The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday additional a now-patched security flaw impacting Cisco Adaptive Security Appliance (ASA) and Firepower Risk Defense (FTD) computer software to its Regarded Exploited Vulnerabilities (KEV) catalog, following experiences that it truly is currently being probable exploited in Akira ransomware attacks.
The vulnerability in dilemma is CVE-2020-3259 (CVSS rating: 7.5), a significant-severity facts disclosure issue that could make it possible for an attacker to retrieve memory contents on an affected system. It was patched by Cisco as portion of updates introduced in May 2020.
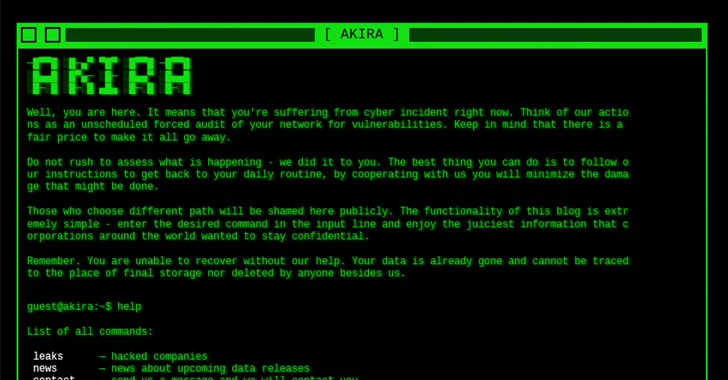
Late last thirty day period, cybersecurity firm Truesec explained it uncovered evidence suggesting that it has been weaponized by Akira ransomware actors to compromise multiple vulnerable Cisco Anyconnect SSL VPN appliances over the previous calendar year.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

“There is no publicly obtainable exploit code for […] CVE-2020-3259, which means that a danger actor, this kind of as Akira, exploiting that vulnerability would need to have to acquire or deliver exploit code by themselves, which calls for deep insights into the vulnerability,” security researcher Heresh Zaremand claimed.
According to Palo Alto Networks Unit 42, Akira is one of the 25 groups with freshly founded facts leak sites in 2023, with the ransomware group publicly boasting almost 200 victims. Initial observed in March 2023, the team is believed to share connections with the infamous Conti syndicate primarily based on the reality that it has despatched the ransom proceeds to Conti-affiliated wallet addresses.
In the fourth quarter of 2023 by yourself, the e-criminal offense group shown 49 victims on its facts leak portal, putting it powering LockBit (275), Engage in (110), ALPHV/BlackCat (102), NoEscape (76), 8Base (75), and Black Basta (72).
Federal Civilian Govt Branch (FCEB) businesses are essential to remediate identified vulnerabilities by March 7, 2024, to protected their networks against probable threats.
CVE-2020-3259 is considerably from the only flaw to be exploited for providing ransomware. Previously this month, Arctic Wolf Labs uncovered the abuse of CVE-2023-22527 – a just lately uncovered shortcoming in Atlassian Confluence Facts Heart and Confluence Server – to deploy C3RB3R ransomware, as very well as cryptocurrency miners and distant accessibility trojans.
The improvement arrives as the U.S. State Division declared rewards of up to $10 million for information and facts that could direct to the identification or area of BlackCat ransomware gang key users, in addition to featuring up to $5 million for info major to the arrest or conviction of its affiliate marketers.

The ransomware-as-a-support (RaaS) scheme, considerably like Hive, compromised in excess of 1,000 victims globally, netting at the very least $300 million in illicit income due to the fact its emergence in late 2021. It was disrupted in December 2023 pursuing an global coordinated procedure.
The ransomware landscape has come to be a lucrative industry, attracting the awareness of cybercriminals on the lookout for speedy money achieve, primary to the increase of new players these as Alpha (not to be puzzled with ALPHV) and Wing.
The U.S. Federal government Accountability Business (GAO), in a report printed to the close of January 2024, called for improved oversight into proposed tactics for addressing ransomware, especially for corporations from critical producing, strength, healthcare and public health and fitness, and transportation devices sectors.
Identified this post interesting? Observe us on Twitter and LinkedIn to go through far more distinctive content material we put up.
Some elements of this post are sourced from:
thehackernews.com

 RustDoor macOS Backdoor Targets Cryptocurrency Firms with Fake Job Offers
RustDoor macOS Backdoor Targets Cryptocurrency Firms with Fake Job Offers