A new zero-day security flaw has been found out in the Apache OfBiz, an open-resource Company Useful resource Setting up (ERP) procedure that could be exploited to bypass authentication protections.
The vulnerability, tracked as CVE-2023-51467, resides in the login features and is the outcome of an incomplete patch for an additional critical vulnerability (CVE-2023-49070, CVSS rating: 9.8) that was launched earlier this month.
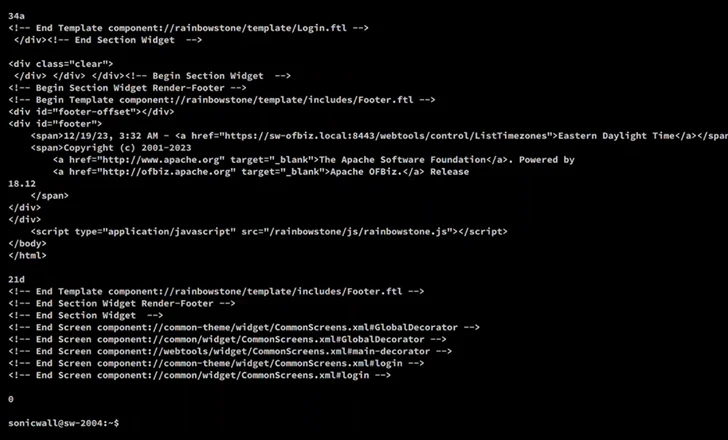
“The security measures taken to patch CVE-2023-49070 left the root issue intact and consequently the authentication bypass was still existing,” the SonicWall Capture Labs menace analysis group, which discovered the bug, stated in a assertion shared with The Hacker News.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
CVE-2023-49070 refers to a pre-authenticated remote code execution flaw impacting versions prior to 18.12.10 that, when correctly exploited, could permit risk actors to obtain comprehensive command over the server and siphon delicate details. It is prompted owing to a deprecated XML-RPC component inside of Apache OFBiz.
According to SonicWall, CVE-2023-51467 could be induced using empty and invalid USERNAME and PASSWORD parameters in an HTTP ask for to return an authentication results information, efficiently circumventing the protection and enabling a danger actor to accessibility usually unauthorized interior methods.

The attack hinges on the truth that the parameter “requirePasswordChange” is established to “Y” (i.e., yes) in the URL, triggering the authentication to be trivially bypassed irrespective of the values handed in the username and password fields.
“The vulnerability enables attackers to bypass authentication to realize a basic Server-Aspect Ask for Forgery (SSRF),” according to a description of the flaw on the NIST National Vulnerability Database (NVD).
Consumers who rely on Apache OFbiz to update to variation 18.12.11 or afterwards as quickly as feasible to mitigate any probable threats.
Observed this posting appealing? Comply with us on Twitter and LinkedIn to study extra distinctive written content we put up.
Some pieces of this posting are sourced from:
thehackernews.com


 Chinese Hackers Exploited New Zero-Day in Barracuda’s ESG Appliances
Chinese Hackers Exploited New Zero-Day in Barracuda’s ESG Appliances