Zero-day vulnerabilities in Windows Installers for the Atera distant checking and administration application could act as a springboard to launch privilege escalation attacks.
The flaws, learned by Mandiant on February 28, 2023, have been assigned the identifiers CVE-2023-26077 and CVE-2023-26078, with the issues remediated in variations 1.8.3.7 and 1.8.4.9 produced by Atera on April 17, 2023, and June 26, 2023, respectively.
“The skill to initiate an procedure from a NT AUTHORITYSYSTEM context can current likely security hazards if not effectively managed,” security researcher Andrew Oliveau explained. “For occasion, misconfigured Customized Actions running as NT AUTHORITYSYSTEM can be exploited by attackers to execute neighborhood privilege escalation attacks.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Successful exploitation of such weaknesses could pave the way for the execution of arbitrary code with elevated privileges.
Each the flaws reside in the MSI installer’s fix operation, likely producing a circumstance in which operations are induced from an NT AUTHORITYSYSTEM context even if they are initiated by a regular consumer.
According to the Google-owned risk intelligence agency, Atera Agent is inclined to a regional privilege escalation attack that can be exploited as a result of DLL hijacking (CVE-2023-26077), which could then be abused to receive a Command Prompt as the NT AUTHORITYSYSTEM person.
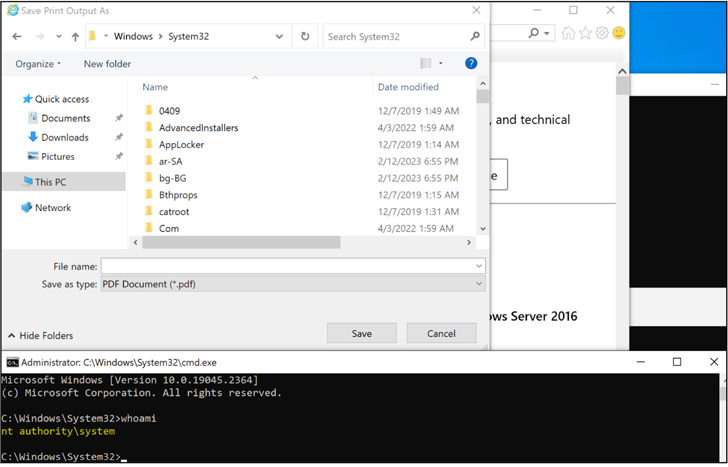
CVE-2023-26078, on the other hand, issues the “execution of program commands that induce the Windows Console Host (conhost.exe) as a kid method,” as a end result opening up a “command window, which, if executed with elevated privileges, can be exploited by an attacker to carry out a nearby privilege escalation attack.”
“Misconfigured Tailor made Actions can be trivial to recognize and exploit, therefore posing important security risks for organizations,” Oliveau reported. “It is vital for software package developers to completely assessment their Custom made Actions to stop attackers from hijacking NT AUTHORITYSYSTEM operations induced by MSI repairs.”
Forthcoming WEBINARShield Versus Insider Threats: Master SaaS Security Posture Administration
Apprehensive about insider threats? We’ve received you included! Join this webinar to examine useful tactics and the techniques of proactive security with SaaS Security Posture Administration.
Be a part of Now
The disclosure comes as Kaspersky shed additional gentle on a now-fastened, significant privilege escalation flaw in Windows (CVE-2023-23397, CVSS rating: 9.8) that has arrive under energetic exploitation in the wild by risk actors employing a specifically crafted Outlook activity, information or calendar celebration.
When Microsoft disclosed previously that Russian country-condition groups weaponized the bug considering that April 2022, evidence collected by the antivirus vendor has uncovered that actual-planet exploit attempts had been carried out by an not known attacker focusing on governing administration and critical infrastructure entities in Jordan, Poland, Romania, Turkey, and Ukraine a thirty day period prior to the public disclosure.
Identified this article appealing? Adhere to us on Twitter and LinkedIn to read more unique written content we post.
Some components of this article are sourced from:
thehackernews.com


 Google Messages Getting Cross-Platform End-to-End Encryption with MLS Protocol
Google Messages Getting Cross-Platform End-to-End Encryption with MLS Protocol