Cybersecurity scientists these days disclosed a new really vital “wormable” vulnerability—carrying a severity rating of 10 out of 10 on the CVSS scale—affecting Windows Server variations 2003 to 2019.
The 17-yr-old remote code execution flaw (CVE-2020-1350), dubbed ‘SigRed’ by Check Issue, could make it possible for an unauthenticated, distant attacker to acquire domain administrator privileges about qualified servers and seize complete management of an organization’s IT infrastructure.
A risk actor can exploit SigRed vulnerability by sending crafted malicious DNS queries to a Windows DNS server and realize arbitrary code execution, enabling the hacker to intercept and manipulate users’ email messages and network targeted visitors, make providers unavailable, harvest users’ qualifications and much additional.
In a detailed report shared with The Hacker News, the Verify Position researcher Sagi Tzadik verified that the flaw is wormable in nature, permitting attackers to launch an assault that can unfold from one particular susceptible personal computer to a further with out any human interaction.
“A solitary exploit can start off a chain response that lets attacks to spread from vulnerable device to susceptible equipment with out necessitating any human interaction,” the researcher claimed.
“This implies that a one compromised machine could be a ‘super spreader,’ enabling the assault to unfold throughout an organization’s network in just minutes of the very first exploit.”
Just after the cybersecurity firm responsibly disclosed its findings to Microsoft, the Windows maker ready a patch for the vulnerability and rolling it out starting up today as section of its July Patch Tuesday, which also features security updates for 122 other vulnerabilities, with a complete 18 flaws shown as crucial, and 105 as critical in severity.
Microsoft explained it discovered no evidence to present that the bug has been actively exploited by attackers, and recommended consumers to set up patches immediately.
“Home windows DNS Server is a core networking ingredient. Although this vulnerability is not at this time identified to be used in active attacks, it is important that prospects apply Home windows updates to handle this vulnerability as quickly as achievable,” Microsoft explained.
Crafting Destructive DNS Responses
Stating that the objective was to detect a vulnerability that would let an unauthenticated attacker compromise a Home windows Area setting, Examine Place researchers mentioned they centered on Home windows DNS, exclusively using a nearer search at how a DNS server parses an incoming question or a response for a forwarded question.
A forwarded question transpires when a DNS server are not able to resolve the IP deal with for a provided area identify (e.g., www.google.com), ensuing in the query currently being forwarded to an authoritative DNS title server (NS).
To exploit this architecture, SigRed requires configuring a domain’s (“deadbeef.entertaining”) NS resource records to place to a destructive title server (“ns1.41414141.club”), and querying the target DNS server for the area in order to have the latter parse responses from the identify server for all subsequent queries associated to the area or its subdomains.
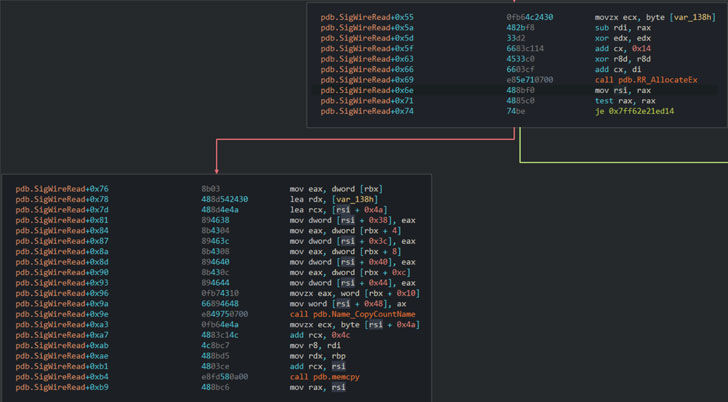
With this set up in place, an attacker can cause an integer overflow flaw in the purpose that parses incoming responses for forwarded queries (“dns.exe!SigWireRead”) to send a DNS response that consists of a SIG source document greater than 64KB and induce a “controlled heap-based mostly buffer overflow of roughly 64KB over a tiny allotted buffer.”
Put in another way the flaw targets the functionality dependable for allocating memory for the useful resource document (“RR_AllocateEx”) to crank out a final result bigger than 65,535 bytes to cause an integer overflow that potential customers to a much scaled-down allocation than predicted.
But with a single DNS information restricted to 512 bytes in UDP (or 4,096 bytes if the server supports extension mechanisms) and 65,535 bytes in TCP, the researchers observed that a SIG reaction with a lengthy signature on your own wasn’t plenty of to trigger the vulnerability.
To attain this, the attack cleverly requires gain of DNS identify compression in DNS responses to create a buffer overflow applying the aforementioned procedure to maximize the allocation’s dimensions by a significant quantity.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Distant Exploitation of the Flaw
Which is not all. SigRed can be brought on remotely by using a browser in confined eventualities (e.g., Internet Explorer and non-Chromium based Microsoft Edge browsers), allowing for an attacker to abuse Windows DNS servers’ support for link reuse and question pipelining capabilities to “smuggle” a DNS question inside of an HTTP request payload to a focus on DNS server on visiting a web page underneath their handle.
What is actually extra, the bug can be further exploited to leak memory addresses by corrupting the metadata of a DNS useful resource file and even obtain publish-what-exactly where capabilities, allowing for an adversary to hijack the execution movement and result in it to execute unintended recommendations.
Remarkably, DNS shoppers (“dnsapi.dll”) are not inclined to the similar bug, primary the scientists to suspect that “Microsoft manages two fully distinct code bases for the DNS server and the DNS shopper, and does not synchronize bug patches among them.”
Given the severity of the vulnerability and the superior chances of lively exploitation, it is really advised that customers patch their affected Windows DNS Servers to mitigate the threat.
As a momentary workaround, the greatest length of a DNS information (in excess of TCP) can be established to “0xFF00” to eliminate the probabilities of a buffer overflow:
reg insert “HKEY_Community_MACHINESYSTEMCurrentControlSetServicesDNSParameters” /v “TcpReceivePacketSize” /t REG_DWORD /d 0xFF00 /f net quit DNS && net begin DNS
“A DNS server breach is a really significant detail. Most of the time, it places the attacker just a person inch absent from breaching the full organization. There are only a handful of these vulnerability styles at any time unveiled,” Look at Point’s Omri Herscovici instructed The Hacker Information.
“Each individual group, huge or compact employing Microsoft infrastructure is at important security hazard, if remaining unpatched. The hazard would be a full breach of the whole company network.”
Identified this article intriguing? Observe THN on Fb, Twitter and LinkedIn to read additional exclusive information we publish.


 Adobe Discloses Significant Code-Execution Bugs in July Update
Adobe Discloses Significant Code-Execution Bugs in July Update