The China-dependent risk actor known as Mustang Panda is suspected to have specific Myanmar’s Ministry of Defence and Foreign Affairs as element of twin strategies intended to deploy backdoors and remote accessibility trojans.
The results arrive from CSIRT-CTI, which said the routines took position in November 2023 and January 2024 after artifacts in relationship with the attacks have been uploaded to the VirusTotal platform.
“The most outstanding of these TTPs are the use of genuine application together with a binary produced by engineering agency Bernecker & Rainer (B&R) and a component of the Windows 10 enhance assistant to sideload destructive dynamic-link libraries (DLLs),” CSIRT-CTI said.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Mustang Panda, active given that at minimum 2012, is also acknowledged by the cybersecurity local community under the names BASIN, Bronze President, Camaro Dragon, Earth Preta, HoneyMyte, RedDelta, Red Lich, Stately Taurus, and TEMP.Hex.

In recent months, the adversary has been attributed to attacks concentrating on an unnamed Southeast Asian government as effectively as the Philippines to provide backdoors able of harvesting delicate information and facts.
The November 2023 an infection sequence begins with a phishing email bearing a booby-trapped ZIP archive attachment made up of a authentic executable (“Investigation of the third assembly of NDSC.exe”) that’s originally signed by B&R Industrial Automation GmbH and a DLL file (“BrMod104.dll”).
The attack requires benefit of the fact that the binary is susceptible to DLL lookup get hijacking to facet-load the rogue DLL and subsequently establish persistence and speak to with a command-and-control (C2) server and retrieve a known backdoor identified as PUBLOAD, which, in turn, acts as a tailor made loader to drop the PlugX implant.
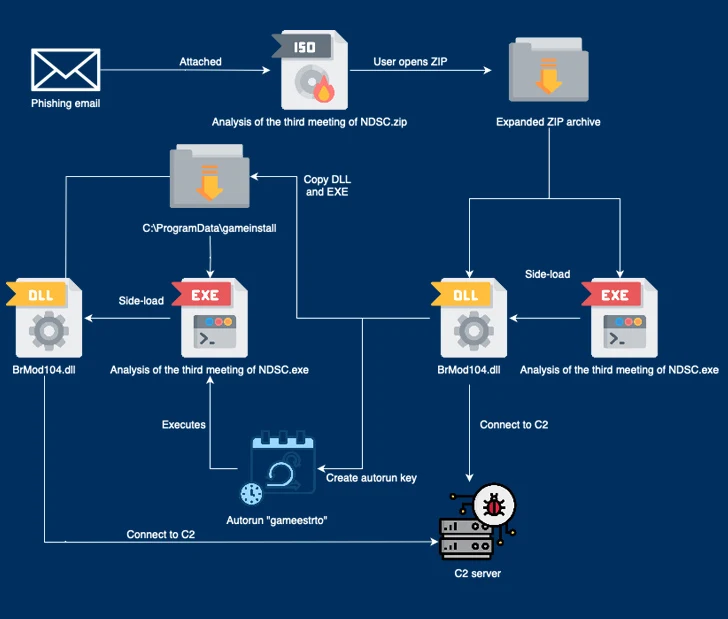
“The risk actors endeavor to disguise the [C2] website traffic as Microsoft update site visitors by including the ‘Host: www.asia.microsoft.com’ and ‘User-Agent: Windows-Update-Agent’ headers,” CSIRT-CTI mentioned, mirror a May possibly 2023 campaign disclosed by Lab52.
On the other hand, the second marketing campaign noticed before this month employs an optical disc graphic (“ASEAN Notes.iso”) that contains LNK shortcuts to result in a multi-stage process that makes use of yet another bespoke loader called TONESHELL to very likely deploy PlugX from a now-inaccessible C2 server.

It is really worth noting that a comparable attack chain attributed to Mustang Panda was beforehand unearthed by EclecticIQ in February 2023 in intrusions aimed at govt and community sector companies throughout Asia and Europe.
“Adhering to the rebel attacks in northern Myanmar [in October 2023], China has expressed concern about its effect on trade routes and security close to the Myanmar-China border,” CSIRT-CTI reported.
“Stately Taurus operations are recognised to align with geopolitical interests of the Chinese govt, such as numerous cyberespionage operations versus Myanmar in the earlier.”
Found this report intriguing? Observe us on Twitter and LinkedIn to study a lot more exclusive content material we submit.
Some parts of this posting are sourced from:
thehackernews.com

 493 Companies Share Their SaaS Security Battles – Get Insights in this WebinarJan 29, 2024SaaS Security / Webinar In today's digital world, security risks are more prevalent than ever, especially when it comes to Software as a Service (SaaS) applications. Did you know that an alarming 97% of companies face serious risks from unsecured SaaS applications? Moreover, about 20% of these organizations are struggling with internal data threats. These statistics aren't just numbers; they're a wake-up call. We're excited to invite you to a not-to-be-missed webinar, " Critical SaaS Security Do's and Don'ts: Insights from 493 Companies ," with Ran Senderovitz , the Chief Operating Officer of Wing Security. Ran isn't just going to talk about the problems; he's going to dive deep into the realities of SaaS security, backed by extensive research and data analysis from almost 500 companies using SaaS. Here's What This Webinar Offers: Insights Across Data, SaaS Applications, Users, and AI: Explore a comprehensive analysis of the statistics about SaaS security, di
493 Companies Share Their SaaS Security Battles – Get Insights in this WebinarJan 29, 2024SaaS Security / Webinar In today's digital world, security risks are more prevalent than ever, especially when it comes to Software as a Service (SaaS) applications. Did you know that an alarming 97% of companies face serious risks from unsecured SaaS applications? Moreover, about 20% of these organizations are struggling with internal data threats. These statistics aren't just numbers; they're a wake-up call. We're excited to invite you to a not-to-be-missed webinar, " Critical SaaS Security Do's and Don'ts: Insights from 493 Companies ," with Ran Senderovitz , the Chief Operating Officer of Wing Security. Ran isn't just going to talk about the problems; he's going to dive deep into the realities of SaaS security, backed by extensive research and data analysis from almost 500 companies using SaaS. Here's What This Webinar Offers: Insights Across Data, SaaS Applications, Users, and AI: Explore a comprehensive analysis of the statistics about SaaS security, di