U.S. cybersecurity and intelligence agencies have unveiled a set of suggestions to deal with security concerns with 5G standalone network slicing and harden them against achievable threats.
“The risk landscape in 5G is dynamic due to this, state-of-the-art monitoring, auditing, and other analytical abilities are expected to fulfill specific degrees of network slicing service stage necessities about time,” the U.S. Cybersecurity and Infrastructure Security Agency (CISA) and the Nationwide Security Agency (NSA) said.
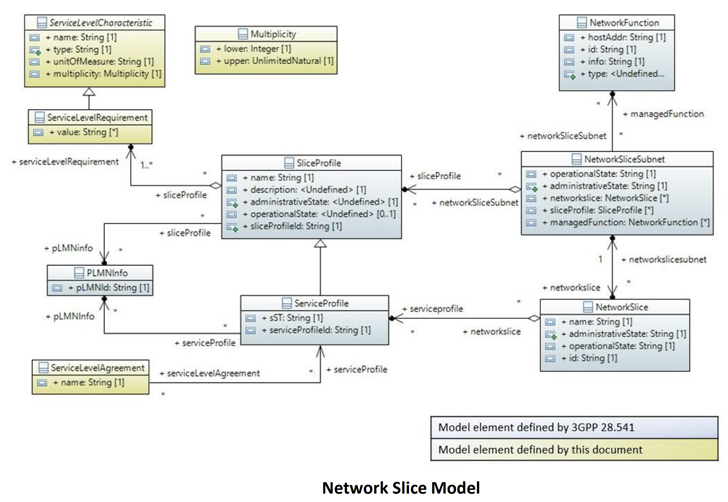
5G is the fifth-technology technology regular for broadband mobile networks, featuring elevated facts speeds and lower latency. Network slicing is an architectural model that lets cell service suppliers to partition their network up into several independent “slices” in purchase to develop digital networks that cater to diverse shoppers and use situations.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The most up-to-date advisory builds on assistance formerly issued by the businesses in December 2022, warning that network slicing could expose customers to a vast range of threat vectors – denial-of-support, jamming, id theft, and adversary-in-the-middle attacks – efficiently hampering the confidentiality, integrity, and the availability of network solutions.
Fears with 5G network slicing ended up comprehensive in a report released by Enea AdaptiveMobile Security in March 2021, which highlighted the likely for brute-pressure attacks to get destructive access to a slice and orchestrate denial-of-service attacks versus other network features.
Then in May perhaps 2021, the U.S. government cautioned that insufficient implementation of telecom expectations, source chain threats, and weaknesses in programs architecture could pose main cybersecurity dangers to 5G networks, thus allowing danger actors to exploit the loopholes to extract important intelligence from victims.
Impending WEBINARShield In opposition to Insider Threats: Learn SaaS Security Posture Management
Worried about insider threats? We’ve received you covered! Be a part of this webinar to check out sensible approaches and the tricks of proactive security with SaaS Security Posture Administration.
Be part of Currently
In the most current advice, the authorities cited denial-of-support attacks on the signaling plane, misconfiguration attacks, and adversary-in-the-center attacks as the three distinguished 5G threat vectors, noting that a zero have confidence in architecture (ZTA) can enable protected network deployments.
“A large element of ZTA can be completed by employing authentication, authorization, and audit (AAA) procedures,” CISA and NSA explained. “Good implementation of
authentication and authorization can also mitigate danger vectors stemming from misconfiguration attacks.”
The companies also stated it really is very important to understand field-recognized finest-tactics of how 5G network slicing can be implemented, built, deployed, operated, managed, possibly hardened, and mitigated as they impact Top quality of Services (QoS) and services level agreements (SLAs).
Found this short article intriguing? Observe us on Twitter and LinkedIn to read much more special content we post.
Some sections of this short article are sourced from:
thehackernews.com


 Chinese APT41 Hackers Target Mobile Devices with New WyrmSpy and DragonEgg Spyware
Chinese APT41 Hackers Target Mobile Devices with New WyrmSpy and DragonEgg Spyware