GitHub on Wednesday introduced that it really is earning out there a characteristic termed code scanning autofix in community beta for all Highly developed Security clients to supply qualified recommendations in an work to keep away from introducing new security issues.
“Run by GitHub Copilot and CodeQL, code scanning autofix covers more than 90% of alert kinds in JavaScript, Typescript, Java, and Python, and delivers code recommendations demonstrated to remediate extra than two-thirds of identified vulnerabilities with minor or no enhancing,” GitHub’s Pierre Tempel and Eric Tooley mentioned.
The capacity, very first previewed in November 2023, leverages a blend of CodeQL, Copilot APIs, and OpenAI GPT-4 to generate code recommendations. The Microsoft-owned subsidiary also stated it plans to insert help for extra programming languages, which includes C# and Go, in the foreseeable future.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
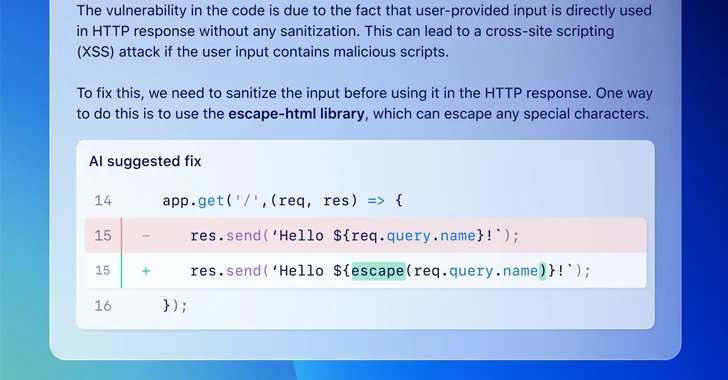
Code scanning autofix is built to aid developers repair vulnerabilities as they code by creating prospective fixes as nicely as providing a organic language explanation when an issue is discovered in a supported language.

These strategies could go outside of the existing file to incorporate adjustments to several other data files and the dependencies that must be included to rectify the trouble.
“Code scanning autofix lowers the barrier of entry to developers by combining information on very best techniques with facts of the codebase and warn to advise a likely repair to the developer,” the corporation claimed.
“As a substitute of starting off with a research for facts about the vulnerability, the developer starts off with a code recommendation that demonstrates a potential alternative for their codebase.”
That explained, it truly is remaining to the developer to evaluate the tips and ascertain if it truly is the right remedy and guarantee that it does not deviate from its intended actions.
GitHub also emphasized the latest limitations of the autofix code solutions, producing it critical that developers meticulously critique the alterations and the dependencies just before accepting them –
- Suggest fixes that are not syntactically correct code alterations
- Advise fixes that are syntactically correct code but are prompt at the incorrect site
- Advise fixes that are syntactically legitimate but that modify the semantics of the software
- Propose fixes that are are unsuccessful to address the root cause, or introduce new vulnerabilities
- Suggest fixes that only partially resolve the underlying flaw
- Suggest unsupported or insecure dependencies
- Advise arbitrary dependencies, main to feasible source chain attacks
“The technique has incomplete understanding of the dependencies revealed in the wider ecosystem,” the corporation mentioned. “This can direct to ideas that incorporate a new dependency on malicious application that attackers have released below a statistically possible dependency identify.”
Uncovered this posting appealing? Observe us on Twitter and LinkedIn to browse additional unique information we write-up.
Some elements of this article are sourced from:
thehackernews.com

 Making Sense of Operational Technology Attacks: The Past, Present, and Future
Making Sense of Operational Technology Attacks: The Past, Present, and Future