An ongoing marketing campaign dubbed Earth Bogle is leveraging geopolitical-themed lures to produce the NjRAT remote access trojan to victims throughout the Center East and North Africa.
“The danger actor uses public cloud storage expert services this sort of as files[.]fm and failiem[.]lv to host malware, while compromised web servers distribute NjRAT,” Development Micro said in a report published Wednesday.
Phishing emails, generally customized to the victim’s passions, are loaded with malicious attachments to activate the an infection regime. This can take the sort of a Microsoft Cabinet (Cab) archive file containing a Visual Basic Script dropper to deploy the following-phase payload.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Alternatively, it is really suspected that the data files are dispersed via social media platforms these types of as Fb and Discord, in some cases even generating bogus accounts to serve adverts on internet pages impersonating reputable news outlets.
The Taxi files, hosted on cloud storage services, also masquerade as sensitive voice calls to entice the target into opening the archive, only for the VBScript to be executed, top to the retrieval of one more VBScript file that masks alone as an graphic file.
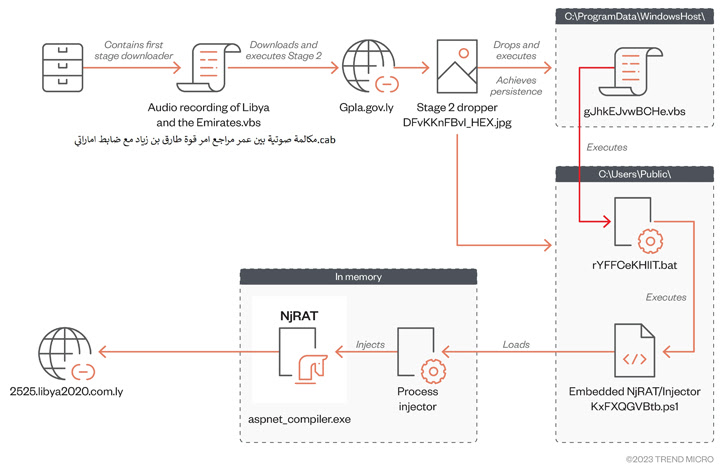
The second-stage VBScript, for its section, fetches from an presently breached area a PowerShell script that’s accountable for loading the RAT payload into memory and executing it.
NjRAT (aka Bladabindi), initially found in 2013, has myriad abilities that let the risk actor to harvest sensitive details and get handle above compromised computers.
“This case demonstrates that risk actors will leverage community cloud storage as malware file servers, combined with social engineering approaches interesting to people’s sentiments such as regional geopolitical themes as lures, to infect targeted populations,” the scientists concluded.
Found this article fascinating? Stick to us on Twitter and LinkedIn to read through additional exclusive material we write-up.
Some pieces of this article are sourced from:
thehackernews.com

 1000 Shipping Vessels Impacted by Ransomware Attack
1000 Shipping Vessels Impacted by Ransomware Attack