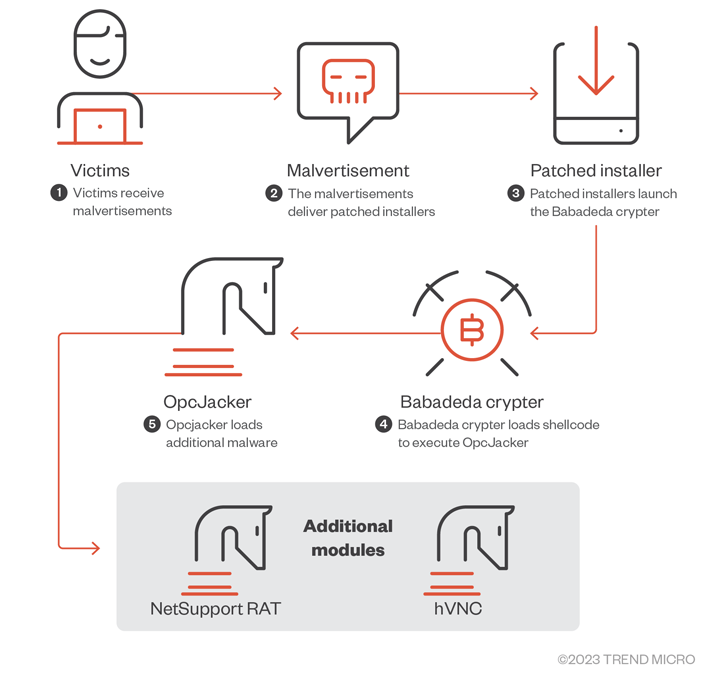
A piece of new details-thieving malware named OpcJacker has been spotted in the wild considering the fact that the next half of 2022 as element of a malvertising campaign.
“OpcJacker’s key functions include keylogging, getting screenshots, stealing delicate information from browsers, loading supplemental modules, and changing cryptocurrency addresses in the clipboard for hijacking applications,” Craze Micro scientists Jaromir Horejsi and Joseph C. Chen mentioned.
The original vector of the campaign requires a network of faux internet sites promotion seemingly innocuous software package and cryptocurrency-relevant programs. The February 2023 campaign particularly singled out people in Iran less than the pretext of providing a VPN services.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The installer documents act as a conduit to deploy OpcJacker, which is also able of offering next-phase payloads this sort of as NetSupport RAT and a hidden virtual network computing (hVNC) variant for remote entry.
OpcJacker is hid making use of a crypter regarded as Babadeda and would make use of a configuration file to activate its information harvesting features. It can also run arbitrary shellcode and executables.
“The configuration file format resembles a bytecode created in a customized equipment language, where each instruction is parsed, particular person opcodes are attained, and then the distinct handler is executed,” Craze Micro reported.
Provided the malware’s potential to steal crypto money from wallets, the strategies are suspected to be monetarily-motivated. That stated, OpcJacker’s versatility also would make it an great malware loader.
THN WEBINARBecome an Incident Reaction Pro!
Unlock the techniques to bulletproof incident reaction – Grasp the 6-Stage course of action with Asaf Perlman, Cynet’s IR Chief!
Don’t Skip Out – Help save Your Seat!
The findings occur as Securonix revealed details of an ongoing attack marketing campaign dubbed TACTICAL#OCTOPUS that targets U.S. entities with tax-themed lures to infect them with backdoors to achieve accessibility to victim methods as perfectly as seize clipboard knowledge and keystrokes.
In a associated advancement, Italian and French users looking for cracked versions of Personal computer servicing application such as EaseUS Partition Grasp and Driver Easy Pro on YouTube are becoming redirected to Blogger pages distributing the NullMixer dropper.
NullMixer also stands out for concurrently dropping a vast range of off-the-shelf malware, which includes PseudoManuscrypt, Raccoon Stealer, GCleaner, Fabookie, and a new malware loader referred to as Crashtech Loader, main to huge-scale infections.
Uncovered this post interesting? Abide by us on Twitter and LinkedIn to study extra special written content we put up.
Some components of this post are sourced from:
thehackernews.com

 Western Digital suffers cyber attack, shuts down systems
Western Digital suffers cyber attack, shuts down systems