks inside an application but also use this data to fraudulently attribute the click on to its advertisement network even in cases where by a competing advert network has served the advert.
It truly is well worth noting that applications that aspect in-application adverts incorporate SDKs from many advertisement networks with advertisement mediators’ assistance.
“When the attribution company tries to match the put in celebration to registered click notifications, it finds two that match,” the assessment found. “Employing a previous-contact attribution design, the Mintegral click on notification is supplied the attribution and the click notification from the other ad network is rejected.”
In other words, Mintegral has been thieving advert revenues from other advertising networks by declaring the advertisements from a different advert network as its very own, in addition to robbing developers off their revenues even when the system just isn’t remaining made use of to serve adverts.
“In our investigation, we learned that the moment the Mintegral SDK is built-in into an application, it intercepts the clicks even if Mintegral isn’t enabled to provide advertisements,” Miller claimed. “In this case, ad revenue that must have arrive back to the developer or publisher by way of a competing advertisement network will never ever be paid to the developer.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Gathering Much more Info Than Required for Advertisement Click Attribution
Even a lot more concerningly, the SDK incorporates features that are made to snoop on all conversation from the impacted applications, with the scope of details being gathered significantly extra than what is essential for reputable click attribution.
The information logged incorporates OS Edition, IP Handle, charging point out, Mintegral SDK version, network sort, design, package deal title, advertising and marketing identifier (IDFA or Identifier for Advertisers), and more.
“The tries by Mintegral to conceal the nature of the knowledge staying captured, both equally by way of anti-tampering controls and a personalized proprietary encoding method, are reminiscent of comparable features claimed by researchers that analyzed the TikTok app,” Miller mentioned.
While there is certainly no way to know for customers to know if they’re making use of an app that embeds the Mintegral SDK, it is really imperative that 3rd-occasion builders review their applications and remove the SDK to plug the information leak.
For its section, Apple is introducing new privacy characteristics in its future iOS 14 update that helps make it more challenging for third-celebration applications to observe end users by inquiring for their express consent for serving focused advertisements.
Found this post attention-grabbing? Stick to THN on Fb, Twitter and LinkedIn to read extra distinctive written content we submit.


 F-Safe: Enhance EDR to Quit Lazarus Group
F-Safe: Enhance EDR to Quit Lazarus Group