Risk actors have been observed earning use of bogus websites masquerading as reputable antivirus methods from Avast, Bitdefender, and Malwarebytes to propagate malware capable of stealing sensitive facts from Android and Windows units.
“Hosting malicious software program by web sites which glimpse reputable is predatory to standard consumers, especially those who glimpse to shield their equipment from cyber attacks,” Trellix security researcher Gurumoorthi Ramanathan reported.
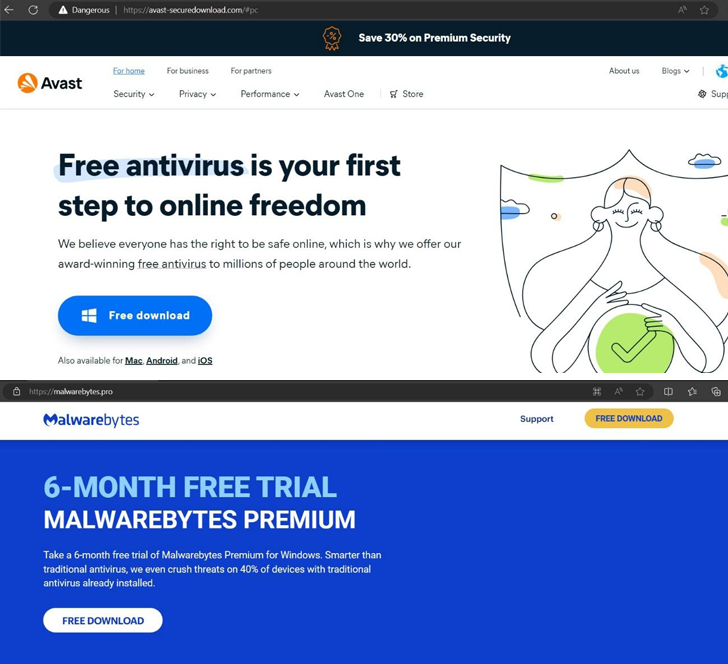
The listing of web sites is under –

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
- avast-securedownload[.]com, which is utilised to provide the SpyNote trojan in the variety of an Android deal file (“Avast.apk”) that, at the time set up, requests for intrusive permissions to read SMS messages and contact logs, set up and delete applications, consider screenshot, track place, and even mine cryptocurrency
- bitdefender-app[.]com, which is made use of to deliver a ZIP archive file (“set up-win-x86-x64.exe.zip”) that deploys the Lumma data stealer malware
- malwarebytes[.]pro, which is applied to supply a RAR archive file (“MBSetup.rar”) that deploys the StealC data stealer malware
The cybersecurity company explained it also uncovered a rogue Trellix binary named “AMCoreDat.exe” that serves as a conduit to fall a stealer malware capable of harvesting sufferer information and facts, including browser data, and exfiltrating it to a distant server.

It is really at present not obvious how these bogus sites are dispersed, but similar campaigns in the earlier have used techniques this sort of as malvertising and lookup engine optimization (Seo) poisoning.
Stealer malware have significantly become a widespread menace, with cybercriminals marketing a lot of personalized variants with varying ranges of complexity. This features new stealers like Acrid, SamsStealer, ScarletStealer, and Waltuhium Grabber, as well as updates to present ones such as SYS01stealer (aka Album Stealer or S1deload Stealer).
“The actuality that new stealers appear each individual now and then, put together with the fact that their features and sophistication varies greatly, implies that there is a criminal current market demand from customers for stealers,” Kaspersky explained in a the latest report.
The advancement comes as scientists have found out a new Android banking trojan termed Antidot that disguises by itself as a Google Enjoy update to aid information and facts theft by abusing Android’s accessibility and MediaProjection APIs.
“Performance-wise Antidot is able of keylogging, overlay attacks, SMS exfiltration, screen captures, credentials theft, gadget management, and execution of commands been given from the attackers,” Broadcom-owned Symantec claimed in a bulletin.
Uncovered this post attention-grabbing? Adhere to us on Twitter and LinkedIn to read through much more special content we write-up.
Some parts of this write-up are sourced from:
thehackernews.com


 How Do Hackers Blend In So Well? Learn Their Tricks in This Expert Webinar
How Do Hackers Blend In So Well? Learn Their Tricks in This Expert Webinar