A crypter (alternatively spelled cryptor) malware dubbed AceCryptor has been employed to pack a lot of strains of malware considering the fact that 2016.
Slovak cybersecurity organization ESET explained it identified above 240,000 detections of the crypter in its telemetry in 2021 and 2022. This quantities to a lot more than 10,000 hits for every thirty day period.
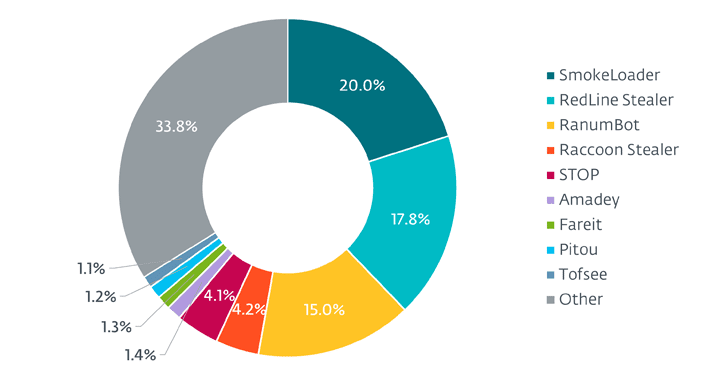
Some of the notable malware people contained in just AceCryptor are SmokeLoader, RedLine Stealer, RanumBot, Raccoon Stealer, Halt ransomware, and Amadey, among the other folks.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The international locations with the most detections consist of Peru, Egypt, Thailand, Indonesia, Turkey, Brazil, Mexico, South Africa, Poland, and India.
AceCryptor was initial highlighted by Avast in August 2022, detailing the use of the malware to distribute Halt ransomware and RedLine Stealer on Discord in the type of 7-Zip information.
Crypters are equivalent to packers, but rather of using compression, they are known to obfuscate the malware code with encryption to make detection and reverse engineering a good deal much more complicated.
They are also indicative of a pattern the place malware authors publicize this sort of capabilities for other menace actors, less technically refined or otherwise, who are hunting to armor their creations.
“Even though threat actors can produce and retain their individual custom cryptors, for crimeware threat actors it often might be a time-consuming or technically tough job to preserve their cryptor in a so-referred to as FUD (fully undetectable) state,” ESET researcher Jakub Kaloč explained.
“Demand from customers for these types of security has developed numerous crypter-as–a-services (CaaS) selections that pack malware.”
AceCryptor-packed malware is delivered by using trojanized installers of pirated application, spam e-mail bearing destructive attachments, or other malware that has by now compromised a host.
It’s also suspected to be offered as a CaaS, owing to the fact that it is applied by a number of menace actors to propagate a assorted assortment of malware people.
Approaching WEBINAR Zero Belief + Deception: Master How to Outsmart Attackers!
Discover how Deception can detect advanced threats, quit lateral movement, and greatly enhance your Zero Have confidence in approach. Be part of our insightful webinar!
Help save My Seat!.advert-button,.advert-label,.ad-label:followingexhibit:inline-block.advert_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px good #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-top-left-radius:25px-moz-border-radius-topleft:25px-webkit-border-bottom-ideal-radius:25px-moz-border-radius-bottomright:25px.advertisement-labelfont-sizing:13pxmargin:20px 0font-weight:600letter-spacing:.6pxcolor:#596cec.ad-label:right afterwidth:50pxheight:6pxcontent:”border-major:2px good #d9deffmargin: 8px.advert-titlefont-size:21pxpadding:10px 0font-excess weight:900text-align:leftline-height:33px.ad-descriptiontext-align:leftfont-size:15.6pxline-height:26pxmargin:5px !importantcolor:#4e6a8d.ad-buttonpadding:6px 12pxborder-radius:5pxbackground-color:#4469f5font-dimensions:15pxcolor:#fff!importantborder:0line-peak:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-fat:500letter-spacing:.2px
The crypter is greatly obfuscated, incorporating a 3-layer architecture to progressively decrypt and unpack each and every stage and eventually start the payload, while also showcasing anti-VM, anti-debugging, and anti-examination strategies to fly underneath the radar.
The next layer, in accordance to ESET, is claimed to have been launched in 2019 as an additional security mechanism.
The conclusions arrive as yet another crypter support codenamed ScrubCrypt has been leveraged cryptojacking teams like the 8220 Gang to illicitly mine cryptocurrency on contaminated hosts.
Earlier this January, Verify Position also unearthed a packer recognized as TrickGate which is made use of to deploy a huge range of malware these kinds of as TrickBot, Emotet, AZORult, Agent Tesla, FormBook, Cerber, Maze, and REvil for more than six yrs.
Found this post exciting? Follow us on Twitter and LinkedIn to read through a lot more exceptional information we post.
Some pieces of this write-up are sourced from:
thehackernews.com

 3 Challenges in Building a Continuous Threat Exposure Management (CTEM) Program and How to Beat Them
3 Challenges in Building a Continuous Threat Exposure Management (CTEM) Program and How to Beat Them