A new ongoing marketing campaign dubbed EleKtra-Leak has set its eyes on exposed Amazon Web Support (AWS) identity and entry management (IAM) credentials inside of public GitHub repositories to aid cryptojacking activities.
“As a final result of this, the risk actor related with the campaign was capable to generate many AWS Elastic Compute (EC2) circumstances that they employed for huge-ranging and extensive-lasting cryptojacking functions,” Palo Alto Networks Unit 42 researchers William Gamazo and Nathaniel Quist said in a technological report shared with The Hacker News.
The operation, active due to the fact at the very least December 2020, is developed to mine Monero from as a lot of as 474 exclusive Amazon EC2 instances between August 30 and Oct 6, 2023.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
A standout factor of the attacks is the automatic focusing on of AWS IAM qualifications inside 4 minutes of their initial publicity on GitHub, indicating that risk actors are programmatically cloning and scanning the repositories to capture the uncovered keys.
The adversary has also been noticed blocklisting AWS accounts that publicize IAM qualifications in what is actually possible witnessed as an work to prevent even further analysis.

There is proof to counsel that the attacker may also have been joined to a different cryptojacking campaign disclosed by Intezer in January 2021 aimed at badly secured Docker providers using the identical bespoke mining application.
Element of the campaign’s achievements lies in the exploitation of blindspots in GitHub’s solution scanning element and AWS’ AWSCompromisedKeyQuarantine plan to flag and protect against the misuse of compromised or uncovered IAM credentials to run or commence EC2 instances.
Whilst the quarantine coverage is used in just two minutes of the AWS credentials being publicly accessible on GitHub, it truly is currently being suspected that the keys are currently being uncovered by means of an as-but-undetermined process.
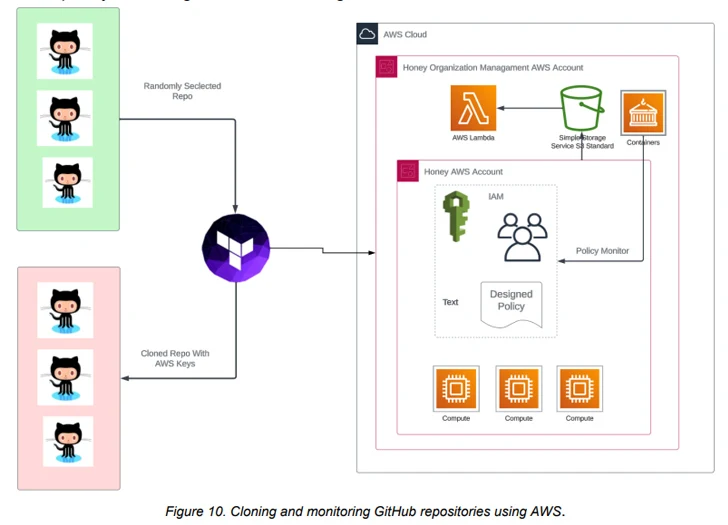
Device 42 stated that the “risk actor might be ready to uncover uncovered AWS keys that aren’t mechanically detected by AWS and subsequently management these keys outdoors of the AWSCompromisedKeyQuarantine policy.”
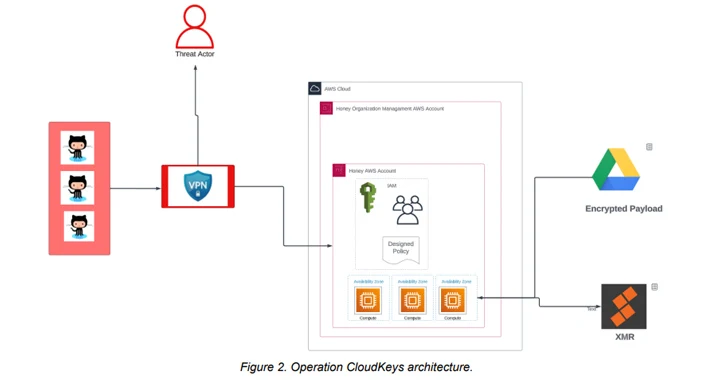
In the attack chains identified by the cybersecurity enterprise, the stolen AWS qualifications are used to perform an account reconnaissance procedure, followed by building AWS security teams and launching multiple EC2 situations throughout numerous regions from driving a virtual non-public network (VPN).
The cryptomining operations are performed on c5a.24xlarge AWS situations owing to their bigger processing ability, permitting its operators to mine more cryptocurrency in a shorter time period of time.

The mining program made use of to carry out cryptojacking is fetched from a Google Generate URL, highlighting a pattern of destructive actors leveraging the rely on affiliated with greatly used applications to fly underneath the radar.
“The sort of Amazon Machine Visuals (AMI) the danger actor made use of was also unique,” the researchers said. “The recognized illustrations or photos had been non-public and they were being not listed in the AWS Marketplace.”
To mitigate these types of attacks, businesses that accidentally expose AWS IAM qualifications are advisable to quickly revoke any API connections applying the keys, get rid of them from the GitHub repository, and audit GitHub repository cloning functions for any suspicious operations.
“The risk actor can detect and launch a entire-scale mining procedure in 5 minutes from the time of an AWS IAM credential remaining uncovered in a community GitHub repository,” the scientists stated. “Regardless of prosperous AWS quarantine insurance policies, the campaign maintains continuous fluctuation in the selection and frequency of compromised victim accounts.”
Identified this short article attention-grabbing? Adhere to us on Twitter and LinkedIn to browse much more exclusive content material we write-up.
Some elements of this article are sourced from:
thehackernews.com

 Urgent: New Security Flaws Discovered in NGINX Ingress Controller for Kubernetes
Urgent: New Security Flaws Discovered in NGINX Ingress Controller for Kubernetes