A vast majority of surveyed CISOs stated that when shopping for cybersecurity seller methods, they value input from their peers very first and foremost – additional than analyst stories, vendor information or any other resource of data, in accordance to a freshly revealed research.
A joint venture of communications company Merritt Team and technology and Tech Exec Networks (T.E.N.), the study also discovered some of the finest and worst tactics when security sellers pitch their products to CISOs. 20-8 p.c of CISOs said that obtaining a phone connect with from an uninformed sales rep destroys any chance of setting up a business enterprise connection, when close to 34 % explained that sellers that try to recognize a company’s one of a kind suffering points stand a better probability of good results. (All percentages are rounded.)
See what a couple CISOs determined as their major likes and largest switch-offs when it comes to vendor advertising tactics.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Irrespective of its compact sample dimension (53 contributors), the survey influenced SC Media to achieve out to its very own business contacts to elicit their views. As it turns out, they share quite a few of the similar sentiments as these polled in the study, the results of which seem in Merritt Group’s official report, “Marketing and Marketing to the CISO,” 2020 version.
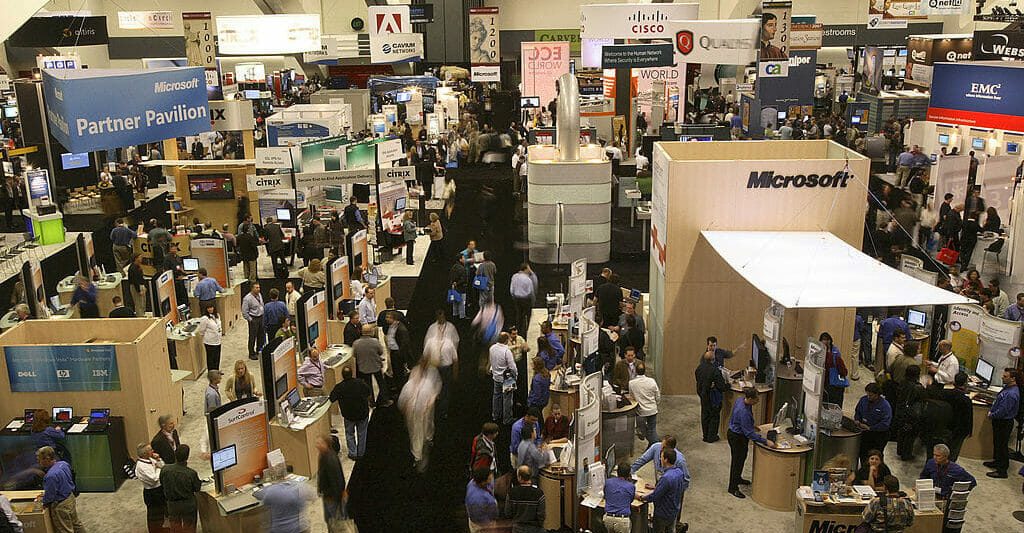
Amongst the CISOs who participated in the survey, 64 % reported they depend on their colleagues as their principal supply of information and facts pertaining to security solutions and distributors. The future most well-liked resources were being conferences and events (13 p.c) sector analyst reports (9 percent) and vendor material including webcasts and podcasts (eight %).
“Trusted term of mouth reigns supreme,” agreed Mark Eggleston, VP, main information security and privateness officer at Wellness Partners Plans, who reported he mainly depends on “trusted CISO or architects” for vendor suggestions. “CISOs are very occupied, and owning trusted thought leaders distill execs and downsides of any answer by means of functional experience is pure gold,” he extra.
On the other hand, “Events, analysts, webinars, podcasts are all compensated for and get lost in the sound of what is worthwhile or not,” reported Caleb Sima, VP of security at Databricks.
Sima explained he discusses the vendor landscape “almost weekly by way of CISO Slack teams.” Other great boards for achieving out to peers, according to Eggleston, are conferences, sponsored meetups, organized dinners, and even LinkedIn “if you do a terrific career cultivating your network.”
Neil Daswani, co-director of the Stanford Highly developed Security Program at Stanford University, and a former CISO at Symantec, mentioned peer recommendations can be a big time-saver.
“If a security seller has assisted 1 CISO achieve good results with mitigating risk, likelihood are they will be in a position to enable other CISOs in equivalent vertical industries with mitigating dangers,” reported Daswani. “There is a course of early adopter CISOs that direct the pack in their discipline and try out out new options first, which other CISOs might emulate and adhere to based on peer consultation.”
Gerald Beuchelt, CISO at LogMeIn, agreed that hearing from friends with “actual arms-on experience” with a particular alternative “is tremendously worthwhile and can’t be changed with even a very detailed examination or evidence-of-notion,” frequently due to the fact complex evaluations like these just can’t always “address the quite a few edge cases that existing themselves in authentic-planet environments.”
“In addition, real practitioners also have a considerably greater perception of issues that are not automatically specifically related to the capabilities or functionality of the technology, including precise vendor assistance effectiveness, user acceptance, or other secondary and tertiary problems,” Beuchelt continued.
When hunting to be educated on industry traits, field colleagues are once more remarkably valued: 43 percent of surveyed CISOs ranked peer exchange as their best source of these kinds of facts, whilst 28 p.c claimed they examine investigation studies and 13 p.c claimed they change to video clips and webinars, reported Merritt Team.
Analyst stories: flawed, but continue to valuable
The report suggests that vendors preventing investing in field analyst stories, noting that CISOs seem to be to be especially skeptical of them for the reason that option suppliers from time to time pay out for inclusion. “This process has hurt the trustworthiness of business analyst stories, and as a result the impression they have on CISO acquiring actions,” the report claims.
On the other hand, here the CISOs who spoke with SC Media somewhat disagreed.
“True, beware of pay out-to-enjoy organizations. However, really do not fully lower price them,” reported Eggleston. “Just confirm the source’s angle first prior to listening to their sell. They’ll know you are not a pushover. Another tip is talk to: ‘How do you make your cash?’ That solution right there will explain to you if they are swaying you to advantage themselves, not you.”
Sima termed analyst experiences “a vital evil” that can confirm valuable. “If I really don’t know who the players are in the area, I can use them to get a great strategy of in which to get started and roughly the top rated players,” he mentioned. “If you’re an org that relies upon on paying for ‘safe’ vendors then this is great. If you want to be slicing edge and see outside of the horizon, they are not valuable.”
On the other hand, Eggleston explained that any “white paper is ordinarily vendor-sponsored garbage… They’ve definitely gotten a undesirable title. CISOs see ideal by way of that, and when I get a get in touch with for a cost-free white paper via phone, my typical response is to hold up the phone.”
In the report, CISOs expressed specific articles structure choices when a vendor is supplying the promoting materials. Amongst the study respondents, the major alternative of seller content material structure was roundtable occasions and dinners (38 %), followed by webinars (15 percent), white papers and ebooks (15 per cent) and circumstance experiments (13 per cent).
Only 4 p.c mentioned they chiefly rely on seller advertising and marketing collateral such as revenue sheets and brochures. But there are ways distributors could get to boost their believability, reported 1 of the men.
“…[G]ood sellers can perform scientific, information-pushed scientific studies that communicate to their rewards,” stated Daswani. Any seller will, of system, worry their rewards. If they can do so with facts, that is an essential element of the story. But only component of the story. If suppliers can be open about what are their products’ trade-offs as in comparison to their rivals, they can existing a well balanced as a substitute of a biased story.”
“Advertising, promoting, pay back-to-participate in analyst studies, and identical material can be a valuable aspect of analyzing a merchandise or a alternative,” mentioned Beuchelt. “This is significantly legitimate when these elements are concentrated on supplying context and material and do not emphasis on ‘high-gloss features’ or buzzwords.”
“Interestingly more than enough, actual product manuals are usually most handy for me to actually gauge abilities and usability of a products. But it is pretty vital to place matters into standpoint and make absolutely sure that other extra well balanced or even unfavorable resources are also taken into consideration” Beuchelt continued.
But what Daswani would genuinely like to see a lot more of often isn’t out there: “I do believe it is critical to have more goal, scientific research [of cyber solutions] to be carried out by labs, universities, and consultants in get for our subject to advance,” he reported. “Security vendors need to remove clauses in their contracts that stop prospects and other people from accomplishing goal evaluations and publishing the results. Can you consider what the airline or pharmaceutical industries would be like if options could not be correctly evaluated by deal?”
How vendors can make a excellent or terrible perception
The surveyed CISOs also lose light on what vendor behaviors can perhaps aid seal a deal or damage a marriage. In addition to being familiar with and addressing companies’ particular suffering points, the execs also said they valued when suppliers steer clear of utilizing FUD (panic, uncertainty and question) in their pitches (26 per cent) and when they guide with person circumstance experiments that are pertinent to their corporations (23 %).
The major three transform-offs have been abnormal email advertising and marketing (30 percent), cold contacting (25 percent) and making an attempt to circumvent the CISO and converse with a better-stage govt (19 percent).
(The CISOs whom SC Media spoke with also shared some of their very own favourite vendor techniques and turnoffs. See below for more particulars.)
But are option suppliers listening, and are they modifying their marketing and advertising approaches in accordance with CISO’s tastes?
Mark Nunnikhoven, VP of cloud analysis at TrendMicro, reported he agrees that CISOs “don’t have added time on their fingers and traditional seller pitches are a waste of their time. This is why peer information is so beneficial. It’s trustworthy, open, and concise. CISOs need no-bull, technical data.”
“This necessitates a shift in how you sector to CISOs,” Nunnikhoven continued. “It’s not so substantially marketing as schooling of where by vendors’ products would be a great healthy and where they aren’t. Suppliers need to have sincere conversations with CISOs and be sincere about their offers’ strengths and weaknesses as concisely as attainable.”
Nunnikhoven thinks vendors’ complex weblogs can be a beneficial communications software for CISOs to reference. “It shows the needed know-how in a security place, is quickly searchable, and sales opportunities with the most critical component: the dilemma the CISO is facing and attainable options for it,” he reported.
Corey Nachreiner, CTO at WatchGuard Technologies, explained the the report “seems to seize the methods an common CISO would price,” but he thinks some of the study responses could have differed if the researchers had expanded their pool of respondents outside of basically CISOs.
“First, CISOs are typically only located at enterprises or upper midmarket businesses, so this report does not seriously go over what sources other security-concentrated consumers might benefit,” stated Nachreiner. “And there are far more specialized, fewer small business-targeted security qualified personas, both on the CISO’s team and during an firm, that can have affect on acquiring decisions that would have a little bit distinctive characteristics. For occasion, security analysts or incident handlers reporting to a CISO could possibly obtain much more worth in resources like podcasts, social media, and matter issue discussion boards.”
“Furthermore, because of its company concentrate, the report also misses the SMB dynamic where MSPs and MSSPs serve as trusted third-occasion advisors for security customers in non-enterprise organizations. And if the report went even even more down the choice-building stack, the effects would possible differ a lot more substantially. As a CISO myself, I tend to benefit ebooks, specialized papers, and responses from my staff and colleagues more than something else.”

 Twitter Hack Update: What We Know (and What We Do not)
Twitter Hack Update: What We Know (and What We Do not)