An analysis of firmware pictures across equipment from Dell, HP, and Lenovo has uncovered the existence of out-of-date versions of the OpenSSL cryptographic library, underscoring a supply chain risk.
EFI Progress Package, aka EDK, is an open up source implementation of the Unified Extensible Firmware Interface (UEFI), which capabilities as an interface between the operating method and the firmware embedded in the device’s components.
The firmware growth surroundings, which is in its next iteration (EDK II), comes with its very own cryptographic offer known as CryptoPkg that, in change, helps make use of expert services from the OpenSSL task.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
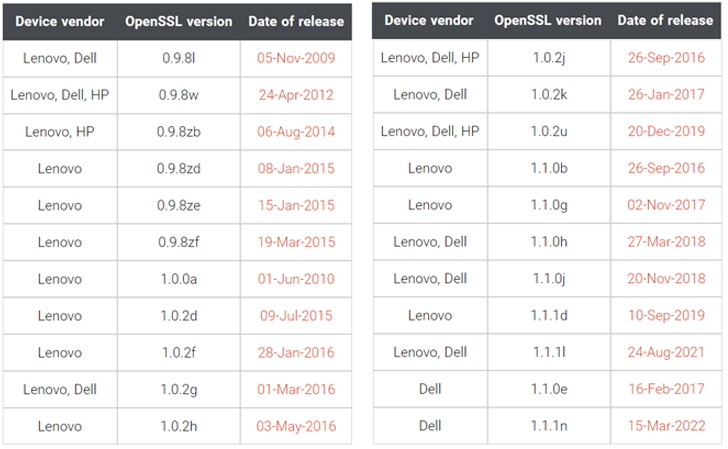
Per firmware security corporation Binarly, the firmware impression related with Lenovo Thinkpad organization equipment was observed to use 3 different versions of OpenSSL: .9.8zb, 1..0a, and 1..2j, the final of which was produced in 2018.
What is a lot more, one of the firmware modules named InfineonTpmUpdateDxe relied on OpenSSL edition .9.8zb that was transported on August 4, 2014.
“The InfineonTpmUpdateDxe module is liable for updating the firmware of Trusted System Module (TPM) on the Infineon chip,” Binarly discussed in a complex produce-up very last 7 days.
“This evidently implies the supply chain problem with 3rd-party dependencies when it looks like these dependencies by no means obtained an update, even for critical security issues.”
The variety of OpenSSL versions apart, some of the firmware offers from Lenovo and Dell used an even more mature edition (.9.8l), which arrived out on November 5, 2009. HP’s firmware code, also, used a 10-12 months-aged edition of the library (.9.8w).
The fact that the product firmware utilizes various versions of OpenSSL in the exact same binary package deal highlights how 3rd-party code dependencies can introduce additional complexities in the source chain ecosystem.
Binarly even more pointed out the weaknesses in what is referred to as a Application Invoice of Supplies (SBOM) that arises as a outcome of integrating compiled binary modules (aka closed source) in the firmware.
“We see an urgent have to have for an added layer of SBOM Validation when it arrives to compiled code to validate on the binary stage, the record of 3rd-party dependency information and facts that matches the precise SBOM furnished by the seller,” the enterprise reported.
“A ‘trust-but-verify’ strategy is the finest way to offer with SBOM failures and lower offer chain challenges.”
Found this write-up intriguing? Stick to THN on Facebook, Twitter and LinkedIn to study much more special written content we post.
Some areas of this report are sourced from:
thehackernews.com


 Experts Warn Remote Workers of Black Friday Security Threats
Experts Warn Remote Workers of Black Friday Security Threats