A zero-day flaw in a WordPress plugin referred to as BackupBuddy is becoming actively exploited, WordPress security business Wordfence has disclosed.
“This vulnerability can make it feasible for unauthenticated end users to download arbitrary information from the influenced web-site which can involve sensitive info,” it stated.
BackupBuddy lets customers to back up their total WordPress installation from in the dashboard, including concept data files, webpages, posts, widgets, people, and media documents, among some others.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

The plugin is estimated to have about 140,000 lively installations, with the flaw (CVE-2022-31474, CVSS score: 7.5) impacting versions 8.5.8. to 8.7.4.1. It truly is been dealt with in variation 8.7.5 produced on September 2, 2022.
The issue is rooted in the perform referred to as “Regional Directory Duplicate” that is designed to retailer a regional copy of the backups. In accordance to Wordfence, the vulnerability is the final result of the insecure implementation, which allows an unauthenticated danger actor to obtain any arbitrary file on the server.
Extra details about the flaw have been withheld in light of lively in-the-wild abuse and its ease of exploitation.
“This vulnerability could let an attacker to check out the contents of any file on your server that can be go through by your WordPress set up,” the plugin’s developer, iThemes, explained. “This could contain the WordPress wp-config.php file and, depending on your server set up, delicate information like /and so forth/passwd.”

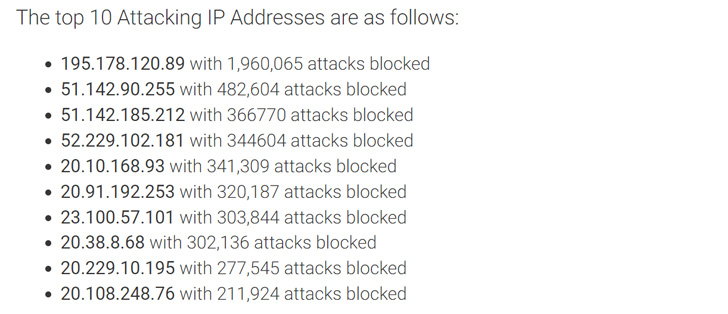
Wordfence pointed out that the concentrating on of CVE-2022-31474 commenced on August 26, 2022, and that it has blocked virtually 5 million attacks in the intervening time period. Most of the intrusions have tried to go through the below documents –
- /and so on/passwd
- /wp-config.php
- .my.cnf
- .accesshash
Consumers of the BackupBuddy plugin are recommended to up grade to the latest version. Ought to customers determine that they might have been compromised, it is really recommended to reset the databases password, alter WordPress Salts, and rotate API keys saved in wp-config.php.
Located this post appealing? Follow THN on Fb, Twitter and LinkedIn to read through extra special content we put up.
Some elements of this article are sourced from:
thehackernews.com


 Podcast transcript: Are phishing tests a waste of time?
Podcast transcript: Are phishing tests a waste of time?