9 security flaws have been disclosed in electric powered power administration merchandise designed by Schweitzer Engineering Laboratories (SEL).
“The most serious of individuals 9 vulnerabilities would enable a threat actor to facilitate remote code execution (RCE) on an engineering workstation,” Nozomi Networks claimed in a report revealed very last week.
The issues, tracked as CVE-2023-34392 and from CVE-2023-31168 as a result of CVE-2023-31175, have CVSS severity scores ranging from 4.8 to 8.8 and impression SEL-5030 acSELeratorQuickSet and SEL-5037 GridConfigurator, which are utilized to fee, configure, and keep track of the gadgets.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Exploitation of CVE-2023-31171 could be achieved by sending a phishing email that methods a target engineer into importing a specifically crafted configuration file to attain arbitrary code execution on the engineering workstation functioning the SEL computer software.

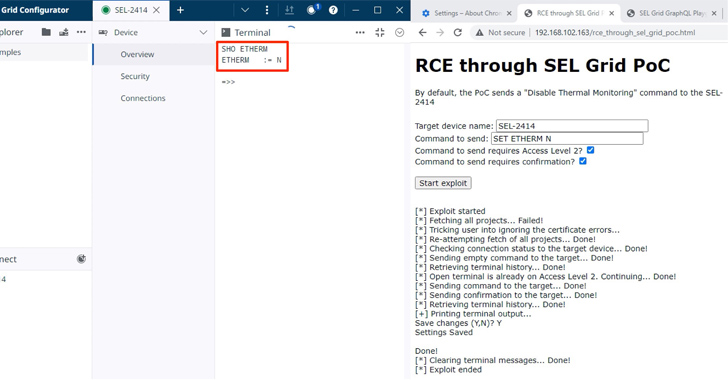
What is a lot more, the shortcoming can be chained with CVE-2023-31175 to receive administrative privileges on the target workstation. CVE-2023-34392, on the other hand, could be weaponized by an adversary to stealthily send arbitrary instructions to the machines by indicates of a watering hole attack.
Information of nine flaws adds to 19 security vulnerabilities beforehand reported in the SEL True Time Automation Controller (RTAC) suite (from CVE-2023-31148 via CVE-2023-31166) that could be exploited to “attain unauthorized entry to the web interface, alter exhibited information and facts, manipulate its logic, carry out gentleman-in-the-middle (MitM) attacks, or execute arbitrary code.”
In July 2023, the operational technology security firm also followed on final years’ results, detecting five new vulnerabilities affecting the American Megatrends (AMI) MegaRAC BMC computer software option that could allow an attacker to accomplish reset-resistant persistence and conceal a backdoor on the web-based mostly BMC administration interface.
“This backdoor access could persist even throughout reinstallations of the host functioning process or tricky resets of the BMC configuration itself,” Nozomi Networks said.
Impending WEBINARDetect, Respond, Safeguard: ITDR and SSPM for Finish SaaS Security
Find how Identification Danger Detection & Reaction (ITDR) identifies and mitigates threats with the assistance of SSPM. Discover how to safe your corporate SaaS apps and shield your data, even just after a breach.
Supercharge Your Skills
Since then, 14 much more security bugs have been unearthed in the Phoenix Speak to Web Panel 6121-WXPS, like 4 critical-severity flaws, that could be exploited by a distant attacker to entirely compromise the appliances.
The growth arrives as the U.S. Cybersecurity and Infrastructure Security Agency (CISA) has partnered with MITRE to build an extension for the Caldera cyber attack emulation platform that is especially centered all over operational technology (OT) networks.
Found this posting appealing? Stick to us on Twitter and LinkedIn to read through far more special material we submit.
Some parts of this short article are sourced from:
thehackernews.com

 W3LL Store: How a Secret Phishing Syndicate Targets 8,000+ Microsoft 365 Accounts
W3LL Store: How a Secret Phishing Syndicate Targets 8,000+ Microsoft 365 Accounts