Focus! If you use Amazon’s voice assistant Alexa in you good speakers, just opening an harmless-seeking web-link could let attackers set up hacking abilities on it and spy on your pursuits remotely.
Cybersecurity scientists today disclosed intense security vulnerabilities in Amazon’s Alexa digital assistant that could render it susceptible to a variety of destructive attacks.
In accordance to a report launched by Verify Point Study and shared with The Hacker Information, the “exploits could have authorized an attacker to clear away/put in expertise on the qualified victim’s Alexa account, entry their voice historical past and get personalized facts by means of skill conversation when the person invokes the mounted talent.”
“Smart speakers and digital assistants are so commonplace that it’s effortless to overlook just how a lot particular info they hold, and their job in controlling other clever products in our homes,” Oded Vanunu, head of merchandise vulnerabilities study, reported.
“But hackers see them as entry factors into peoples’ life, providing them the opportunity to access info, eavesdrop on conversations or conduct other destructive actions without having the proprietor being informed,” he additional.
Amazon patched the vulnerabilities after the scientists disclosed their results to the corporation in June 2020.
An XSS Flaw in One of Amazon’s Subdomains
Check Issue stated the flaws stemmed from a misconfigured CORS plan in Amazon’s Alexa cellular application, as a result probably making it possible for adversaries with code-injection abilities on one Amazon subdomain to accomplish a cross-domain assault on a further Amazon subdomain.
Place in different ways, profitable exploitation would have essential just one click on on an Amazon link that has been specifically crafted by the attacker to direct people to an Amazon subdomain that is vulnerable to XSS attacks.
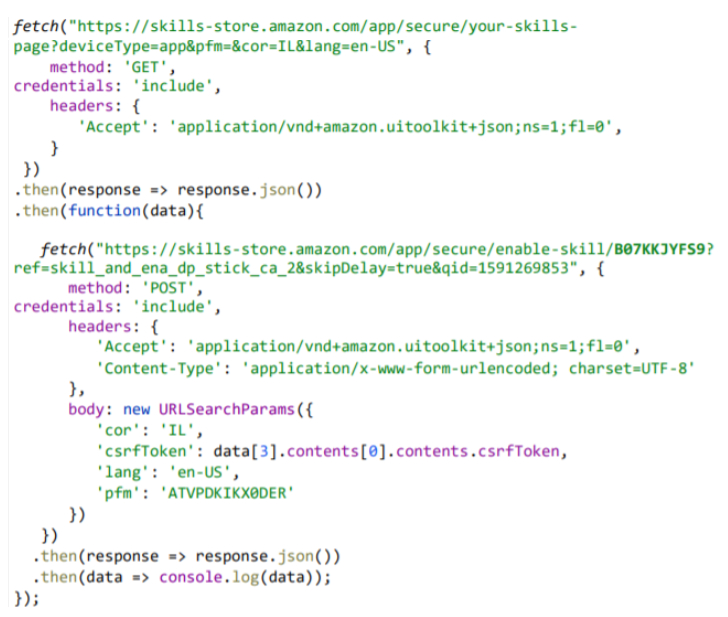
In addition, the researchers discovered that a request to retrieve a listing of all the put in abilities on the Alexa device also returns a CSRF token in the response.
The key goal of a CSRF token is to reduce Cross-Web page Ask for Forgery attacks in which a destructive link or system brings about an authenticated user’s web browser to accomplish an unwelcome action on a respectable internet site.
This happens since the web site are unable to differentiate in between authentic requests and forged requests.
But with the token in possession, a undesirable actor can develop valid requests to the backend server and perform steps on the victim’s behalf, this sort of as installing and enabling a new ability for the sufferer remotely.
In short, the assault performs by prompting the user to click on on a destructive url that navigates to an Amazon subdomain (“monitor.amazon.com”) with an XSS flaw that can be exploited to attain code-injection.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The attacker then employs it to bring about a request to “skillsstore.amazon.com” subdomain with the victim’s credentials to get a record of all put in techniques on the Alexa account and the CSRF token.
In the final stage, the exploit captures the CSRF token from the response and takes advantage of it to put in a talent with a specific skill ID on the target’s Alexa account, stealthily take out an set up talent, get the victim’s voice command record, and even obtain the personalized information saved in the user’s profile.
The Want for IoT Security
With the global clever speaker sector dimension projected to attain $15.6 billion by 2025, the investigation is yet another motive why security is essential in the IoT space.
As digital assistants become extra pervasive, they are increasingly turning out to be valuable targets for attackers hunting to steal delicate information and disrupt wise home devices.
“IoT devices are inherently vulnerable and nonetheless deficiency adequate security, which will make them beautiful targets to menace actors,” the researchers concluded.
“Cybercriminals are continually searching for new strategies to breach equipment, or use them to infect other critical techniques. The two the bridge and the devices provide as entry factors. They ought to be stored secured at all occasions to preserve hackers from infiltrating our smart properties.”
Located this posting attention-grabbing? Observe THN on Facebook, Twitter and LinkedIn to read through additional special content material we put up.


 CASB Complexity Means Many Items Are Less than-Utilized
CASB Complexity Means Many Items Are Less than-Utilized