Microsoft 365 (M365), formerly named Office environment 365 (O365), is Microsoft’s cloud system flagship item with main improvements forward, this kind of as the deprecation of their legacy authentication protocols.
Typically saved on or saved to the gadget, Essential Authentication protocols rely on sending usernames and passwords with every ask for, expanding the risk of attackers capturing users’ qualifications, specially if not TLS protected. Fundamental Authentication, when important for businesses applying legacy program, is not able to implement MFA and is outmoded by Present day Authentication.
The legacy settings have been on Microsoft’s radar to resolve for yrs. In 2018, Microsoft declared it would introduce a collection of modifications — and finally deprecation — to its authentication controls as a implies to aid businesses mitigate the risk. These adjustments had been established to just take place in excess of a number of years, and in September 2021, they declared that they will start off to completely disable Basic Auth in all tenants, no matter of utilization, with the exception of SMTP Auth by late 2022.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
In purchase to help a clean transition from these legacy protocols to a fashionable natural environment, Adaptive Shield has designed a move-by-stage manual to assist you decrease risk and strengthen your organization’s M365 security.
Adaptive Shield has also created and produced a PowerShell script that generates a unified report to map out the organization’s posture to know which buyers have legacy protocols enabled — for you to duplicate-paste. This post covers the broad strokes of the guideline from the discovery techniques and blocking access processes whilst displaying you how to take care of particular exclusions.
To download the whole guide with all the scripts, simply click right here.
Record of Basic Authentication Protocols
To secure the organization’s deployment, the initial stage is being aware of what forms of fundamental authentication protocols exist. Inside Microsoft, the deemed fundamental/legacy protocols contain:
- Authenticated SMTP – Utilised by POP and IMAP customers to mail email messages
- Autodiscover – Used by Outlook and EAS clientele to find and link to mailboxes in Trade On the net
- Exchange ActiveSync (EAS) – Made use of to join to mailboxes in Exchange On the web
- Exchange On the web PowerShell – Applied to link to Trade On the net with remote PowerShell
- Exchange Web Companies – A programming interface that is utilised by Outlook, Outlook for Mac, and third-party apps
- IMAP – Made use of by IMAP email shoppers, letting users to entry email from anyplace and any product
- MAPI about HTTP – Made use of by Outlook 2010 and afterwards
- OAB (Offline Handle Ebook) – A copy of tackle checklist collections that are downloaded and applied by Outlook
- Outlook Provider – Applied by the Mail and Calendar application for Windows 10
- POP3 – Applied by POP email customers to download new messages and delete them from the email serverReporting Web Companies
- Other purchasers – Any other protocols discovered as making use of legacy authentication
These authentication protocols do not support present day authentication mechanisms like multi-factor authentication (MFA), which suggests that enabling MFA will not suffice.
To enhance security and mitigate risk, corporations must obtain all the consumers and services that use the legacy protocols, migrate to use fashionable protocols, and block the primary kinds.
This whitepaper will get you by the discovery and blocking process, in addition to sharing guidance for added controls, like Mailbox solutions and Conditional Accessibility guidelines, that can boost your Microsoft 365 security posture.
Discovery: Know Your Posture
Just before shutting down all legacy protocols inside of the corporation, it is vital to determine consumers and services that are working with standard authentication. Somewhat than lower efficiency and generate user irritation, it is important to let end users know that the process is becoming upgraded, which will support stay away from business interruptions and endorse a painless changeover to contemporary protocols.
The are a couple means to understand about your organization’s posture working with these solutions:
- Powershell script – shows which users have the exchange legacy protocols enabled
- Conditional Obtain Report – shows precise usage of the fundamental authentication protocols
- Azure Advertisement Signal-In Logs – exhibits indicator-ins performed with legacy authentication clientele
PowerShell Script
Operating the PowerShell script acts as a very good starting up position to map out the consumer and service landscape that requirements to be mitigated.
Following operating a couple Powershell cmdlets, the Adaptive Defend workforce made this PowerShell script (See comprehensive guidebook for the script ) to merge them all into 1 unified report. The script generates a file: BasicProtocolsReport.csv. This file will demonstrate customers and their legacy protocol statuses. Each individual protocols’ position is tested from Authentication Policy, Mailbox expert services, and Transport config. Under is the checklist of the whole payload:
- user
- has_mailbox – Suggests if the person has a mailbox licensed
- blocked – Account status (enabled/disabled)
- mfa – Multi Factor Authentication enrollment standing
- auth_policy – Title of successful authentication plan (if set)
- is_ap_def – Implies no matter whether the powerful authentication policy is an corporation default or particularly assigned to the user
- protocol columns (activesync, imap, mapi, pop, smtp, outlookservice, powershell, ExchangeWebServices, autodiscover, OfflineAddressBook, rpc, ReportingWebServices) – Status (Genuine – enabled Untrue – blocked)
- protocl_technique columns (activesync, imap, mapi, pop, smtp, outlookservice) – Every single of these protocols can be blocked employing mailbox services options, authentication coverage, and transport config (world-wide settings for SMTP) this column’s information which strategies are in put to block these protocols.
Conditional Access – Report-Only
Generate a report with Conditional Access (see determine 1) which simulates the users and products and services that would be affected if you have been to block simple authentication protocols. This report provides you visibility into the users and companies truly using the legacy protocols.
The suggested run time for this report is a few months, over a company quarter, to capture any idle customers, and sporadic or time-scheduled services.
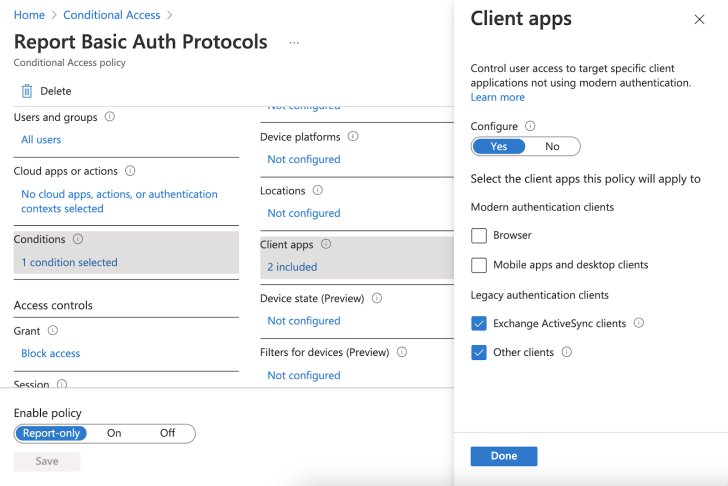 Figure 1: Crank out a consumer and providers report in excess of a 3-month period
Figure 1: Crank out a consumer and providers report in excess of a 3-month period
Reviewing the report and cross referencing it with the PowerShell script benefits will assist you to have a better photograph of legacy protocols in use, reducing the probability of lacking expert services or users that nevertheless have essential authentication protocols in perform.
Azure Advertisement Indicator-In Logs
The Azure Advert signal-in logs are yet another helpful way to know your posture. Diving into the logs and filtering “Client application” can expose indication-ins performed with legacy authentication clientele.
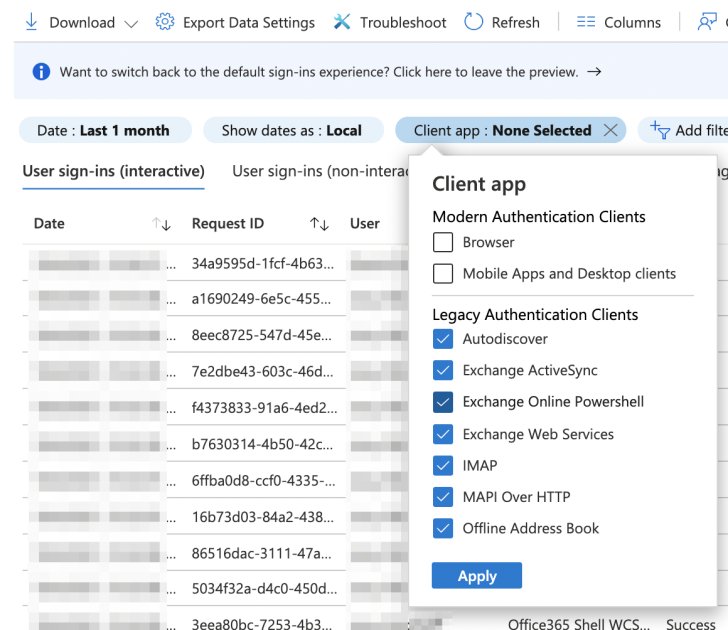 Determine 2: Reveal indicator-ins performed with legacy authentication consumers
Determine 2: Reveal indicator-ins performed with legacy authentication consumers
Just take note that the Azure indicator-in logs’ retention is up to 30 days and you might finish up lacking people and providers if this is the only tactic made use of.
Find out how an SSPM option can automate this process for you.
Blocking Obtain
Right after carefully investigating and identifying all of the usage of simple authentication protocols, it is time to block them.
There are a couple of very well-identified approaches to blocking authentication protocols, a well-liked just one getting employing the Conditional Accessibility insurance policies.
Even so, there are downsides to making use of Conditional Entry as the to start with line of defense.
Conditional Obtain policies are processed post first-factor authentication. This indicates that the credentials can be compromised (as suggestions will even now be provided to the consumer, an advantage in a brute force attack for instance), so the mailbox may well not have been breached but the attacker can try out the validated password on other programs.
Authentication Guidelines
Start off at the supply. Microsoft has a dedicated attribute for blocking simple authentication protocols, producing it uncomplicated to regulate making use of the Admin console.
Go to the Workplace Admin middle -> Configurations -> Org Options -> Fashionable authentication and uncheck all of the standard authentication protocols (make absolutely sure that modern day authentication is checked). See Figure 3.
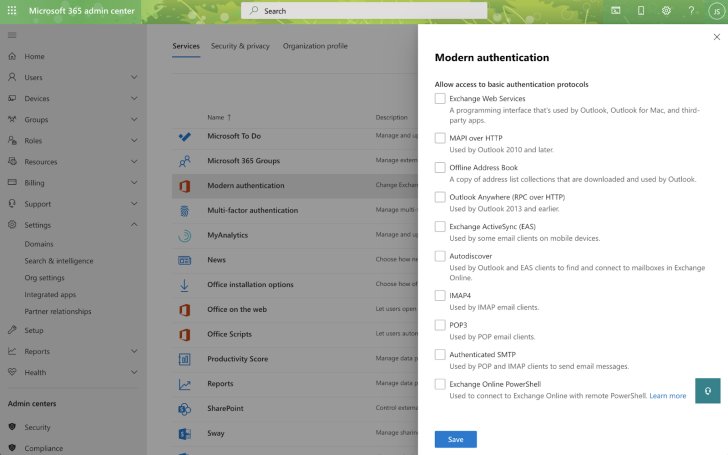 Figure 3: All simple authentication protocols are unchecked
Figure 3: All simple authentication protocols are unchecked
Shifting options in the admin middle results in a new authentication policy and sets it as the organization’s default plan.
Use PowerShell to validate:
$default_policy = Get-OrganizationConfig | Select DefaultAuthenticationPolicy
Get-AuthenticationPolicy $default_policy.DefaultAuthenticationPolicy
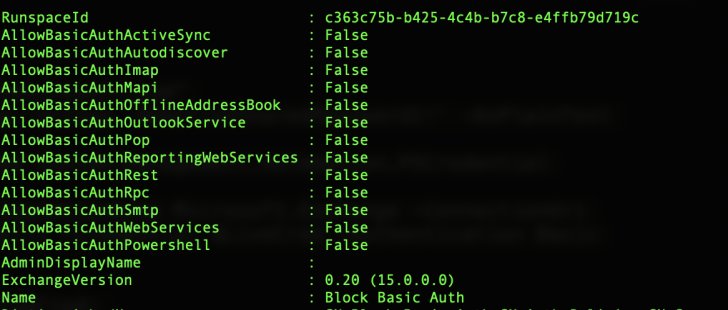
You can set exceptions and assign diverse authentication insurance policies to precise buyers utilizing PowerShell commands:
New-AuthenticationPolicy -Identify “Engineering Group” -AllowBasicAuthImap
Set-Person -Identity
This case in point creates a new authentication policy named Engineering Group that will allow primary authentication with IMAP and assigns it to a user.
Authentication procedures are a must but not plenty of to halt the risk risk of these legacy protocols by yourself. The authentication coverage addresses legacy purchasers, mailbox protocols this kind of as IMAP and SMTP, and other clients this sort of as PowerShell. Having said that, like Conditional Accessibility, even even though the support is blocked, some clientele will nevertheless supply feed-back (permitting specific cyberattacks to do well in gleaning a password for software in other SaaS applications). To prevent this incriminating opinions, fully turn off the services.
Shutting down a support can only be done for mailboxes, which covers 6 protocols out of the 13. Blocking the authentication plan covers the rest.
Mailbox Providers and Transport Config
Disabling a mailbox company (or enabling in case of exclusion) can be carried out using the UI for every consumer.
Go to the Workplace Admin middle -> People -> Active customers -> find a user (with mailbox) -> Mail tab -> Deal with email apps and uncheck the fundamental authentication protocols: POP, IMAP, SMTP. See figure 4.
Observe that SMTP, MAPI in excess of HTTP, and Cell (Trade ActiveSync) assist both equally simple and modern day authentication.
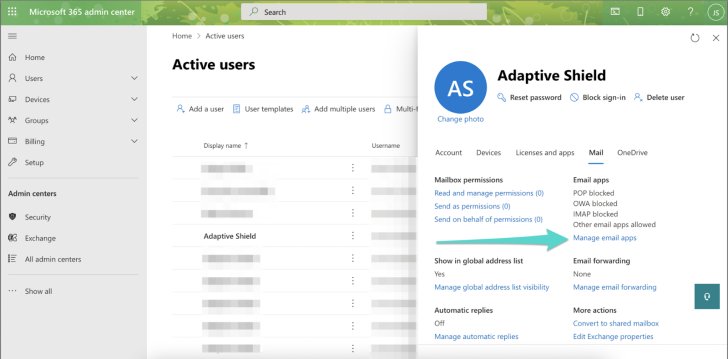 Determine 4. Basic authentication protocols are unchecked
Determine 4. Basic authentication protocols are unchecked
There is no SMTP bulk edit a number of mailboxes (POP and IMAP bulk edit can be identified in the common Exchange Admin Centre).
Transportation config controls the whole Trade group, and one particular of its capabilities is to transform off the SMTP service (the two standard and modern day).
Use PowerShell command to disable SMTP globally.
Set-TransportConfig -SmtpClientAuthenticationDisabled $accurate
In purchase to block essential authentication protocols for all mailboxes or subset use Powershell cmdlets:
$Consumers = Get-CASMailbox -ResultSize unrestricted
$Buyers | foreach Set-CASMailbox -Id $_ -SmtpClientAuthenticationDisabled $accurate -ActiveSyncEnabled $false -ImapEnabled $phony -MapiEnabled $wrong -PopEnabled $wrong -OWAEnabled $phony
Exclusions
There are instances that you may well take into account excluding and enabling legacy protocols. For example, a supervisor who is making use of an older machine or a script that was made employing the legacy protocols and now desires to be redeveloped might call for an exclusion.
In these instances, it is strongly encouraged to:
- Document: Have a method in area for requests and their reasoning
- Restrict: Place in area a time interval that will allow for the requester time to resolve the issue that they require the legacy protocols, whether replacing the system or time to rewrite the code, and many others.
- Conditional Accessibility: Use compensating controls by permitting only unique gadgets, or place in put IP limits, geofencing, and extra with the Conditional Obtain insurance policies.
Summary
Controlling SaaS configurations in an business is difficult and this guide is intended to aid relieve the discomfort and clean the changeover from the M365 legacy protocols to a modern-day environment. The approach has various ways and involves continuous oversight. From the discovery of the legacy authentication protocols opened and utilised by end users and organization procedures to blocking access and implementing and taking care of the exclusions, security teams have to have to dive in, remediate and control each problematic use of the authentication protocol.
In massive-scale environments, in which improvements often occur and configurations are in the hundreds, it is suggested to regulate SaaS misconfigurations with an automatic SaaS Security Posture Administration remedy (SSPM).
Uncovered this post exciting? Abide by THN on Fb, Twitter and LinkedIn to read through far more unique articles we submit.
Some sections of this posting are sourced from:
thehackernews.com


 Australian competition regulator seeks to undermine Google Search monopoly
Australian competition regulator seeks to undermine Google Search monopoly