Getty Images
Cyber legal teams have been observed to be attracting hackers and tech pros alike with white-collar employment advantages and enormous salaries as high as $1.2 million.
Assessment from Kaspersky uncovered that the spike in cyber criminal offense over the previous two years has prompted some groups to accelerate selecting to hold pace with desire.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Scientists at the agency analysed additional than 200,000 work adverts posted on dark web webpages in between January 2020 and June 2022.
The consequence concluded that the quantity of advertisements enhanced speedily in the course of the onset of the pandemic, surpassing an ordinary of 10,000 advertisements for each quarter – a determine that peaked in March 2020.
“A total of around 200,000 employment-associated advertisements ended up posted on the dark web all through the period of time in query,” scientists explained. “The most significant range of these, or 41% of the whole, have been posted in 2020.”
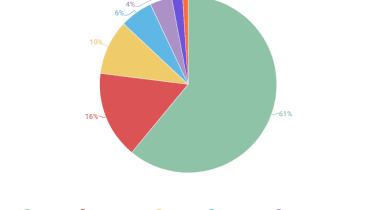
Distribution of dark web occupation advertisements across specialisations
Kaspersky
Posting exercise peaked in March 2020, quite possibly prompted by a pandemic-related profits fall expert by component of the inhabitants,” the security agency added.
Dedicated ‘hacker’ roles weren’t the only spot in which cyber prison teams ended up found to be looking for further know-how.
Teams significantly sought out personnel to fill developer, admin, and designer positions even though other in-demand from customers roles included program engineers and network testers.
Work ads searching for builders were the most regular, the examine revealed, accounting for 61% of the whole. Similarly, developers also topped the list of the ideal-compensated dark web-sourced IT roles, with the greatest monthly salary standing at $20,000.
Staff incentives
Dark web career listings highlighted by Kaspersky bore similarities to an common tech sector task advert. Teams in search of new starts off often supplied a selection of incentives such as holiday getaway spend, flexible doing work several hours, and future employee referral bonuses.
“Employers on the dark web request to catch the attention of applications by giving favourable phrases of employment, between other things,” researchers mentioned. “The most often outlined pros provided remote do the job, comprehensive-time employment, and flextime.”
“You can also occur throughout compensated time off, paid out ill leaves, and even ‘a friendly team’ detailed among the phrases of work.”
Some teams have been also observed to perform common efficiency testimonials, researchers found. This follow was commonplace in the Conti cyber crime team and saw personnel granted bonuses dependent on exemplary efficiency or fines due to weak productivity.
Risk and reward
The reasoning behind some dark web buyers in search of roles can vary, scientists suggested. Some may possibly be trying to get choice earnings streams though many others may perhaps have misplaced careers in the course of the onset of the pandemic in 2020.
“People could have various reasons for likely to a dark web web site to seem for a work. Several are drawn by anticipations of effortless money and large fiscal achieve,” scientists wrote.
The analyze also noted that whilst some employment advertised on the dark web offered far more than what an unique could make lawfully, there was little variation amongst the ordinary level of IT professionals’ pay out on each sides of the lawful divide.

Median month-to-month IT salaries on the dark web
Kaspersky
“Although dark web work could be anticipated to pay larger than genuine types, we did not detect a substantial variation among the median stages of IT professionals’ payment in the cyber legal ecosystem and the authentic position market place.”
Accelerating functions
Rik Ferguson, VP of Security Intelligence at Forescout instructed IT Pro this analysis highlights the rising sophistication of cyber criminal teams and their demand for technical knowledge across a vary of fields.
“For a lot of decades now, cyber crime has been a really distributed and specialised industry. Just one criminal gang may agreement out certain necessities to unbiased specialists offering products and services this kind of as “crypting”, escrow, money mules, coding and many more,” he reported.
“Recently even though, some of the much more set up and prosperous ransomware menace actors (LockBit for example) have employed industry experts, specially in software progress, right into their operation.”
Ferguson added that this recruitment pattern could be because of to a need to make improvements to operational effectiveness and maximise the effects of offensive capabilities.
“Some of this is for performance, the potential to regulate the advancement of a a lot more efficient “product” and consequently recruit additional affiliate marketers to spread the ransomware,” he mentioned. “Some of it may well be pushed by competitive and confidentiality considerations all-around trying to keep their operation insulated, both of those from their legal competitors and from legislation enforcement.”
Some components of this report are sourced from:
www.itpro.co.uk


 New Report Reveals NikoWiper Malware That Targeted Ukraine Energy Sector
New Report Reveals NikoWiper Malware That Targeted Ukraine Energy Sector