New investigate disclosed a string of intense security vulnerabilities in the ‘Find My Mobile’—an Android app that arrives pre-mounted on most Samsung smartphones—that could have permitted distant attackers to observe victims’ serious-time location, watch phone phone calls, and messages, and even delete facts saved on the phone.
Portugal-primarily based cybersecurity products and services service provider Char49 exposed its results on Samsung’s Obtain My Mobile Android application at the DEF CON convention previous week and shared particulars with the Hacker News.
“This flaw, right after set up, can be effortlessly exploited and with severe implications for the person and with a probably catastrophic affect: everlasting denial of assistance by way of phone lock, complete details reduction with manufacturing facility reset (SD card included), critical privateness implication via IMEI and locale monitoring as nicely as connect with and SMS log access,” Char49’s Pedro Umbelino claimed in technological analysis.
The flaws, which work on unpatched Samsung Galaxy S7, S8, and S9+ units, have been addressed by Samsung immediately after flagging the exploit as a “large effect vulnerability.”
Samsung’s Come across My Cell assistance permits owners of Samsung gadgets to remotely track down or lock their smartphone or tablet, again up details stored on the gadgets to Samsung Cloud, wipe local knowledge, and block entry to Samsung Pay out.
In accordance to Char49, there had been four different vulnerabilities in the app that could have been exploited by a destructive application set up on the qualified product, so generating a guy-in-the-disk attack to hijack interaction from the backend servers and snoop on the target.
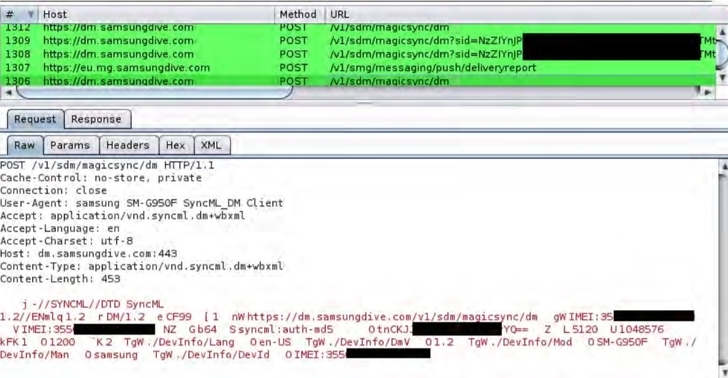
The flaw stems from the actuality the application checks for the existence of a distinct file on the device’s SD card (“/mnt/sdcard/fmm.prop”) in get to load a URL (“mg.URL”), thus enabling a rogue application to produce this file that can be used by a bad actor to possibly hijack the communications with the server.
“By pointing the MG URL to an attacker-managed server and forcing the registration, the attacker can get several specifics about the consumer: coarse location through the IP deal with, IMEI, product manufacturer, API degree, backup applications, and a number of other facts,” Umbelino claimed.
To obtain this, a malicious app mounted on the device tends to make use of an exploit chain that leverages two different unprotected broadcast receivers to redirect commands despatched to Samsung’s servers from the Find My Mobile app to a distinctive server which is beneath the attacker’s manage and execute destructive commands.
The destructive server also forwards the ask for to the legitimate server and retrieves the response, but not in advance of injecting its individual commands in the server responses.
In executing so, a thriving assault could allow a hacker to observe the device’s spot, seize contact information and text messages for spying, lock the phone for ransom, and erase all knowledge by means of a factory reset.
Unnecessary to say, the vulnerability is however yet another indicator of how an app that’s meant to safeguard consumers versus information and facts decline can be prone to a amount of flaws that can defeat the app’s goal.
“The FMM [Find My Mobile] software ought to not have arbitrary components publicly readily available and in an exported point out,” Umbelino said. “If totally vital, for example if other offers simply call these elements, then they must be guarded with suitable permissions. Testing code that relies on the existence of documents in public areas really should be removed.”
Uncovered this article interesting? Comply with THN on Facebook, Twitter and LinkedIn to study much more special content we post.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount


 Law enforcement Use of Facial Recognition Ruled Illegal in Environment First Case
Law enforcement Use of Facial Recognition Ruled Illegal in Environment First Case