A 29-yr-aged Ukrainian national has been arrested in connection with jogging a “refined cryptojacking scheme,” netting them in excess of $2 million (€1.8 million) in illicit income.
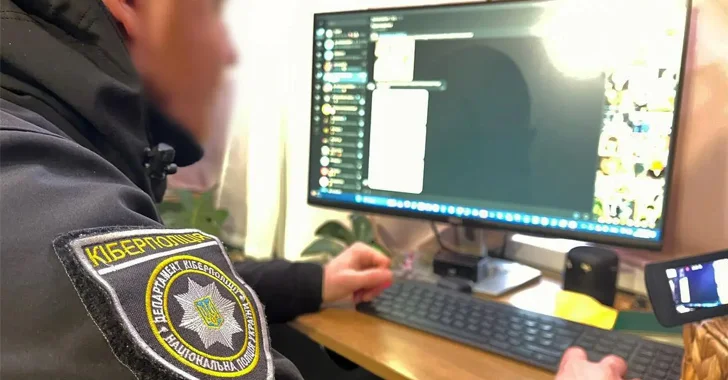
The particular person was apprehended in Mykolaiv, Ukraine, on January 9 by the National Law enforcement of Ukraine with aid from Europol and an unnamed cloud support service provider adhering to “months of intense collaboration.”
“A cloud supplier approached Europol back again in January 2023 with information and facts concerning compromised cloud user accounts of theirs,” Europol mentioned, adding it shared the intelligence with the Ukrainian authorities.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
As portion of the probe, three properties had been searched to unearth evidence towards the suspect.

Cryptojacking refers to a variety of cyber crime that involves the unauthorized use of a person’s or organization’s computing means to mine cryptocurrencies.
On the cloud, these attacks are typically carried out by infiltrating the infrastructure by way of compromised qualifications acquired as a result of other usually means and installing miners that use the contaminated host’s processing ability to mine crypto devoid of their awareness or consent.
“If the credentials do not have the threat actors’ wanted permissions, privilege escalation strategies are made use of to attain added permissions,” Microsoft pointed out in July 2023. “In some circumstances, menace actors hijack present subscriptions to even more obfuscate their functions.”
The core thought is to prevent having to pay for vital infrastructure expected to mine cryptocurrencies, both by using benefit of totally free trials or compromising reputable tenants to carry out cryptojacking attacks.
In October 2023, Palo Alto Networks Device 42 in depth a cryptojacking marketing campaign in which danger actors ended up identified stealing Amazon Web Providers (AWS) qualifications from GitHub repositories within five minutes of their general public disclosure to mine Monero.
Discovered this report fascinating? Abide by us on Twitter and LinkedIn to examine extra unique information we write-up.
Some components of this short article are sourced from:
thehackernews.com

 Nation-State Actors Weaponize Ivanti VPN Zero-Days, Deploying 5 Malware Families
Nation-State Actors Weaponize Ivanti VPN Zero-Days, Deploying 5 Malware Families