The Android banking trojan identified as Anatsa has expanded its aim to consist of Slovakia, Slovenia, and Czechia as section of a new marketing campaign observed in November 2023.
“Some of the droppers in the marketing campaign productively exploited the accessibility support, in spite of Google Play’s increased detection and safety mechanisms,” ThreatFabric stated in a report shared with The Hacker News.
“All droppers in this campaign have shown the capability to bypass the restricted configurations for accessibility assistance in Android 13.” The marketing campaign, in whole, will involve 5 droppers with far more than 100,000 full installations.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
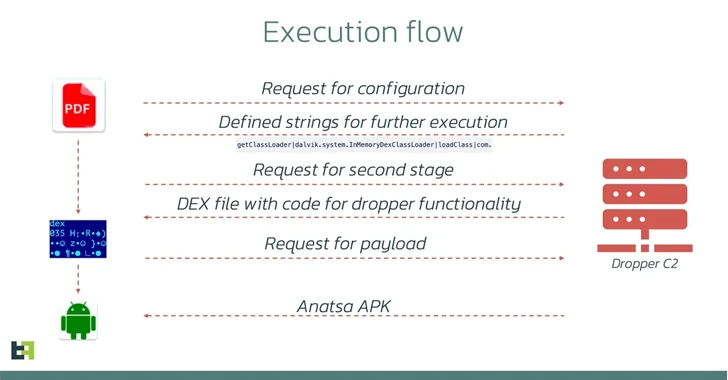
Also regarded by the identify TeaBot and Toddler, Anatsa is identified to be dispersed beneath the guise of seemingly innocuous applications on the Google Enjoy Shop. These applications, referred to as droppers, facilitate the set up of the malware by circumventing security measures imposed by Google that look for to grant sensitive permissions.
In June 2023, the Dutch cell security organization disclosed an Anatsa marketing campaign that targeted banking prospects in the U.S., the U.K., Germany, Austria, and Switzerland at least considering the fact that March 2023 utilizing dropper applications that had been collectively downloaded around 30,000 instances on the Enjoy Retailer.

Anatsa comes fitted with capabilities to attain whole regulate about infected gadgets and execute steps on a victim’s behalf. It can also steal qualifications to initiate fraudulent transactions.
The hottest iteration observed in November 2023 is no unique in that one of the droppers masqueraded as a phone cleaner app named “Phone Cleaner – File Explorer” (offer identify “com.volabs.androidcleaner”) and leveraged a approach termed versioning to introduce its destructive behavior.
Even though the application is no more time accessible for obtain from the formal storefront for Android, it can continue to be downloaded through other sketchy third-party sources.
According to statistics accessible on application intelligence system AppBrain, the app is believed to have been downloaded about 12,000 times throughout the time it was obtainable on the Google Enjoy Shop among November 13 and November 27, when it was unpublished.
“To begin with, the application appeared harmless, with no destructive code and its accessibility service not partaking in any destructive things to do,” ThreatFabric scientists claimed.
“Even so, a week right after its release, an update introduced destructive code. This update altered the AccessibilityService features, enabling it to execute destructive steps these kinds of as quickly clicking buttons once it gained a configuration from the [command-and-control] server.”
What helps make the dropper noteworthy is that its abuse of the accessibility services is personalized to Samsung equipment, suggesting that it was designed to exclusively target the firm-produced handsets at some stage, although other droppers used in the marketing campaign have been uncovered to be maker agnostic.
The droppers are also capable of circumventing Android 13’s restricted configurations by mimicking the course of action applied by marketplaces to put in new apps with no possessing their access to the accessibility provider functionalities disabled, as earlier noticed in the situation of dropper providers like SecuriDropper.

“These actors favor concentrated attacks on particular locations rather than a world wide unfold, periodically shifting their concentration,” ThreatFabric said. “This specific strategy permits them to focus on a limited number of economic businesses, main to a significant number of fraud cases in a brief time.”
The growth will come as Fortinet FortiGuard Labs in depth yet another marketing campaign that distributes the SpyNote remote accessibility trojan by imitating a legit Singapore-dependent cryptocurrency wallet provider recognized as imToken to exchange vacation spot wallet addresses and with actor-controlled kinds and conduct illicit asset transfers.
“Like much Android malware nowadays, this malware abuses the accessibility API,” security researcher Axelle Apvrille reported. “This SpyNote sample uses the Accessibility API to target well known crypto wallets.”
Discovered this posting interesting? Follow us on Twitter and LinkedIn to read through more exceptional written content we publish.
Some elements of this report are sourced from:
thehackernews.com


 Russian-Linked Hackers Breach 80+ Organizations via Roundcube Flaws
Russian-Linked Hackers Breach 80+ Organizations via Roundcube Flaws