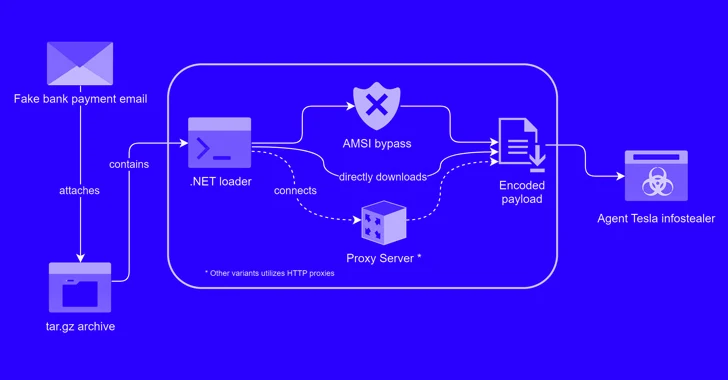
A new phishing marketing campaign has been noticed leveraging a novel loader malware to deliver an facts stealer and keylogger referred to as Agent Tesla.
Trustwave SpiderLabs explained it discovered a phishing email bearing this attack chain on March 8, 2024. The concept masquerades as a financial institution payment notification, urging the user to open an archive file attachment.
The archive (“Lender Handlowy w Warszawie – dowód wpłaty_pdf.tar.gz”) conceals a malicious loader that activates the technique to deploy Agent Tesla on the compromised host.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“This loader then employed obfuscation to evade detection and leveraged polymorphic habits with complicated decryption techniques,” security researcher Bernard Bautista claimed in a Tuesday examination.
“The loader also exhibited the functionality to bypass antivirus defenses and retrieved its payload employing unique URLs and person brokers leveraging proxies to even further obfuscate website traffic.”
The tactic of embedding malware inside seemingly benign files is a tactic that has been repeatedly used by threat actors to trick unsuspecting victims into triggering the infection sequence.

The loader utilised in the attack is created in .NET, with Trustwave identifying two unique variants that each individual make use of a various decryption regime to access its configuration and ultimately retrieve the XOR-encoded Agent Tesla payload from a distant server.
In an energy to evade detection, the loader is also designed to bypass the Windows Antimalware Scan Interface (AMSI), which offers the potential for security software to scan information, memory, and other info for threats.
It achieves this by “patching the AmsiScanBuffer perform to evade malware scanning of in-memory written content,” Bautista described.
The previous period includes decoding and executing Agent Tesla in memory, permitting the danger actors to stealthily exfiltrate sensitive facts through SMTP making use of a compromised email account affiliated with a authentic security system supplier in Turkey (“merve@temikan[.]com[.]tr”).
The technique, Trustwave explained, not only does not elevate any crimson flags, but also affords a layer of anonymity that would make it more difficult to trace the attack again to the adversary, not to point out help you save the effort of owning to set up dedicated exfiltration channels.
“[The loader] employs procedures like patching to bypass Antimalware Scan Interface (AMSI) detection and dynamically load payloads, guaranteeing stealthy execution and reducing traces on disk,” Bautista said. “This loader marks a noteworthy evolution in the deployment tactics of Agent Tesla.”
The disclosure arrives as BlueVoyant uncovered an additional phishing activity performed by a cybercrime group called TA544 that leverages PDFs dressed up as authorized invoices to propagate WikiLoader (aka WailingCrab) and establish connections with command-and-regulate (C2) server that virtually completely encompasses hacked WordPress web-sites.
It truly is truly worth noting that TA544 also weaponized a Windows security bypass flaw tracked as CVE-2023-36025 in November 2023 to distribute Remcos RAT by way of a diverse loader family dubbed IDAT Loader, making it possible for it to seize manage of infected programs.
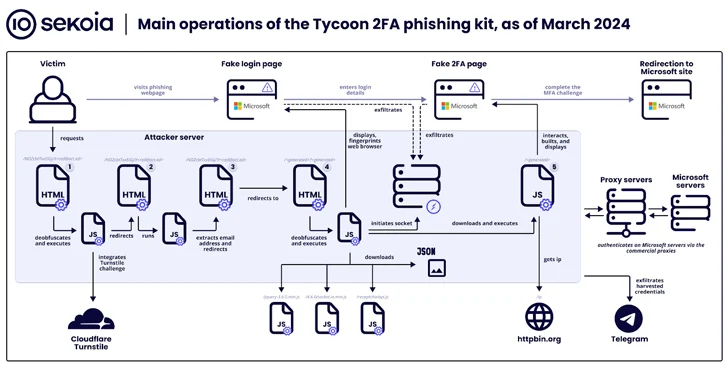
The findings also comply with a surge in the use of a phishing package named Tycoon, which Sekoia explained has “grow to be one particular of the most prevalent [adversary-in-the-middle] phishing kits over the final few months, with far more than 1,100 domain names detected amongst late Oct 2023 and late February 2024.”

Tycoon, publicly documented by Trustwave final month, permits cyber criminals to target end users of Microsoft 365 with phony login pages to capture their credentials, session cookies, and two-factor authentication (2FA) codes. It is really recognized to be lively considering that at least August 2023, with the service available by way of non-public Telegram channels.
The phishing kit is notable for incorporating considerable site visitors filtering approaches to thwart bot exercise and analysis makes an attempt, demanding web site guests to entire a Cloudflare Turnstile problem right before redirecting buyers to a credential harvesting site.
Tycoon also shares operational and style-level similarities with the Dadsec OTT phishing package, boosting the possibility that the developers had accessibility to and tweaked the supply code of the latter to suit their needs. This is supported by the point that Dadsec OTT had its supply code leaked in October 2023.
“The developer increased stealth capabilities in the most the latest model of the phishing package,” Sekoia stated. “The the latest updates could reduce the detection amount by security goods of the Tycoon 2FA phishing web pages and the infrastructure. Furthermore, its simplicity of use and its comparatively very low rate make it rather well-liked between threat actors.”
Found this post intriguing? Stick to us on Twitter and LinkedIn to go through much more unique written content we submit.
Some components of this article are sourced from:
thehackernews.com

 Two Chinese APT Groups Ramp Up Cyber Espionage Against ASEAN Countries
Two Chinese APT Groups Ramp Up Cyber Espionage Against ASEAN Countries