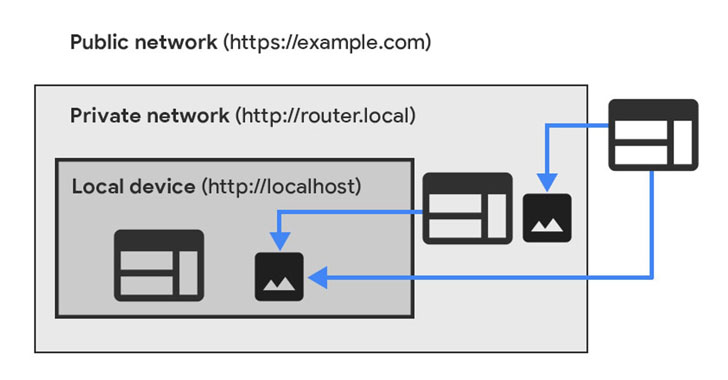
Google Chrome has declared plans to prohibit public internet websites from straight accessing endpoints found in just personal networks as component of an impending significant security shakeup to reduce intrusions by means of the browser.
The proposed adjust is set to be rolled out in two phases as aspect of releases Chrome 98 and Chrome 101 scheduled in the coming months through a newly implemented W3C specification known as non-public network accessibility (PNA).

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

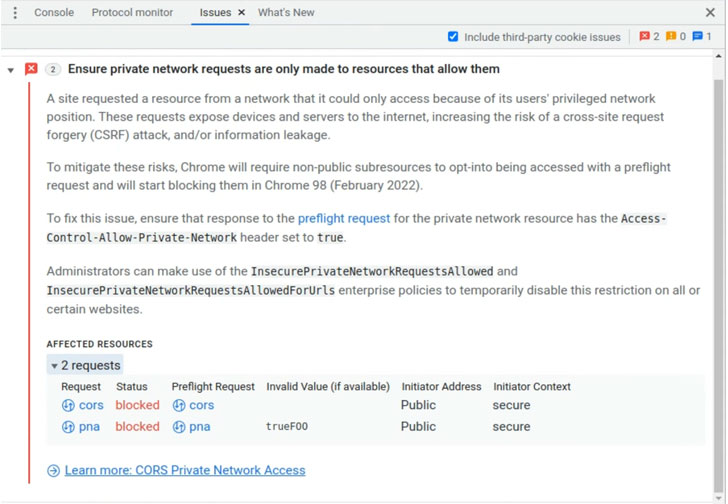
“Chrome will start out sending a CORS preflight request ahead of any private network ask for for a subresource, which asks for express permission from the focus on server,” Titouan Rigoudy and Eiji Kitamura claimed. “This preflight request will carry a new header, Access-Control-Ask for-Private-Network: accurate, and the response to it should carry a corresponding header, Access-Manage-Allow for-Personal-Network: legitimate.”
What this indicates is that starting up with Chrome model 101, any web page available by means of the internet will be created to find explicit authorization from the browser in advance of they can accessibility inside network assets. In other terms, the new PNA specification provides a provision inside the browser by which websites can ask for servers gated behind area networks to attain a connection.
“The specification also extends the Cross-Origin Resource Sharing (CORS) protocol so that web-sites now have to explicitly ask for a grant from servers on non-public networks right before becoming allowed to send arbitrary requests,” Rigoudy pointed out in August 2021, when it initial introduced plans to deprecate entry to non-public network endpoints from non-safe web-sites.
The target, the scientists mentioned, is to safeguard end users from cross-internet site ask for forgery (CSRF) attacks targeting routers and other units on non-public networks, which help bad actors to reroute unsuspecting people to destructive domains.
Uncovered this posting attention-grabbing? Stick to THN on Fb, Twitter and LinkedIn to read through extra distinctive articles we submit.
Some parts of this report are sourced from:
thehackernews.com



 Russia’s “politically motivated” REvil raid could be used as leverage, experts warn
Russia’s “politically motivated” REvil raid could be used as leverage, experts warn