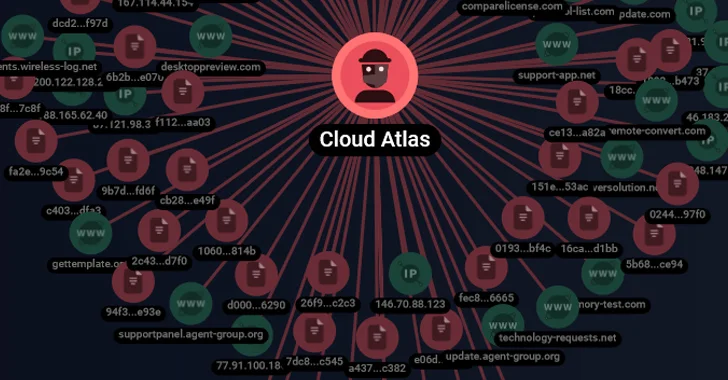
The danger actor referred to as Cloud Atlas has been joined to a established of spear-phishing attacks on Russian enterprises.
Targets provided a Russian agro-industrial organization and a condition-owned research business, according to a report from F.A.C.C.T., a standalone cybersecurity enterprise fashioned after Group-IB’s formal exit from Russia before this 12 months.
Cloud Atlas, energetic considering that at least 2014, is a cyber espionage group of unidentified origin. Also identified as Clean Ursa, Inception, Oxygen, and Pink Oct, the risk actor is regarded for its persistent strategies targeting Russia, Belarus, Azerbaijan, Turkey, and Slovenia.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
In December 2022, Test Position and Good Systems thorough multi-stage attack sequences that led to the deployment of a PowerShell-based mostly backdoor referred to as PowerShower as well as DLL payloads able of speaking with an actor-managed server.
Approaching WEBINAR From Person to ADMIN: Master How Hackers Get Total Handle
Find the magic formula techniques hackers use to develop into admins, how to detect and block it before it is really far too late. Register for our webinar now.
Be a part of Now
The starting up level is a phishing message bearing a lure doc that exploits CVE-2017-11882, a 6-year-old memory corruption flaw in Microsoft Office’s Equation Editor, to kick-commence the execution of destructive payloads, a procedure Cloud Atlas has employed as early as October 2018.

“The actor’s massive spear-phishing campaigns continue on to use its uncomplicated but powerful approaches in purchase to compromise its targets,” Kaspersky mentioned in August 2019. “In contrast to several other intrusion sets, Cloud Atlas has not preferred to use open resource implants through its modern strategies, in get to be a lot less discriminating.”
F.A.C.C.T. explained the most recent get rid of chain as very similar to the just one described by Good Technologies, with effective exploitation of CVE-2017-11882 by using RTF template injection paving the way for shellcode that’s dependable for downloading and running an obfuscated HTA file. The mails originate from well-known Russian email services Yandex Mail and VK’s Mail.ru.
The destructive HTML software subsequently launches Visible Essential Script (VBS) information that are in the long run liable for retrieving and executing an unknown VBS code from a distant server.

“The Cloud Atlas group has been lively for many many years, very carefully considering by each and every part of their attacks,” Constructive Technologies claimed of the group very last yr.
“The group’s toolkit has not improved for years—they attempt to disguise their malware from researchers by using one particular-time payload requests and validating them. The group avoids network and file attack detection applications by using reputable cloud storage and very well-documented application capabilities, in specific in Microsoft Business office.”
The progress arrives as the company stated that at the very least 20 corporations positioned in Russia have been compromised working with Decoy Doggy, a modified version of Pupy RAT, attributing it to an innovative persistent threat actor it calls Hellhounds.
The actively taken care of malware, in addition to allowing the adversary to remotely handle the infected host, arrives with a scriptlet developed to transmit telemetry information to an “automated” account on Mastodon with the identify “Lamir Hasabat” (@lahat) on the Mindly.Social instance.
“Following components on the to start with version of Decoy Canine were released, the malware authors went to a great deal of effort to hamper its detection and investigation each in traffic and in the file method,” security researchers Stanislav Pyzhov and Aleksandr Grigorian explained.
Discovered this post exciting? Abide by us on Twitter and LinkedIn to examine extra exceptional content material we put up.
Some elements of this posting are sourced from:
thehackernews.com

 British LAPSUS$ Teen Members Sentenced for High-Profile Attacks
British LAPSUS$ Teen Members Sentenced for High-Profile Attacks