Elite hackers linked with Russia’s armed service intelligence company have been joined to significant-volume phishing strategies aimed at hundreds of users in Ukraine to extract intelligence and affect general public discourse connected to the war.
Google’s Threat Analysis Group (TAG), which is monitoring the actions of the actor less than the identify FROZENLAKE, stated the attacks carry on the “group’s 2022 target on targeting webmail users in Eastern Europe.”
The state-sponsored cyber actor, also tracked as APT28, Fancy Bear, Forest Blizzard, Iron Twilight, Sednit, and Sofacy, is both extremely active and proficient. It has been lively considering that at minimum 2009, targeting media, governments, and navy entities for espionage.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The most recent intrusion established, starting off in early February 2023, included the use of reflected cross-web site scripting (XSS) attacks in numerous Ukrainian govt web-sites to redirect consumers to phishing domains and capture their credentials.
The disclosure comes as U.K. and U.S. intelligence and legislation enforcement agencies introduced a joint advisory warning of APT28’s attacks exploiting an previous, identified vulnerability in Cisco routers to deploy malware acknowledged as Jaguar Tooth.
FROZENLAKE is far from the only actor targeted on Ukraine considering that Russia’s military services invasion of the place over a yr back. A different notable adversarial collective is FROZENBARENTS – aka Sandworm, Seashell Blizzard (née Iridium), or Voodoo Bear – which has engaged in a sustained effort and hard work to focus on companies affiliated to the Caspian Pipeline Consortium (CPC) and other electricity sector entities in Eastern Europe.
The two teams have been attributed to the Standard Team Main Intelligence Directorate (GRU), with APT28 tied to the 85th Particular Assistance Middle (GTsSS) armed service intelligence unit 26165. Sandworm, on the other hand, is thought to be aspect of GRU’s Device 74455.
The credential harvesting marketing campaign qualified CPC staff members with phishing inbound links sent through SMS. The attacks from the electrical power vertical distributed hyperlinks to bogus Windows update offers that finally executed an facts stealer identified as Rhadamanthys to exfiltrate passwords and browser cookies.
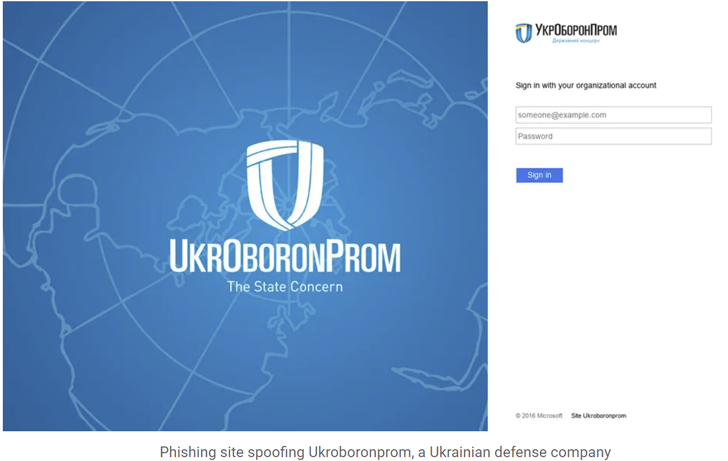
FROZENBARENTS, dubbed the “most versatile GRU cyber actor,” has also been noticed launching credential phishing attacks focusing on the Ukrainian protection industry, armed forces, and Ukr.net webmail buyers beginning in early December 2022.
Approaching WEBINARMaster the Art of Dark Web Intelligence Accumulating
Find out the art of extracting threat intelligence from the dark web – Join this qualified-led webinar!
Preserve My Seat!
The risk actor is explained to have more established on line personas throughout YouTube, Telegram, and Instagram to disseminate pro-Russian narratives, leak info stolen from compromised corporations, and post targets for dispersed denial-of-company (DDoS) attacks.
“FROZENBARENTS has qualified end users involved with well-known channels on Telegram,” TAG researcher Billy Leonard explained. “Phishing strategies sent through email and SMS spoofed Telegram to steal credentials, often concentrating on consumers pursuing pro-Russia channels.”
A 3rd risk actor of interest is PUSHCHA (aka Ghostwriter or UNC1151), a Belarusian authorities-backed group that’s recognized to act on behalf of Russian pursuits, its focused phishing attacks singling out Ukrainian webmail suppliers this kind of as i.ua and meta.ua to siphon credentials.
Google TAG also highlighted a set of attacks mounted by the team at the rear of Cuba ransomware to deploy RomCom RAT in the Ukrainian government and military services networks.
“This represents a substantial change from this actor’s classic ransomware functions, behaving far more in the same way to an actor conducting functions for intelligence assortment,” Leonard pointed out.
Discovered this short article appealing? Comply with us on Twitter and LinkedIn to study a lot more exceptional material we article.
Some sections of this post are sourced from:
thehackernews.com


 Nurse Call Systems, Infusion Pumps Riskiest Connected Medical Devices
Nurse Call Systems, Infusion Pumps Riskiest Connected Medical Devices