Threat actors are actively exploiting a not long ago disclosed critical security flaw in the WooCommerce Payments WordPress plugin as element of a substantial focused campaign.
The flaw, tracked as CVE-2023-28121 (CVSS score: 9.8), is a case of authentication bypass that allows unauthenticated attackers to impersonate arbitrary buyers and carry out some steps as the impersonated consumer, including an administrator, most likely foremost to internet site takeover.
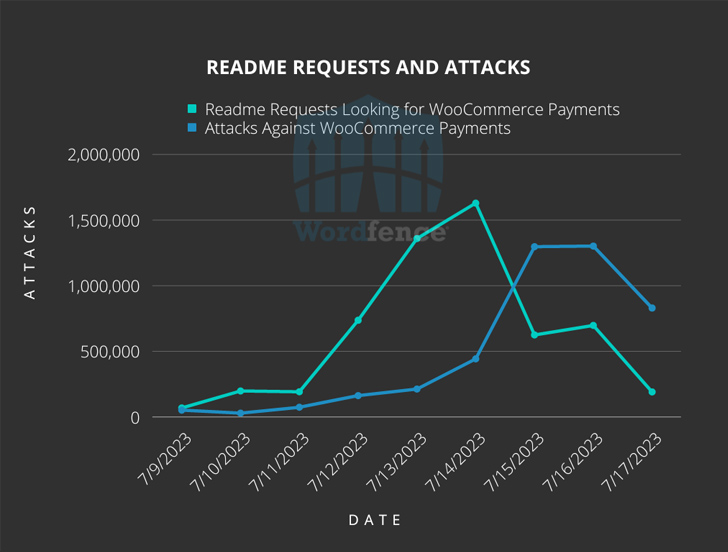
“Huge-scale attacks from the vulnerability, assigned CVE-2023-28121, commenced on Thursday, July 14, 2023 and ongoing about the weekend, peaking at 1.3 million attacks from 157,000 web sites on Saturday, July 16, 2023,” Wordfence security researcher Ram Gall said in a Monday submit.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Versions 4.8. by 5.6.1 of WooCommerce Payments are vulnerable. The plugin is put in on in excess of 600,000 sites. Patches for the bug had been released by WooCommerce back in March 2023, with WordPress issuing auto-updates to websites working with influenced variations of the application.
A widespread denominator observed in the attacks involves the use of the HTTP request header “X-Wcpay-System-Checkout-Person: 1” that will cause susceptible sites to treat any further payloads as coming from an administrative consumer.
Wordfence explained the aforementioned loophole is currently being weaponized to deploy the WP Console plugin, which can be applied by an administrator to execute destructive code and set up a file uploader to established up persistence and backdoor the compromised web site.
Adobe ColdFusion Flaws Exploited in the Wild
The disclosure will come as Immediate7 reported that it observed active exploitation of Adobe ColdFusion flaws in various client environments starting off July 13, 2023, to deploy web shells on contaminated endpoints.
“Danger actors show up to be exploiting CVE-2023-29298 in conjunction with a secondary vulnerability,” Fast7 security researcher Caitlin Condon mentioned. The further flaw appears to be CVE-2023-38203 (CVSS rating: 9.8), a deserialization flaw that was dealt with in an out-of-band update launched on July 14.
Upcoming WEBINARShield Against Insider Threats: Learn SaaS Security Posture Management
Anxious about insider threats? We’ve received you lined! Be part of this webinar to take a look at simple methods and the secrets of proactive security with SaaS Security Posture Management.
Sign up for Nowadays
CVE-2023-29298 (CVSS score: 7.5) problems an access control bypass vulnerability impacting ColdFusion 2023, ColdFusion 2021 Update 6 and below, and ColdFusion 2018 Update 16 and below.
“The vulnerability allows an attacker to obtain the administration endpoints by inserting an unforeseen additional forward slash character in the requested URL,” Swift7 disclosed last 7 days.
Fast7, however, warned that the resolve for CVE-2023-29298 is incomplete and that it could be trivially modified to bypass the patches unveiled by Adobe.
People are encouraged to update to the hottest variation of Adobe ColdFusion to safe versus possible threats, given that the fixes place in location to take care of CVE-2023-38203 breaks the exploit chain.
Located this article interesting? Follow us on Twitter and LinkedIn to read through more distinctive articles we publish.
Some pieces of this report are sourced from:
thehackernews.com


 JumpCloud Blames ‘Sophisticated Nation-State’ Actor for Security Breach
JumpCloud Blames ‘Sophisticated Nation-State’ Actor for Security Breach