The Iranian danger actor tracked as APT34 has been joined to a new phishing attack that sales opportunities to the deployment of a variant of a backdoor named SideTwist.
“APT34 has a superior amount of attack technology, can design and style distinctive intrusion solutions for diverse types of targets, and has source chain attack capacity,” NSFOCUS Security Labs explained in a report printed final week.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
APT34, also identified by the names Cobalt Gypsy, Hazel Sandstorm (formerly Europium), Helix Kitten, and OilRig, has a track document of concentrating on telecommunications, governing administration, defense, oil and economic providers verticals in the Middle East given that at the very least 2014 by using spear-phishing lures that culminate in the deployment of various backdoors.

1 of the vital attributes of the hacking outfit is its capacity to create new and up-to-date resources to limit the odds of detection and get a foothold on compromised hosts for extended durations of time.
SideTwist was initial documented as utilised by APT34 in April 2021, with Check out Point describing it as an implant able of file obtain/upload and command execution.
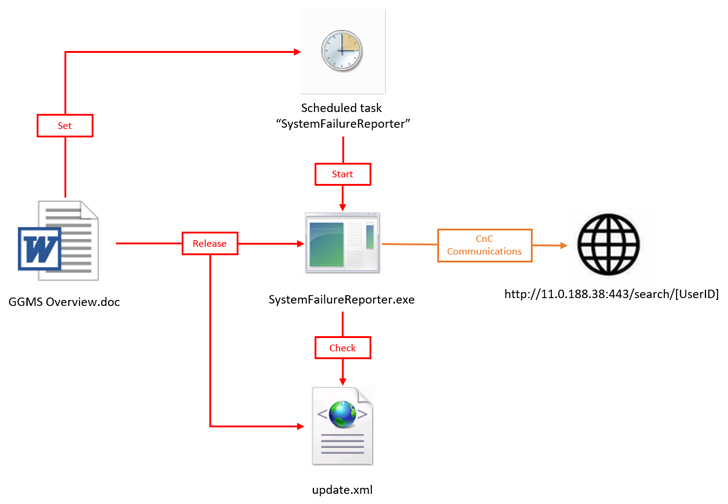
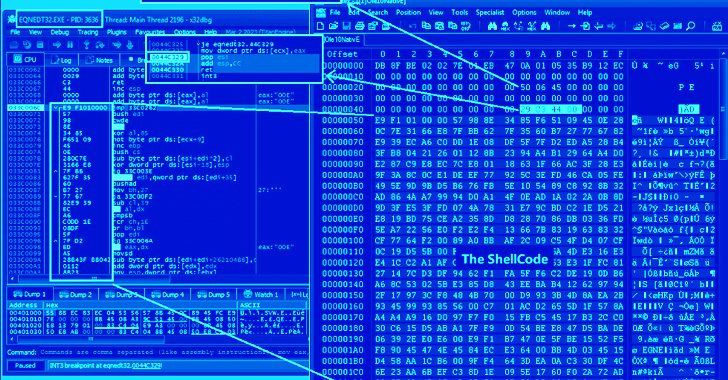
The attack chain recognized by NSFOCUS begins with a bait Microsoft Term doc that embeds inside a malicious macro, which, in transform, extracts and launches the Foundation64-encoded payload stored in the file.
The payload is a variant of SideTwist which is compiled making use of GCC and establishes interaction with a distant server (11..188[.]38) to obtain even further instructions.
The improvement comes as Fortinet FortiGuard Labs captured a phishing marketing campaign that spreads a new Agent Tesla variant employing a specifically crafted Microsoft Excel document that exploits CVE-2017-11882, a 6-year-aged memory corruption vulnerability in Microsoft Office’s Equation Editor, and CVE-2018-0802.
Approaching WEBINARWay Way too Susceptible: Uncovering the Condition of the Identity Attack Area
Achieved MFA? PAM? Service account protection? Obtain out how perfectly-geared up your firm definitely is versus id threats
Supercharge Your Skills
“The Agent Tesla core module collects sensitive details from the victim’s product,” security researcher Xiaopeng Zhang said. “This information and facts incorporates the saved credentials of some software package, the victim’s keylogging information, and screenshots.”
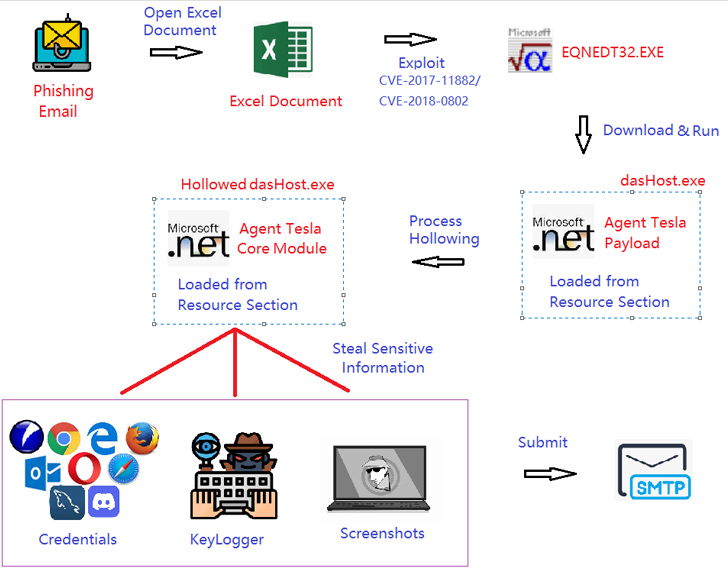
According to info shared by cybersecurity agency Qualys, CVE-2017-11882 stays one particular of the most favored flaws to day, exploited by “467 malware, 53 danger actors, and 14 ransomware” as recently as August 31, 2023.
It also follows the discovery of yet another phishing attack that has been observed to make use of ISO impression file lures to start malware strains this kind of as Agent Tesla, LimeRAT, and Remcos RAT on contaminated hosts.
Observed this article appealing? Observe us on Twitter and LinkedIn to read through additional special content we publish.
Some areas of this posting are sourced from:
thehackernews.com


 Three CISOs Share How to Run an Effective SOC
Three CISOs Share How to Run an Effective SOC