Hundreds of WordPress sites employing a vulnerable variation of the Popup Builder plugin have been compromised with a malware termed Balada Injector.
Initially documented by Doctor Web in January 2023, the marketing campaign will take place in a sequence of periodic attack waves, weaponizing security flaws WordPress plugins to inject backdoor built to redirect visitors of infected web pages to bogus tech assistance pages, fraudulent lottery wins, and force notification cons.
Subsequent conclusions unearthed by Sucuri have discovered the enormous scale of the procedure, which is explained to have been lively considering that 2017 and infiltrated no much less than 1 million websites considering that then.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

The GoDaddy-owned web-site security company, which detected the most up-to-date Balada Injector activity on December 13, 2023, reported it identified the injections on around 7,100 websites.
These attacks choose advantage of a superior-severity flaw in Popup Builder (CVE-2023-6000, CVSS rating: 8.8) – a plugin with extra than 200,000 active installs – that was publicly disclosed by WPScan a working day just before. The issue was addressed in edition 4.2.3.
“When properly exploited, this vulnerability may enable attackers complete any motion the logged‑in administrator they qualified is permitted to do on the qualified web page, together with putting in arbitrary plugins, and producing new rogue Administrator people,” WPScan researcher Marc Montpas claimed.
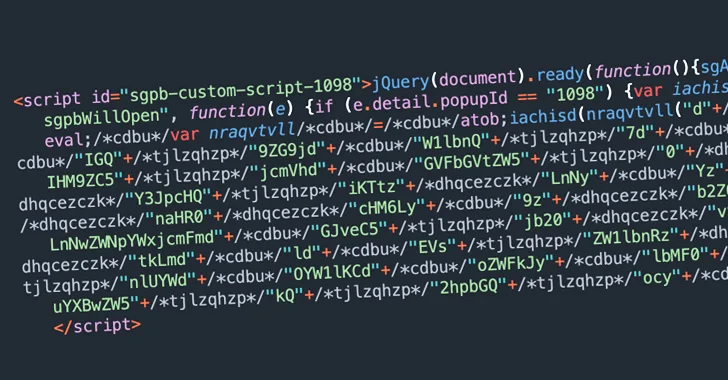
The ultimate intention of the marketing campaign is to insert a destructive JavaScript file hosted on specialcraftbox[.]com and use it to choose control of the internet site and load extra JavaScript in buy to aid malicious redirects.
In addition, the threat actors driving Balada Injector are recognised to create persistent management about compromised internet sites by uploading backdoors, adding malicious plugins, and generating rogue blog directors.
This is usually accomplished by using the JavaScript injections to precisely focus on logged-in internet site administrators.
“The strategy is when a blog administrator logs into a web page, their browser contains cookies that enable them to do all their administrative responsibilities without the need of getting to authenticate themselves on each new site,” Sucuri researcher Denis Sinegubko observed past 12 months.

“So, if their browser masses a script that tries to emulate administrator action, it will be ready to do virtually something that can be carried out by means of the WordPress admin interface.”
The new wave is no exception in that if logged-in admin cookies are detected, it weaponizes the elevated privileges to set up and activate a rogue backdoor plugin (“wp-felody.php” or “Wp Felody”) so as to fetch a next-phase payload from the aforementioned area.
The payload, one more backdoor, is saved beneath the identify “sasas” to the listing where by momentary data files are stored, and is then executed and deleted from disk.
“It checks up to three ranges previously mentioned the existing listing, searching for the root directory of the current web-site and any other websites that may possibly share the identical server account,” Sinegubko said.
“Then, in the detected website root directories, it modifies the wp-web site-header.php file to inject the exact same Balada JavaScript malware as was initially injected by means of the Popup Builder vulnerability.”
Found this post intriguing? Follow us on Twitter and LinkedIn to study extra unique content we write-up.
Some elements of this article are sourced from:
thehackernews.com

 DDoS Attacks on the Environmental Services Industry Surge by 61,839% in 2023
DDoS Attacks on the Environmental Services Industry Surge by 61,839% in 2023