Cybersecurity scientists this 7 days uncovered a new form of ransomware targeting macOS people that spreads by means of pirated applications.
In accordance to a number of unbiased stories from K7 Lab malware researcher Dinesh Devadoss, Patrick Wardle, and Malwarebytes, the ransomware variant — dubbed “EvilQuest” — is packaged together with genuine applications, which on set up, disguises itself as Apple’s CrashReporter or Google Application Update.
Other than encrypting the victim’s files, EvilQuest also will come with capabilities to ensure persistence, log keystrokes, make a reverse shell, and steal cryptocurrency wallet-similar data files.
With this progress, EvilQuest joins a handful of ransomware strains that have completely singled out macOS, which include KeRanger and Patcher.
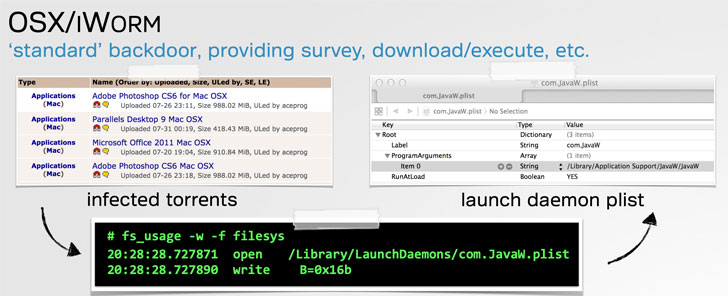
The supply of the malware appears to be trojanized variations of well known macOS application — this sort of as Tiny Snitch, a DJ software referred to as Combined In Important 8, and Ableton Are living — that are distributed on well-liked torrent web pages.
“To start, the respectable Minimal Snitch installer is attractively and skillfully packaged, with a perfectly-created personalized installer that is properly code signed,” Thomas Reed, director of Mac and cellular at Malwarebytes, claimed. “Nonetheless, this installer was a straightforward Apple installer offer with a generic icon. Even worse, the installer package deal was pointlessly dispersed inside a disk picture file.”
After installed on the contaminated host, EvilQuest does a sandbox look at to detect snooze-patching and comes equipped with anti-debugging logic to guarantee the malware application is not functioning beneath a debugger.
“It is not abnormal for malware to include delays,” Reed mentioned. “For illustration, the to start with-at any time Mac ransomware, KeRanger, incorporated a three-day delay concerning when it infected the method and when it began encrypting files. This allows to disguise the source of the malware, as the malicious habits might not be right away affiliated with a application mounted three days in advance of.”
It also kills any security computer software (e.g., Kaspersky, Norton, Avast, DrWeb, McAfee, Bitdefender, and Bullguard) that could detect or block these types of destructive conduct on the method, and sets up persistence using start agent and daemon house record data files (“com.apple.questd.plist”) to immediately restart the malware just about every time the user logs in.
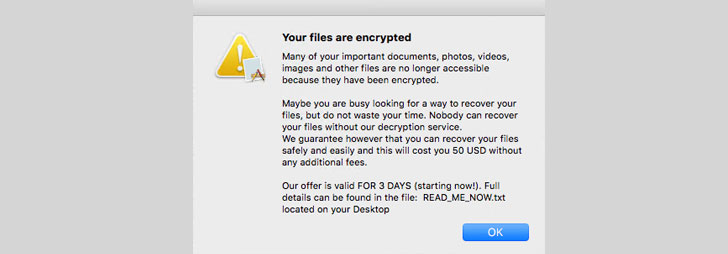
In the very last phase, EvilQuest launches a copy of by itself and starts off encrypting documents — counting cryptocurrency wallet (“wallet.pdf”) and keychain connected data files — prior to inevitably displaying ransom directions to pay out $50 in just 72 several hours or possibility leaving the information locked.
But EvilQuest’s features go over and above common ransomware, including the means to converse with a command-and-control server (“andrewka6.pythonanywhere.com”) to remotely execute instructions, initiate keylogger, create a reverse shell, and even execute a malicious payload right out of memory.
“Armed with these abilities, the attacker can retain complete management over an infected host,” Wardle claimed.
While do the job is on to find a weak point in the encryption algorithm to generate a decryptor, it really is advisable that macOS consumers make backups to stay clear of info loss and use a utility like RansomWhere? to thwart these assaults.
“The very best way of keeping away from the outcomes of ransomware is to maintain a excellent set of backups,” Reed concluded. “Keep at the very least two backup copies of all vital facts, and at least just one need to not be kept attached to your Mac at all occasions.”
Discovered this article intriguing? Stick to THN on Fb, Twitter and LinkedIn to examine far more exceptional content we article.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code


 EvilQuest Mac Ransomware Has Keylogger, Crypto Wallet-Thieving Capabilities
EvilQuest Mac Ransomware Has Keylogger, Crypto Wallet-Thieving Capabilities