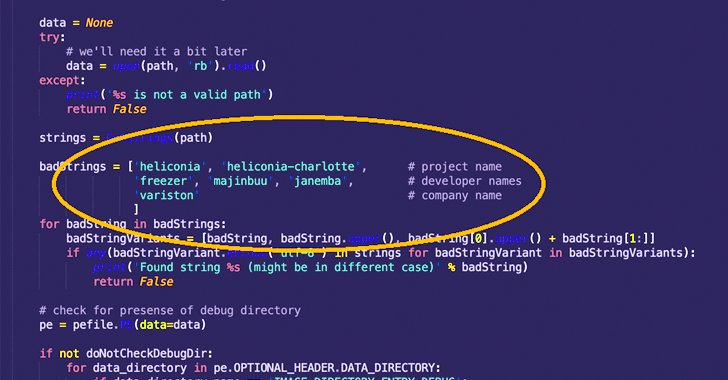
A Barcelona-primarily based surveillanceware seller named Variston IT is mentioned to have surreptitiously planted spy ware on targeted units by exploiting quite a few zero-working day flaws in Google Chrome, Mozilla Firefox, and Windows, some of which day back to December 2018.
“Their Heliconia framework exploits n-working day vulnerabilities in Chrome, Firefox, and Microsoft Defender, and provides all the resources needed to deploy a payload to a concentrate on unit,” Google Danger Examination Team (TAG) scientists Clement Lecigne and Benoit Sevens explained in a write-up.
Variston, which has a bare-bones web site, claims to “give tailor built Facts Security Methods to our clients,” “layout tailor made security patches for any variety of proprietary process,” and aid the “the discovery of digital details by [law enforcement agencies],” among other providers.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The vulnerabilities, which have been patched by Google, Microsoft, and Mozilla in 2021 and early 2022, are considered to have been used as zero-days to aid prospects put in malware of their alternative on the specific techniques.

Heliconia comprises a trio of elements, particularly Noise, Soft, and Documents, each and every of which are responsible for deploying exploits versus bugs in Chrome, Windows, and Firefox, respectively.
Sounds is developed to acquire benefit of a security flaw in the Chrome V8 motor JavaScript motor that was patched in August 2021 as well as an unfamiliar sandbox escape approach termed “chrome-sbx-gen” to help the final payload (aka “agent”) to be set up on targeted units.
On the other hand, the attack banking companies on the prerequisite that the sufferer accesses a booby-trapped webpage to bring about the to start with-phase exploit.
Heliconia Sound can be furthermore configured by the purchaser making use of a JSON file to established distinctive parameters like the most number of occasions to provide the exploits, an expiration day for the servers, redirect URLs for non-goal people, and procedures specifying when a customer need to be regarded a valid target.
Soft is a web framework that is engineered to deliver a decoy PDF document showcasing an exploit for CVE-2021-42298, a distant code execution flaw impacting Microsoft Defender that was fixed by Redmond in November 2021. The an infection chain, in this situation, entailed the person checking out a destructive URL, which then served the weaponized PDF file.
The Files bundle – the 3rd framework – is made up of a Firefox exploit chain for Windows and Linux that leverages a use-after-absolutely free flaw in the browser that was documented in March 2022 (CVE-2022-26485). Having said that, it can be suspected that the bug was possible abused considering that at least 2019.
Google TAG said it turned mindful of the Heliconia attack framework soon after obtaining an anonymous submission to its Chrome bug reporting system. It even more mentioned that there is certainly no recent evidence of exploitation, possibly indicating the toolset has been set to relaxation or developed additional.
The enhancement arrives additional than 5 months right after the tech giant’s cybersecurity division connected a earlier unattributed Android mobile spyware, dubbed Hermit, to Italian software outfit, RCS Lab.
“The growth of the spy ware industry puts buyers at risk and will make the Internet considerably less harmless, and while surveillance technology could be lawful under national or worldwide legal guidelines, they are generally made use of in unsafe techniques to carry out digital espionage from a assortment of teams,” the researchers reported.
Found this post interesting? Comply with us on Twitter and LinkedIn to read far more exceptional content material we put up.
Some sections of this posting are sourced from:
thehackernews.com

 Hackers Leak Another Set of Medibank Customer Data on the Dark Web
Hackers Leak Another Set of Medibank Customer Data on the Dark Web