A severe privilege escalation issue impacting MikroTik RouterOS could be weaponized by distant malicious actors to execute arbitrary code and seize total control of vulnerable units.
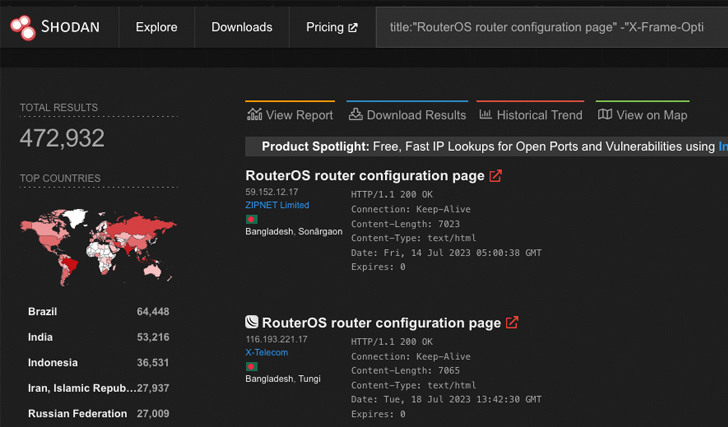
Cataloged as CVE-2023-30799 (CVSS score: 9.1), the shortcoming is expected to put approximately 500,000 and 900,000 RouterOS units at risk of exploitation by means of their web and/or Winbox interfaces, respectively, VulnCheck disclosed in a Tuesday report.
“CVE-2023-30799 does involve authentication,” security researcher Jacob Baines mentioned. “In actuality, the vulnerability itself is a straightforward privilege escalation from admin to ‘super-admin’ which effects in accessibility to an arbitrary perform. Getting credentials to RouterOS systems is less complicated than one particular may possibly expect.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
This is due to the fact the Mikrotik RouterOS functioning method does not supply any safety versus password brute-pressure attacks and ships with a nicely-regarded default “admin” person, with its password staying an vacant string until finally October 2021, at which level administrators ended up prompted to update the blank passwords with the launch of RouterOS 6.49.
CVE-2023-30799 is reported to have been initially disclosed by Margin Exploration as an exploit dubbed FOISted with out an accompanying CVE identifier in June 2022. The security gap, even so, was not plugged until eventually Oct 13, 2022, in the RouterOS secure model 6.49.7 and on July 19, 2023, for the RouterOS Extensive-phrase variation 6.49.8.
VulnCheck famous that a patch for the Long-time period release tree was manufactured out there only after it directly contacted the vendor and “printed new exploits that attacked a wider assortment of MikroTik components.”
A proof-of-notion (PoC) devised by the firm reveals that it’s possible to derive a new MIPS architecture-dependent exploit chain from FOISted and receive a root shell on the router.
Forthcoming WEBINARShield Against Insider Threats: Grasp SaaS Security Posture Management
Apprehensive about insider threats? We’ve received you lined! Sign up for this webinar to discover useful approaches and the secrets and techniques of proactive security with SaaS Security Posture Administration.
Be a part of Today
“Given RouterOS’ long record of being an APT concentrate on, put together with the actuality that FOISted was launched very well in excess of a year in the past, we have to believe we aren’t the 1st team to figure this out,” Baines noted.
“Regretably, detection is practically not possible. The RouterOS web and Winbox interfaces carry out custom made encryption techniques that neither Snort or Suricata can decrypt and inspect. At the time an attacker is set up on the gadget, they can quickly make by themselves invisible to the RouterOS UI.”
With flaws in Mikrotik routers exploited to corral the gadgets into distributed denial-of-services (DDoS) botnets these kinds of as Mēris and use them as command-and-control proxies, it really is advisable that people patch the flaw by updating to the most current model (6.49.8 or 7.x) as soon as possible.
Mitigation tips contains eliminating MikroTik administrative interfaces from the internet, restricting the IP addresses directors can login from, disabling the Winbox and the web interfaces, and configuring SSH to use general public/personal keys and disable passwords.
Observed this article attention-grabbing? Adhere to us on Twitter and LinkedIn to read a lot more exclusive articles we post.
Some components of this report are sourced from:
thehackernews.com


 North Korean Nation-State Actors Exposed in JumpCloud Hack After OPSEC Blunder
North Korean Nation-State Actors Exposed in JumpCloud Hack After OPSEC Blunder