A now-patched critical remote code execution (RCE) vulnerability in GitLab’s web interface has been detected as actively exploited in the wild, cybersecurity scientists alert, rendering a substantial amount of internet-struggling with GitLab circumstances inclined to attacks.
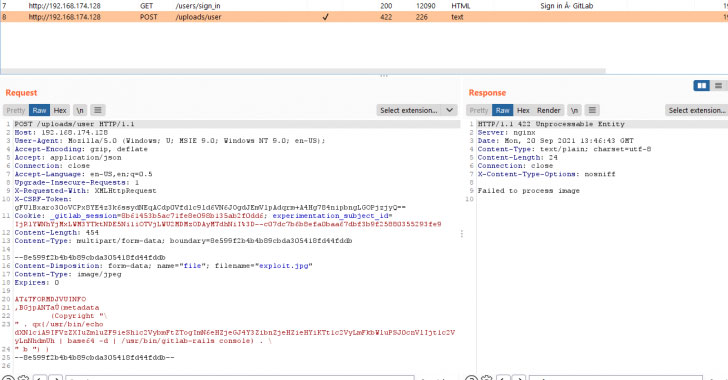
Tracked as CVE-2021-22205, the issue relates to an inappropriate validation of consumer-supplied visuals that final results in arbitrary code execution. The vulnerability, which affects all versions starting from 11.9, has because been addressed by GitLab on April 14, 2021 in variations 13.8.8, 13.9.6, and 13.10.3.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
In just one of the actual-planet attacks specific by HN Security previous thirty day period, two user accounts with admin privileges were being registered on a publicly-available GitLab server belonging to an unnamed customer by exploiting the aforementioned flaw to add a destructive payload that potential customers to remote execution of arbitrary instructions, including acquiring elevated permissions.
Although the flaw was at first deemed to be a case of authenticated RCE and assigned a CVSS rating of 9.9, the severity score was revised to 10. on September 21, 2021 owing to the simple fact that it can be induced by unauthenticated danger actors as well.
“Even with the small go in CVSS score, a adjust from authenticated to unauthenticated has significant implications for defenders,” cybersecurity agency Quick7 stated in an notify posted Monday.

Irrespective of the community availability of the patches for far more than six months, of the 60,000 internet-experiencing GitLab installations, only 21% of the circumstances are mentioned to be thoroughly patched in opposition to the issue, with another 50% still vulnerable to RCE attacks.
In the light of the unauthenticated nature of this vulnerability, exploitation activity is expected to increase, generating it critical that GitLab users update to the latest version as soon as feasible. “In addition, ideally, GitLab really should not be an internet dealing with provider,” the scientists reported. “If you need to entry your GitLab from the internet, take into account placing it behind a VPN.”
Further technical investigation associated to the vulnerability can be accessed listed here.
Discovered this report intriguing? Abide by THN on Facebook, Twitter and LinkedIn to read through much more exclusive written content we submit.
Some sections of this article are sourced from:
thehackernews.com


 Google to Pay Hackers $31,337 for Exploiting Patched Linux Kernel Flaws
Google to Pay Hackers $31,337 for Exploiting Patched Linux Kernel Flaws