In what is the newest evolution of menace actors abusing respectable infrastructure for nefarious finishes, new results display that nation-point out hacking teams have entered the fray in leveraging the social system for concentrating on critical infrastructure.
Discord, in recent yrs, has grow to be a lucrative goal, performing as a fertile ground for hosting malware working with its content delivery network (CDN) as very well as allowing for facts stealers to siphon delicate details off the application and facilitating data exfiltration by means of webhooks.
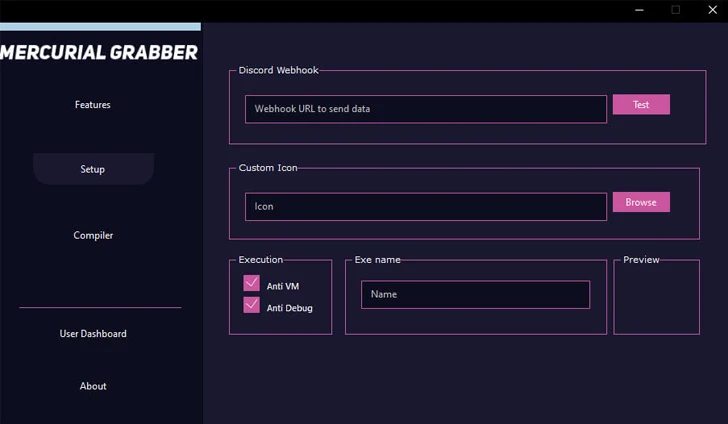
“The usage of Discord is mainly confined to data stealers and grabbers that everyone can acquire or obtain from the Internet,” Trellix researchers Ernesto Fernández Provecho and David Pastor Sanz explained in a Monday report.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

But that could be transforming, for the cybersecurity firm claimed it observed evidence of an artifact focusing on Ukrainian critical infrastructures. There is at this time no proof linking it to a identified danger group.
“”The prospective emergence of APT malware strategies exploiting Discord’s functionalities introduces a new layer of complexity to the risk landscape,” the researchers mentioned.
The sample is a Microsoft OneNote file distributed by using an email concept impersonating the non-income dobro.ua.
The file, once opened, incorporates references to Ukrainian soldiers to trick recipients into donating by clicking on a booby-trapped button, ensuing in the execution of Visual Essential Script (VBS) created to extract and run a PowerShell script in order to down load an additional PowerShell script from a GitHub repository.
For its component, in the remaining phase, PowerShell will take advantage of a Discord webhook to exfiltrate process metadata.
“The reality that the only purpose of the final payload is acquiring details about the program signifies that the marketing campaign is however in an early stage, which also suits with the usage of Discord as [command-and-control],” the scientists reported.
“Having said that, it is vital to emphasize that the actor could provide a additional advanced piece of malware to the compromised units in the long run by modifying the file saved in the GitHub repository.”

Trellix’s assessment further unveiled that loaders this kind of as SmokeLoader, PrivateLoader, and GuLoader are amid the most prevalent malware households that utilize Discord’s CDN to obtain a future-phase payload, together with stealers like RedLine, Vidar, Agent Tesla, and Umbral.
On best of that, some of the widespread malware households that have been observed employing Discord webhooks are Mercurial Grabber, Stealerium, Typhon Stealer, and Venom RAT.
“The abuse of Discord’s CDN as a distribution mechanism for further malware payloads showcases the adaptability of cybercriminals to exploit collaborative applications for their acquire,” the researchers said.
“APTs are recognized for their innovative and focused attacks, and by infiltrating extensively used conversation platforms like Discord, they can proficiently establish extended-term footholds inside networks, putting critical infrastructure and delicate info at risk.”
Discovered this report intriguing? Follow us on Twitter and LinkedIn to browse extra unique written content we article.
Some parts of this article are sourced from:
thehackernews.com


 Critical Vulnerabilities Uncovered in Open Source CasaOS Cloud Software
Critical Vulnerabilities Uncovered in Open Source CasaOS Cloud Software