Google has declared plans to increase a new element in the future version of its Chrome web browser to alert consumers when an extension they have put in has been removed from the Chrome Web Store.
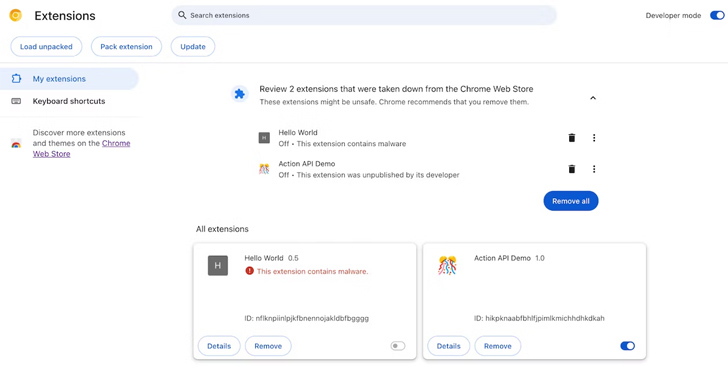
The characteristic, set for release together with Chrome 117, allows consumers to be notified when an incorporate-on has been unpublished by a developer, taken down for violating Chrome Web Store plan, or marked as malware.
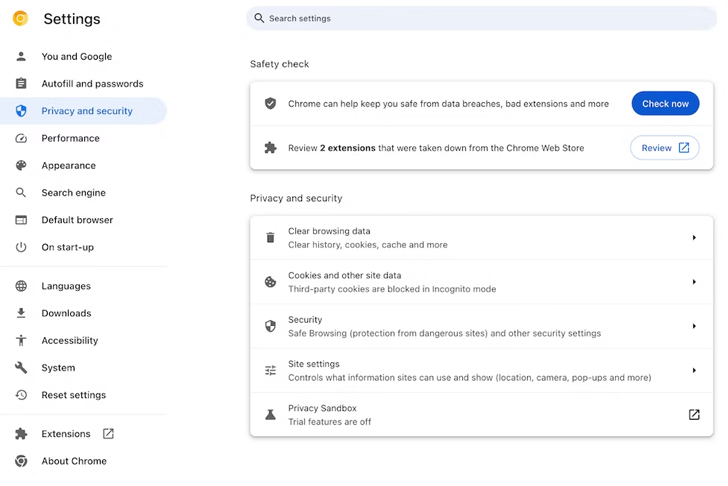
The tech big stated it intends to highlight these types of extensions under a “Basic safety test” class in the “Privacy and security” part of the browser configurations web site.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“When a consumer clicks ‘Review,’ they will be taken to their extensions and given the preference to both take out the extension or hide the warning if they wish to keep the extension installed,” Oliver Dunk, a developer relations engineer for Chrome extensions, said.

“As in preceding variations of Chrome, extensions marked as malware are mechanically disabled.”
The growth arrives as the enterprise said it is likely to immediately enhance all https:// URL navigations to https:// even when users click on on a website link that explicitly declares https://. The characteristic is at present staying examined in Chrome 115, and is expected to be rolled out quickly.
Google also mentioned it will also present a warning starting off in mid-September 2023 when users endeavor to download superior-risk data files when on an insecure link.
“Downloaded data files can consist of destructive code that bypasses Chrome’s sandbox and other protections, so a network attacker has a exceptional option to compromise your laptop when insecure downloads materialize,” the Chromium workforce reported.

“Until HTTPS-Very first Method is enabled, Chrome will not demonstrate warnings when insecurely downloading data files like photographs, audio, or movie, as these file varieties are rather safe.”
Some of the other features that are in the pipeline incorporate enabling HTTPS-1st Method by default in Incognito Manner for a additional protected browsing practical experience and mechanically turning the setting on for customers who seldom use HTTP.
End users can empower HTTPS-Initial Mode by enabling “Constantly use secure connections” in Chrome security settings (chrome://options/security).
The updates also abide by Google’s proposals to increase help for quantum-resistant encryption algorithms in the Chrome browser, beginning with edition 116.
Discovered this posting exciting? Abide by us on Twitter and LinkedIn to read more special material we write-up.
Some sections of this posting are sourced from:
thehackernews.com

 NoFilter Attack: Sneaky Privilege Escalation Method Bypasses Windows Security
NoFilter Attack: Sneaky Privilege Escalation Method Bypasses Windows Security