A new phishing system referred to as “file archiver in the browser” can be leveraged to “emulate” a file archiver software in a web browser when a sufferer visits a .ZIP area.
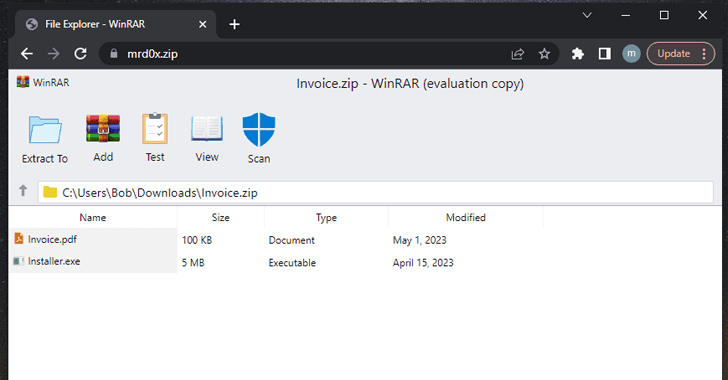
“With this phishing attack, you simulate a file archiver software package (e.g., WinRAR) in the browser and use a .zip domain to make it appear far more reputable,” security researcher mr.d0x disclosed very last 7 days.
Risk actors, in a nutshell, could create a real looking-seeking phishing landing webpage making use of HTML and CSS that mimics respectable file archive software, and host it on a .zip domain, hence elevating social engineering strategies.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
In a possible attack circumstance, a miscreant could vacation resort to this kind of trickery to redirect customers to a credential harvesting site when a file “contained” inside the bogus ZIP archive is clicked.
“Another attention-grabbing use situation is listing a non-executable file and when the consumer clicks to initiate a down load, it downloads an executable file,” mr.d0x mentioned. “Let’s say you have an ‘invoice.pdf’ file. When a user clicks on this file, it will initiate the obtain of a .exe or any other file.”
On major of that, the search bar in the Windows File Explorer can arise as a sneaky conduit where by hunting for a non-existent .ZIP file opens it instantly in the web browser really should the file title correspond to a legit .zip area.
“This is fantastic for this state of affairs considering the fact that the person would be anticipating to see a ZIP file,” the researcher stated. “Once the person performs this, it will car-start the .zip domain which has the file archive template, showing rather legitimate.”
The advancement will come as Google rolled out 8 new best-amount domains (TLDs), which include “.zip” and “.mov,” that have raised some issues that it could invite phishing and other styles of online ripoffs.
This is for the reason that .ZIP and .MOV are both equally respectable file extension names, perhaps baffling unsuspecting people into browsing a malicious internet site rather than opening a file and dupe them into unintentionally downloading malware.
“ZIP data files are frequently employed as aspect of the original phase of an attack chain, usually being downloaded immediately after a user accesses a destructive URL or opens an email attachment,” Craze Micro mentioned.
“Past ZIP archives being made use of as a payload, it is really also probably that malicious actors will use ZIP-related URLs for downloading malware with the introduction of the .zip TLD.”
Whilst reactions are decidedly mixed on the risk posed as a consequence of confusion amongst domain names and file names, it truly is anticipated to equip actors performing in terrible faith with still another vector for phishing.
The discovery also will come as cybersecurity business Group-IB explained it detected a 25% surge in the use of phishing kits in 2022, determining 3,677 exclusive kits, when in comparison to the previous yr.
Of certain curiosity is the uptick in the development of utilizing Telegram to gather stolen info, just about doubling from 5.6% in 2021 to 9.4% in 2022.
Which is not all. Phishing attacks are also starting to be extra sophisticated, with cybercriminals more and more concentrating on packing the kits with detection evasion capabilities such as the use of antibots and dynamic directories.
“Phishing operators create random web site folders that are only available by the receiver of a personalized phishing URL and are not able to be accessed with no the first url,” the Singapore-headquartered organization claimed.
“This technique permits phishers to evade detection and blacklisting as the phishing material will not expose itself.”
Future WEBINAR Zero Trust + Deception: Master How to Outsmart Attackers!
Uncover how Deception can detect state-of-the-art threats, prevent lateral motion, and enhance your Zero Belief approach. Be part of our insightful webinar!
Conserve My Seat!.advertisement-button,.ad-label,.advertisement-label:right afterexhibit:inline-block.ad_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px stable #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-major-still left-radius:25px-moz-border-radius-topleft:25px-webkit-border-bottom-appropriate-radius:25px-moz-border-radius-bottomright:25px.advert-labelfont-measurement:13pxmargin:20px 0font-body weight:600letter-spacing:.6pxcolor:#596cec.advertisement-label:afterwidth:50pxheight:6pxcontent:”border-top:2px reliable #d9deffmargin: 8px.advert-titlefont-measurement:21pxpadding:10px 0font-weight:900text-align:leftline-peak:33px.advertisement-descriptiontext-align:leftfont-sizing:15.6pxline-height:26pxmargin:5px !importantcolor:#4e6a8d.advertisement-buttonpadding:6px 12pxborder-radius:5pxbackground-shade:#4469f5font-dimension:15pxcolor:#fff!importantborder:0line-top:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-excess weight:500letter-spacing:.2px
In accordance to a new report from Notion Point, the amount of advanced phishing attacks attempted by menace actors in 2022 rose 356%. The whole number of attacks amplified by 87% more than the class of the calendar year.
This ongoing evolution of phishing strategies is exemplified by a new wave of attacks that have been noticed leveraging compromised Microsoft 365 accounts and limited-authorization message (.rpmsg) encrypted e-mail to harvest users’ credentials.
“The use of encrypted .rpmsg messages implies that the phishing material of the concept, which includes the URL inbound links, are concealed from email scanning gateways,” Trustwave scientists Phil Hay and Rodel Mendrez spelled out.
A different occasion highlighted by Proofpoint involves the attainable abuse of authentic attributes in Microsoft Groups to facilitate phishing and malware supply, which includes employing assembly invites write-up-compromise by replacing default URLs with malicious hyperlinks by using API calls.
“A various solution that attackers can use, provided obtain to a user’s Groups token, is utilizing Teams’ API or consumer interface to weaponize present one-way links in sent messages,” the enterprise security agency noted.
“This could be carried out by simply replacing benign one-way links with hyperlinks pointing to nefarious internet sites or malicious assets.”
Located this article fascinating? Abide by us on Twitter and LinkedIn to examine extra special articles we write-up.
Some components of this post are sourced from:
thehackernews.com

 PyPI Implements Mandatory Two-Factor Authentication for Project Owners
PyPI Implements Mandatory Two-Factor Authentication for Project Owners