Patches have been released to address two new security vulnerabilities in Apache SuperSet that could be exploited by an attacker to attain distant code execution on influenced devices.
The update (version 2.1.1) plugs CVE-2023-39265 and CVE-2023-37941, which make it possible to conduct nefarious actions as soon as a terrible actor is in a position to achieve handle of Superset’s metadata databases.
Outside the house of these weaknesses, the newest variation of Superset also remediates a different improper Rest API authorization issue (CVE-2023-36388) that enables for reduced-privilege people to carry out server-side request forgery (SSRF) attacks.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
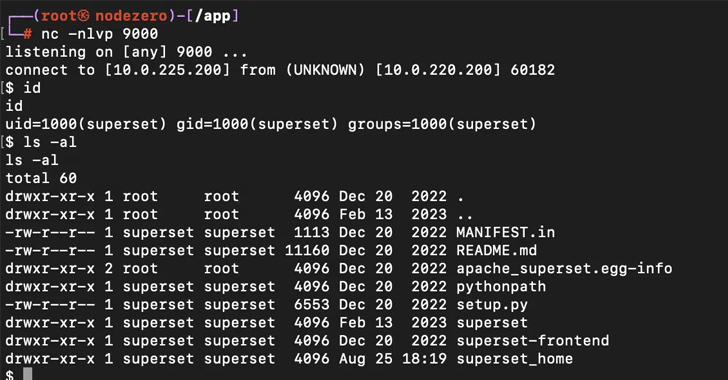
“Superset by style makes it possible for privileged consumers to hook up to arbitrary databases and execute arbitrary SQL queries against individuals databases utilizing the impressive SQLLab interface,” Horizon3.ai’s Naveen Sunkavally reported in a specialized publish-up.
“If Superset can be tricked into connecting to its individual metadata databases, an attacker can instantly read or create software configuration through SQLLab. This prospects to harvesting credentials and remote code execution.”
CVE-2023-39265 relates to a scenario of URI bypass when connecting to the SQLite database made use of for the metastore, enabling an attacker to execute info manipulation instructions.

Also tracked as element of the exact same CVE identifier is the deficiency of validation when importing SQLite databases relationship info from a file, which could be abused to import a maliciously crafted ZIP archive file.
“Superset versions from 1.5 to 2.1. use python’s pickle package deal to keep particular configuration information,” Sunkavally explained about CVE-2023-37941.
“An attacker with write access to the metadata databases can insert an arbitrary pickle payload into the retailer, and then set off deserialization of it, major to distant code execution.”
Some of the other flaws that have been patched in the newest release are below –
- An MySQL arbitrary file browse vulnerability that could be exploited to get credentials to the metadata database
- The abuse of superset load_illustrations command to get the metadata databases URI from the user interface and modify knowledge saved in it
- The use of default credentials to access the metadata databases in some installations of Superset
- The leak of databases credentials in plaintext when querying the /api/v1/database API as a privileged person (CVE-2023-30776, preset in 2.1.)
The disclosure arrives a minor about 4 months following the business disclosed a high-severity flaw in the exact merchandise (CVE-2023-27524, CVSS rating: 8.9) that could empower unauthorized attackers to gain admin accessibility to the servers and execute arbitrary code.
Impending WEBINARWay Way too Vulnerable: Uncovering the Condition of the Id Attack Surface
Reached MFA? PAM? Service account defense? Discover out how very well-outfitted your corporation actually is towards id threats
Supercharge Your Expertise
The problem occurs as a final result of employing a default Top secret_Vital that could be abused by attackers to authenticate and access unauthorized sources on internet-exposed installations.
Considering the fact that the community disclosure of the flaw in April 2023, Horizon3.ai mentioned 2076 out of 3842 Superset servers are even now applying a default Magic formula_Essential, with about 72 situations making use of a trivially guessable Solution_Key like superset, SUPERSET_Top secret_Important, 1234567890, admin, changeme, thisisasecretkey, and your_top secret_crucial_below.
“The consumer is liable for location the Flask Mystery_Essential, which invariably prospects to some buyers setting weak keys,” Sunkavally reported, urging the maintainers to increase assist for automatically generating the key.
“At the root of a lot of of the vulnerabilities […] is the truth that the Superset web interface permits consumers to join to the metadata database. At the root of several of the vulnerabilities in this write-up is the fact that the Superset web interface permits buyers to link to the metadata database.”
Identified this post appealing? Stick to us on Twitter and LinkedIn to go through far more special material we article.
Some parts of this write-up are sourced from:
thehackernews.com

 Mirai Botnet Variant ‘Pandora’ Hijacks Android TVs for Cyberattacks
Mirai Botnet Variant ‘Pandora’ Hijacks Android TVs for Cyberattacks